Key Findings – 2
The Bandwidth of DDoS attacks in 5G Environments Grew Steadily. Small and Medium-sized Attacks Overtook Small Attacks to Become the Mainstream
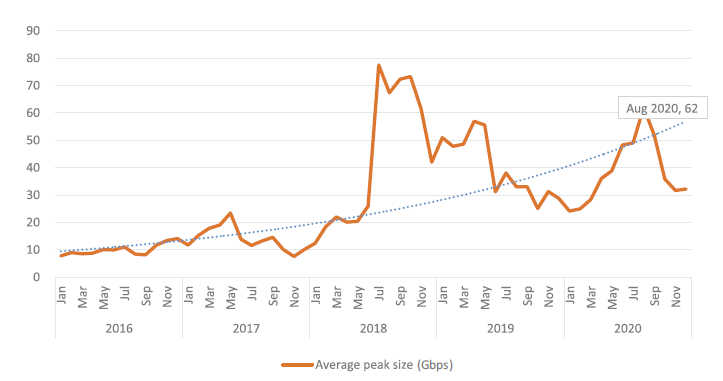
Over the five-year period from 2016 to 2020, the average peak size of DDoS attacks rose to a new level since the latter half of 2018 despite obvious fluctuations.
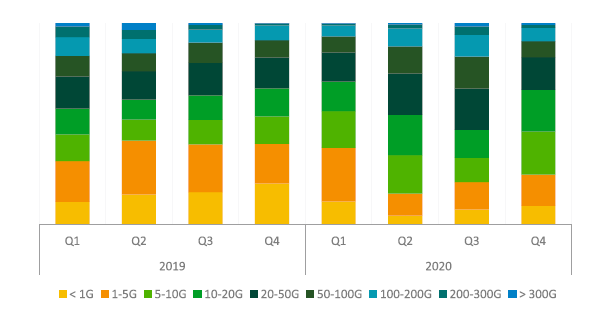
Of all DDoS attacks, 18.16% peaked at 5 – 10 Gbps, making up the largest proportion. In 2019, attacks peaking at 1 – 5 Gbps dominated. In 2020, attacks peaking at 5 – 50 Gbps were distributed evenly and accounted for 53.07% of the total DDoS attacks, but the proportion of small attacks peaking below 5 Gbps dropped. It in large part because of using of 5G networks which not only increase the available bandwidth for devices but also bring challenges to DDoS attack protection and mitigation when the benefit is used by attackers to launch DDoS attacks through IoT botnets.
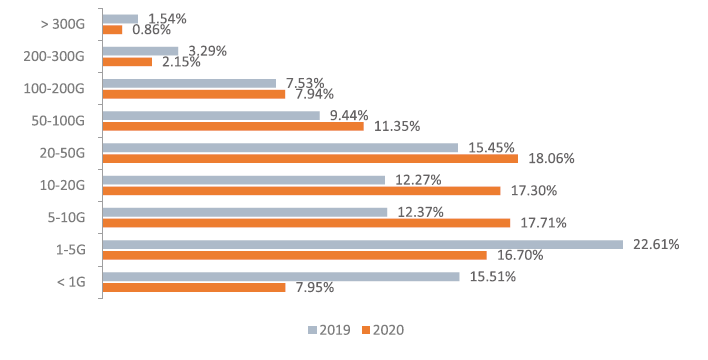
Seen from quarterly statistics of 2020, small DDoS attacks peaking below 5 Gbps decreased obviously, and attacks whose peak size ranged from 5 – 50 Gbps kept increasing and reached 58.4% in Q4. The proportion and the number of volumetric attacks peaking above 300 Gbps both decreased. By December 2020, there had been 1194 such attacks, 58.97% lower than the figure (2910) in 2019. The proportion also dropped from 1.54% in 2019 to 0.86%. This trend reflects the capacity of ordinary hackers, who are capable of launching low-volume attacks that are difficult to protect against, but are incapable of launching high-volume attacks, which require sophisticated skills.
Key Findings – 3
New Types of Reflection Attacks Emerged Constantly with Increasing DDoS Reflection Attacks and Reflectors
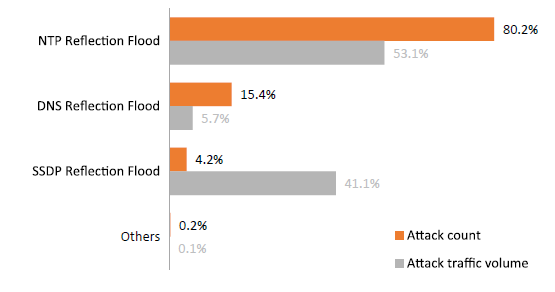
In 2020, reflection attacks made up 34% of all DDoS attacks. Compared with 2019, the number of reflection attacks increased significantly, and so did the proportion. In this year, NTP (Network Time Protocol) reflection, DNS (Domain Name System) reflection, and SSDP (Simple Service Discovery Protocol) reflection attacks stood out among all reflection attacks. To be more specific, NTP reflection attacks made up the largest proportion in both the number (80%) and traffic volume (53%).
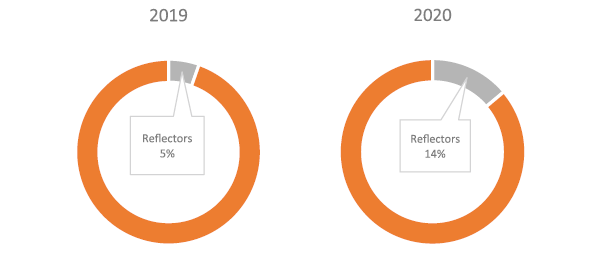
From the attack source type, the proportion of reflectors increased to 14%. Most reflectors are IoT devices. With the fast growth of the 5G technology and IoT, more and more IoT devices are connecting to the network at a faster speed. In contrast to conventional volumetric attack traffic from single IP address, the low-and-slow attack is on the rise by leveraging a wealth of IoT devices. In such attacks, the frequency of packets from each IP address imitate that of packets from legitimate users to evade protection policies that are based on geolocations and rate limiting. To mitigate these attacks, multidimensional detection algorithms have to be used to distinguish between attack sources and normal users.
In February 2020, Amazon Web Services (AWS) said that it suffered a massive DDoS attack of 2.3 Tbps, in contrast to the previous record of 1.7 Tbps in 2018. Through CLDAP (Connection-less Lightweight Directory Access Protocol) reflection, this attack on AWS lasted three days.
In October 2020, Google revealed that, as early as three years ago (2017), it was targeted by a DDoS attack of 2.54 Tbps, which changed the previously perceived record of 1.7 Tbps. This attack also exploited CLDAP, DNS, and SMTP (Simple Mail Transfer Protocol) servers on the Internet to reflect traffic. Data shows that reflection attacks are still dominant in bandwidth consumed DDoS attacks and participated in a lot of renowned volumetric DDoS attacks.
Today, reflection attacks are still changing and evolving, from the first NTP and SSDP attacks to TCP reflection and Memcached erupted in the last two years. Reflection attacks are not difficult to defend against. But just as attack tactics get better, so must defense strategies. As for mitigation devices, NSFOCUS Anti-DDoS System (ADS) is a good choice as it can effectively detect and protect against various known and unknown reflection attacks.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.