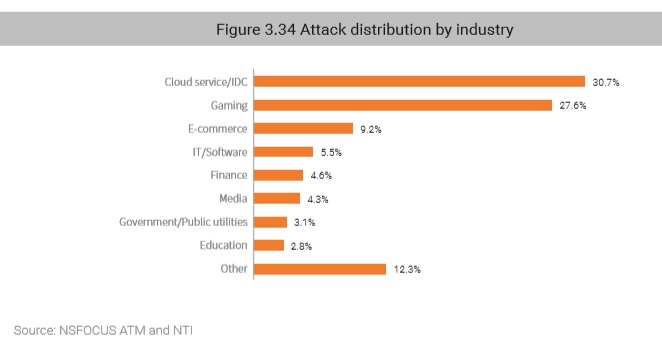
3.6Â Industrial Distribution of Attack Targets
From an industry perspective, cloud service/Internet data center (IDC), gaming, and e-commerce are top 3 industries suffering the most DDoS attacks.
Gaming and e-commerce industries are most favored by attackers for DDoS attacks because they have high requirements for prompt data processing and business continuity, must face fierce competitions with peers, boast volumetric traffic every day, and have good financial liquidity. Generally, hired by a vicious competitor, attackers make profits by launching attacks against other competitors. The competitor aims to seize resources by degrading the quality of service of their counterparts. These are also top criteria for identifying ransom targets.
3.7Â Geographic Distribution of DDoS Attacks
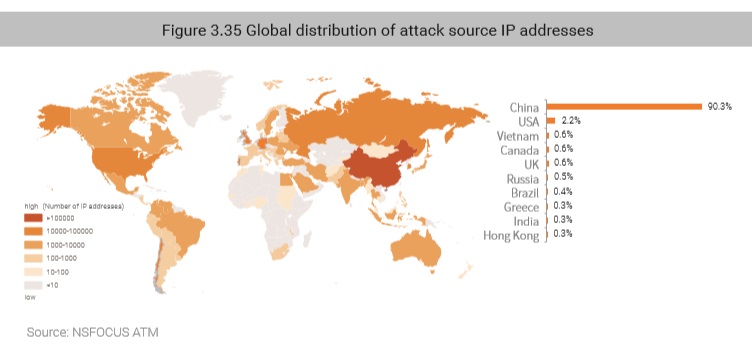
3.7.1 Controlled DDoS Attack Sources
Controlled DDoS attack sources are not necessarily members of botnets but are definitely under some type of malicious remote control. China still hosted the most controlled DDoS attack sources (90%) in 2018, followed by the USA and Vietnam.
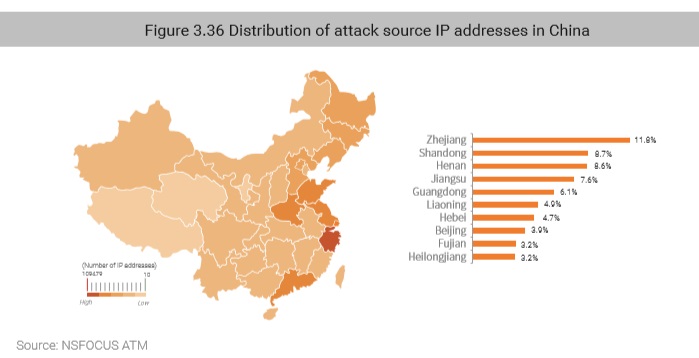
In 2018, Zhejiang, Shandong, and Henan were top 3 Chinese provinces hosting the most controlled attack sources.
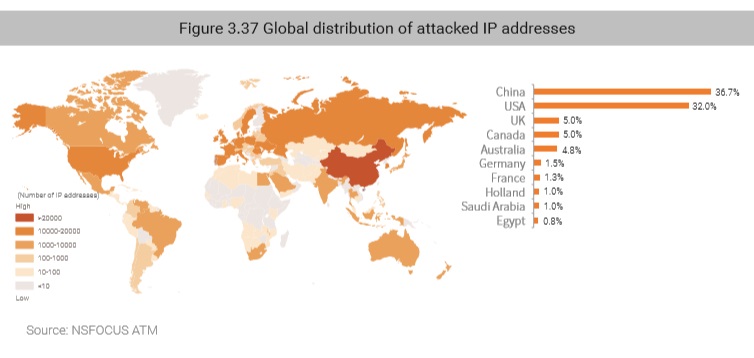
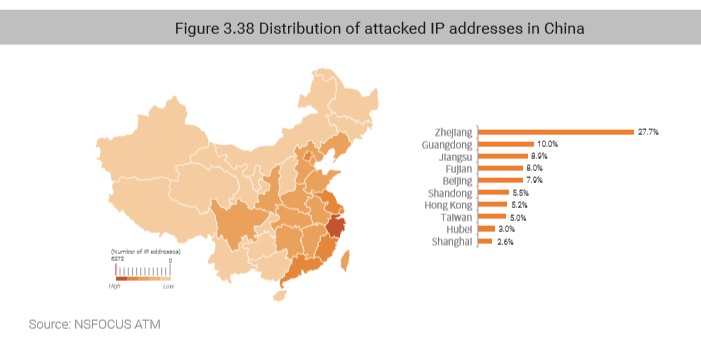
3.7.2 DDoS Attack Targets
In 2018, China was the most severely attacked country, seeing 36% of total worldwide attacks, followed by the USA (32%).
In China, Zhejiang was the most severely attacked province, followed by Guangdong, Jiangsu, Fujian, and Beijing. China’s eastern coastal areas have always been the most favored targets of DDoS attacks, again likely due to their economic prosperity.
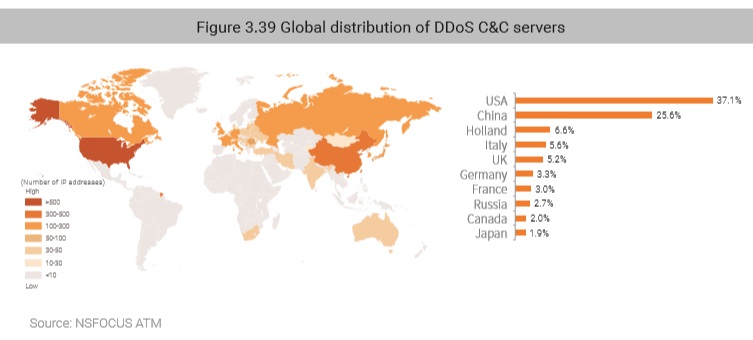
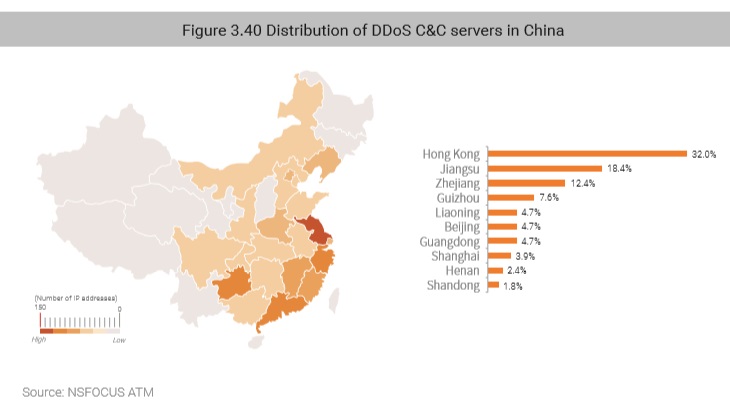
3.7.3 DDoS Command & Control Servers
Globally, the USA, China, and Holland were top 3 countries with the most IP addresses of the DDoS command & control (C&C) servers, making up 70% of the world’s total.
In China, Hong Kong, Jiangsu, and Zhejiang ranked top 3, occupying over 60% of traceable DDoS C&C servers in China.
to be continued