-
Exploit Disclosure
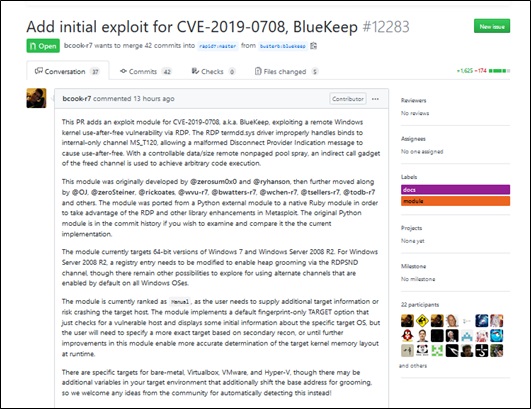
In the early morning of September 7, Beijing time, a developer disclosed a Metasploit exploit module for the Windows remote desktop services remote code execution vulnerability (CVE-2019-0708) on GitHub. The initial public exploit module (BlueKeep) for the CVE-2019-0708 vulnerability could cause old versions of Windows (Windows 7 SP1 x64 and Windows 2008 R2 x64) to execute code remotely without user interaction. This vulnerability, like WannaCry, will propagate widely, having constituted security threats in the wild.
The test shows that this exploit can be successfully used. By default, the BlueKeep module of Metasploit only checks whether the target and its operating system version are vulnerable. Currently, instead of launching attacks automatically, this exploit requires users to manually configure target details prior to further exploitation. If the module does not provide proper configuration parameters during exploitation, this could lead to the blue screen of death (BSoD) to the target host. Currently, hackers have scanned vulnerable devices on a large scale, possibly hitting vulnerable hosts in batches. Therefore, users are strongly recommended to check their assets and immediately download patches for affected devices or take other measures to avoid related threats.
Reference links:
https://github.com/rapid7/metasploit-framework/pull/12283?from=timeline&isappinstalled=0
https://github.com/rapid7/metasploit-framework/pull/12283/files
-
Vulnerability Description
On April 15, Beijing time, Microsoft released May 2019 security patches that fix 82 vulnerabilities, among which the Windows operating system remote desktop services vulnerability (CVE-2019-0708) poses serious threats. Attackers could exploit this vulnerability to cause remote code execution or worm attacks by sending a malicious request to the target via the RDP protocol.
Considering the high risk level of this vulnerability, Microsoft has also released security updates to fix this vulnerability in versions for which official support is no longer available to fix this vulnerability. Currently, the exploit of this vulnerability has been made public, and therefore affected users are advised to download and install patches as soon as possible.
Reference links:
https://support.microsoft.com/en-ca/help/4500705/customer-guidance-for-cve-2019-0708
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0708
-
Scope of Impact
Affected Versions
- Windows 7 for 32-bit Systems Service Pack 1
- Windows 7 for x64-based Systems Service Pack1
- Windows Server 2008 for 32-bit SystemsService Pack 2
- Windows Server 2008 for 32-bit SystemsService Pack 2 (Server Core installation)
- Windows Server 2008 for Itanium-Based SystemsService Pack 2
- Windows Server 2008 for x64-based SystemsService Pack 2
- Windows Server 2008 for x64-based SystemsService Pack 2 (Server Core installation)
- Windows Server 2008 R2 for Itanium-BasedSystems Service Pack 1
- Windows Server 2008 R2 for x64-based SystemsService Pack 1
- Windows Server 2008 R2 for x64-based SystemsService Pack 1 (Server Core installation)
- Windows Server 2003 SP2 x86 (official support no longer available)
- Windows Server 2003 x64 Edition SP2 (official support no longer available)
- Windows XP SP3 x86 (official support no longer available)
- Windows XP Professional x64 Edition SP2 (official support no longer available)
- Windows XP Embedded SP3 x86 (official support no longer available)
Unaffected Versions
- Windows 8
- Windows 10
-
Vulnerability Detection
-
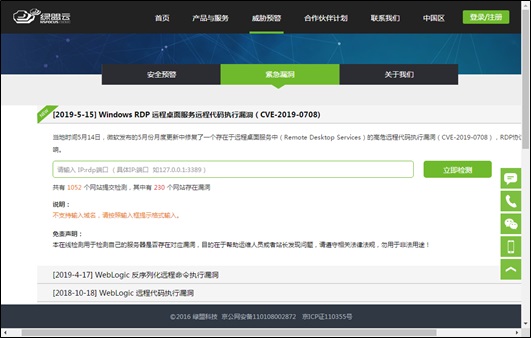
Online Detection
-
NSFOCUS Cloud provides an entry for online detection. Enterprise users can check whether their assets are vulnerable by visiting NSFOCUS Cloud.
- For a mobile device:
https://cloud.nsfocus.com/megi/holes/hole_WindowsRDP_2019_5_15.html
- For a PC:
https://cloud.nsfocus.com/#/secwarning/secwarning_news
-
Check by Our Product
NSFOCUS Remote Security Assessment System (RSAS) has provided thorough scan rules for this vulnerability. The following table lists rule upgrade package details.
| Â | Version | Upgrade Package Download Link |
| RSAS V6 system plug-in package | V6.0R02F01.1411 | http://update.nsfocus.com/update/downloads/id/28802 |
| RSAS V5 system plug-in package | 051840 | http://update.nsfocus.com/update/downloads/id/28822 |
For how to configure NSFOCUS RSAS, click the following link:
https://mp.weixin.qq.com/s/aLAWXs5DgRhNHf4WHHhQyg
-
Mitigation
-
Protection with Security Products
-
To defend against this vulnerability, NSFOCUS has released rule upgrade packages for its security products. Users are strongly recommended to upgrade to the latest rule to ensure that these security products can effectively protect against this vulnerability. The following table lists rule base versions of NSFOCUS security products.
| Product | Rule Base Version | Upgrade Package Download Link | Rule ID |
| NIPS | 5.6.10.20340 | http://update.nsfocus.com/update/downloads/id/28804 | [24489] |
| 5.6.9.20340 | http://update.nsfocus.com/update/downloads/id/28803 | ||
| 5.6.8.778 | http://update.nsfocus.com/update/downloads/id/28794 | ||
| NF | 6.0.1.778 | http://update.nsfocus.com/update/downloads/id/28828 |
For how to upgrade product rules, click the following links:
NIPS: https://mp.weixin.qq.com/s/JsRktENQNj1TdZSU62N0Ww
NF: https://mp.weixin.qq.com/s/bggqcm9VqHiPnfV1XoNuDQ
Microsoft has released security updates for all affected products (including versions for which official support is no longer available) to fix these vulnerabilities. Affected users are advised to download and install them as soon as possible. There are three methods to obtain and install patches: intranet WSUS, Microsoft Update service available on Microsoft’s official website, and offline installation.
Note: To immediately start Windows Update, users can type wuauclt.exe /detectnow at the command line prompt.
Method 1: intranet WSUS
Applicability: This method is applicable to computers that are in the Active Directory domain where the WSUS server is available, or computers that have access to the intranet WSUS service.
The system automatically downloads new security patches in a regular manner and prompts users to install them. What users need to do is install these patches as prompted.
To make a patch take effect immediately, users can restart their computers as soon as the installation is complete.
Method 2: Microsoft Update service available on Microsoft’s official website
Applicability: This method is applicable to computers that can connect to the Internet, but have no access to the intranet WSUS service, including those with the intranet WSUS service disabled and those that have this service enabled, but have no access to the intranet.
If the intranet WSUS service is not enabled on computers, users should first enable it and then install patches and restart the computer as prompted.
If computers have the intranet WSUS service enabled, but do not connect to the intranet, users should do as follows: Choose Start > All Programs > Windows Update, click Check online for updates from Microsoft Update, and then do as prompted.
Method 3: offline installation
With this method, users need to first download the latest patch for the current system, and then double-click the installation package to install it. For download links, see appendix A “Official Patch Download Link.”
-
Workarounds
If users cannot install patches for the time being, they can adopt the following temporary measures to protect against these vulnerabilities:
- If RDP is unnecessary, disable the service.
- Configure the host firewall to block the TCP port (3389 by default) of RDP.
- Enable network-level authentication (NLA). This is applicable to Windows 7, Windows Server 2008, and Windows Server 2008 R2.
Appendix A Official Patch Download Link
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.