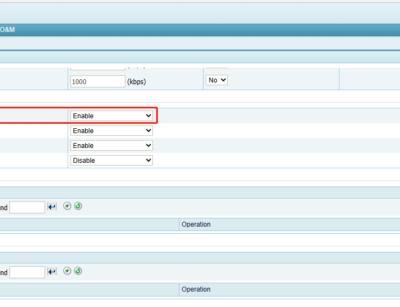
HTTP Keyword Checking is a process by which ADS controls HTTP traffic through the ADS device. In addition, ADS takes a specific action (Accept, Drop, Disconnect, Add to blacklist, Add to whitelist, or Limit rate) as configured on passing packets whose source IP address and specific fields match the HTTP...
Categoria: Knowledge Base
Path Traversal Attack Protection
A path traversal attack, or directory traversal, aims to access files and directories stored outside the web root folder. When the server does not check the user input strictly, by manipulating variables that reference files with "dot-dot-slash (../)" sequences and its variations or by using absolute file paths, it may...
Blacklist Function Optimization on ADS R90F03
ADS R90F03 refactors the blacklist function. You can configure group-specific blacklist rules, and blacklists of different groups take effect independently. Besides, you can use a global blacklist to make related rules and blocked addresses take effect for all groups. Blacklist Introduction on ADS The blacklist function in ADS before R90F03...
“Save” and “Apply” Buttons on ADS Configuration Page
When working with the ADS, it is important to understand the role of the "Apply " and "Save" buttons located in the upper-right corner of the configuration pages. Apply: Clicking the “Apply†button will apply and enforce the configuration changes, making them effective in the RAM of the ADS. These...
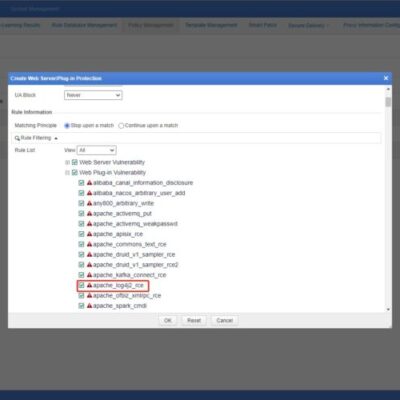
NSFOCUS WAF Log4j2_RCE Protection
Logging events is a critical aspect of software development. While there are lots of frameworks available in Java ecosystem, Log4j has been the most popular for decades, due to the flexibility and simplicity it provides. Apache Log4j is part of the Apache Logging Services, a project of the Apache Software...
Description of ADS Attack Logs: SYN Flood Logs (Part 1)
Introduction to SYN Flood A three-way handshake is required to establish a TCP connection. First, the client sends a TCP SYN packet to the server. The server responds to the client request with an SYN-ACK packet. Then the server waits and expects an ACK packet from the client. At this...