About the product
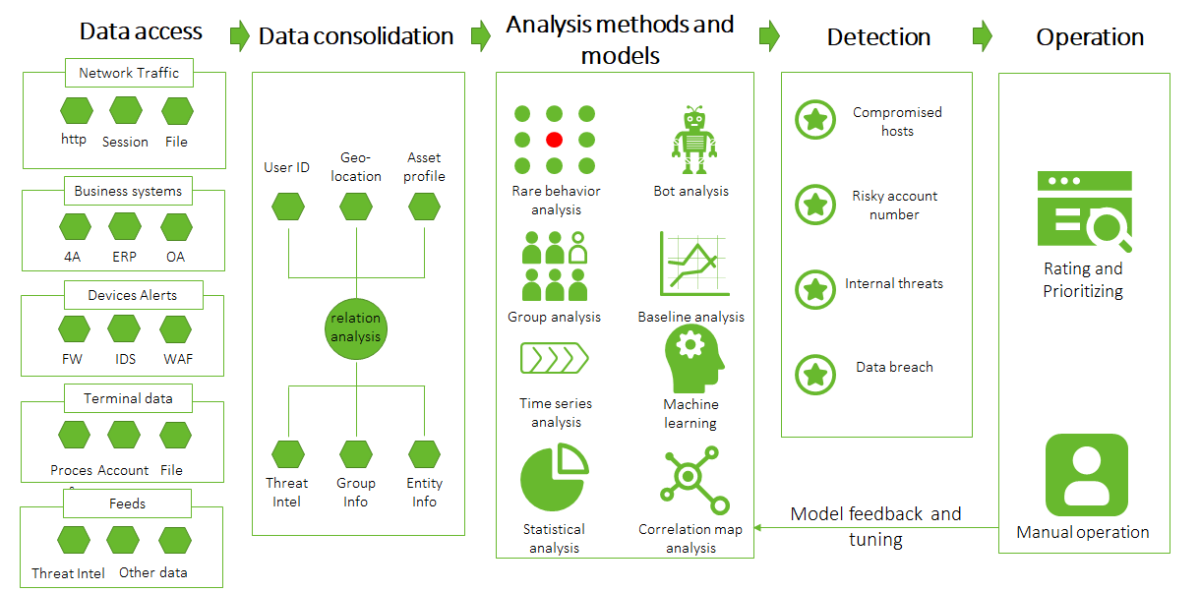
ISOP is an intelligent security operations platform widely applicable to traditional IT security scenarios. Centering on assets, the platform is built on big data to incorporate various types of data from multiple sources with the help of a threat intelligence system. It can analyze logs, traffic, anomalous behavior, vulnerabilities, and intelligence for threats.
Besides, it is powered by such technologies as scenario-based machine learning, multidimensional correlative analysis of multi-source data, automated orchestration against security incidents, and threat visualization.
Therefore, ISOP can provide customers with all-round security monitoring, real-time threat alerting, asset and vulnerability lifecycle management, and automated emergency response capabilities, helping them promptly discover, analyze, and handle security threats and implement closed-loop security management.
Key Technical Advantages of ISOP
- Open and Scalable Big Data Platform Architecture
- Asset Lifecycle management
- Risk Assessment and Prediction by the Intelligent Decision-Making Inference Engine
- Threat Determination Framework for End-to-End Threat Management
- Threat Hunting and Trackback based on Clues
- Vulnerability Risk Prioritization
- Security Orchestration, Automation, and Response (SOAR)
- User and Entity Behavior Analytics (UEBA)
- A Rich Set of Threat Intelligence
Key Application Scenarios
Flexible Access for Classified Protection Compliance
NSFOCUS ISOP receives logs concerning identity authentication, terminal security, security protection, security identification, and security audit in the live network through syslog, standardized interfaces, FTP/SFTP, and NetFlow. Also, the platform retains the logs for 180 days to obey requirements of PB-level classified protection.
All-round Asset Monitoring and Management Across the Network in Different Areas
NSFOUS ISOP surveys assets in several ways (passive discovery of logs and traffic by scanning devices and active discovery by NTI and RSAS) to gain an insight into the exposure surface, ensuring the integrity and security of IT assets.
Dynamic Defense-in-Depth
Leveraging the big data technique to aggregate data in aspects of security detection, identification, audit, protection policies, identities, and authentication, NSFOCUS ISOP, aided by endpoint detection and response (EDR) and threat hunting by honeypots, uses its built-in threat analysis modeling engine, abnormal behavior analysis engine, and security governance and analysis engine to make an in-depth association and analysis to identify known, unknown, and suspicious behaviors.
Ongoing Security Risk Assessment for Security Compliance
NSFOCUS ISOP provides integrated vulnerability management covering system/website vulnerability check, configuration baseline check, weak password check, penetration testing, and check for classified protection configurations, letting security managers know classified protection compliance check results in such dimensions of enterprises’ physical environment, communication networks, regulations, personnel, and network security system development.
Threat Situation Awareness for Cloud Tenants via Collaboration with Third-Party Cloud Management Platforms
NSFOCUS ISOP can accommodate to tenant scenarios through collaboration with cloud management platforms and control platforms. This system allows a user to view his or her own traffic data upon login with a tenant account, maintaining business continuity of public clouds and private clouds.
Visualization of Multi-layer Threat Status Data
NSFOCUS ISOP uses a visualization technique to present the network security situation from different security operation and analysis angles, helping executives stay up-to-date with the latest security trend and risks.