Part 1: Investigation Report on New APT Organization MurenShark: Torpedoes Fired to Turkish Navy [1] Characteristics of Attack Tactics Use compromised sites: MurenShark tends to use compromised sites as the file server and the C&C server in the attack process. As shown in the last chapter, the organization used the...
Author: Jie Ji
Investigation Report on New APT Organization MurenShark: Torpedoes Fired to Turkish Navy [1]
Overview In 2022 Q2, NSFOCUS Security Labs detected a series of cyberattacks against Turkey. After analysis, the researchers confirmed that this round of attacks originated from Actor210426, a new threat entity identified by NSFOCUS Security Labs in April 2021. Through the clues of behavior pattern, attack method, attack tool, attack...
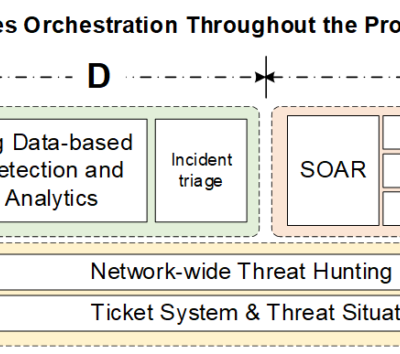
NSFOCUS ISOP Listed in The Security Analytics Platform Landscape Report
Santa Clara, Calif. August 24, 2022 – We are very happy to announce that NSFOCUS was included as one of notable vendors in the report The Security Analytics Platform Landscape, Q3 2022 published by Forrester, an authoritative international research consulting organization. “Security analytics platforms are the center of the SOCâ€, as...
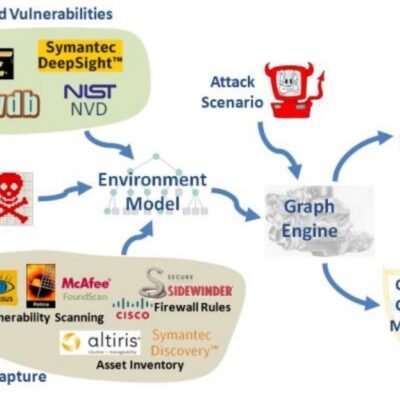
Security Knowledge Graph | Cyberspace Mapping Strengthens Tailor-Made Security
The security knowledge graph, a knowledge graph specific to the security domain, is the key to realizing cognitive intelligence in cyber security, and it also lays an indispensable technological foundation for dealing with advanced, continuous and complex threats and risks in cyberspace. NSFOCUS will publish a series of articles about...
Apache Hadoop Remote Code Execution Vulnerability (CVE-2022-25168) Alert
Overview Recently, NSFOCUS CERT found that Apache Hadoop officially fixed a command injection vulnerability. Since Apache Hadoop's FileUtil.unTar API does not escape the input filename before passing it to the shell, an attacker could exploit this vulnerability to inject arbitrary commands and thus achieve remote code execution. Affected users are...
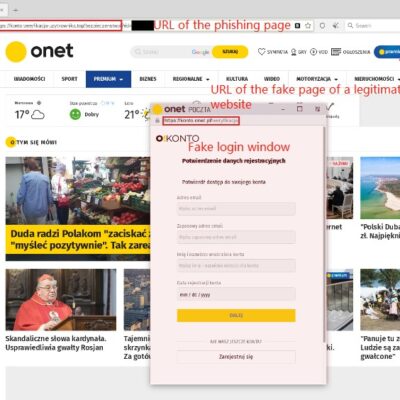
Novel Browser in the Browser (BitB) technique used by threat actor UNC 1151 for phishing attacks
Background Recently, the cyber threat actor known as UNC 1151 group was spotted to use the Browser in the Browser (BitB) technique in its campaigns. This technique is used for phishing attacks by displaying a new browser window containing a fake login panel on the visited website. The window is...