Introduction
As we indicated in the 2018 Annual IoT Security Report, network addresses on the Internet constantly change. Use of historical data to delineate exposure of assets will result in a deviation from reality, presenting a value higher than the actual number. Therefore, to accurately reflect the reality of a given area, we should specify a short period as the statistical cycle when calculating the number. This chapter starts with an analysis of the actual exposure of IoT assets in 2019.
With the booming of IoT applications and depletion of IPv4 addresses, IPv6 addresses will be gradually adopted, which is an irreversible trend. This means that IoT assets on IPv6 networks will become major targets of attackers. In this sense, it will be of great significance to cybersecurity to accurately survey IPv6 assets and services. For this reason, we also describe the methods for discovering IoT assets in IPv6 environments and analyze their exposure in this chapter.
Exposure of IPv4 IoT Assets in China
Finding 1: In 2019, a total of 1.16 million IoT assets were exposed on the Internet, the majority of which were cameras and most of which were found in Taiwan.
In November 2019, we scanned common ports used by IoT assets in China, that is, ports 554 (RTSP), 5060 (SIP), 80 (HTTP), 81 (HTTP), 443 (HTTPS), 21 (FTP), 22 (SSH), and 23 (Telnet) and discovered 1.16 million exposed IoT assets, the majority of which (560,000) were cameras. In addition, there were 280,000 routers, 260,000 VoIP phones, and 20,000 printers exposed. See Figure 2-1.

Figure 2-2 shows top 12 provinces/municipalities with the most exposed IoT assets. Obviously, Taiwan was home to the largest number of such assets, namely, 340,000 or 30% of the country’s total, four times the number in Henan province that came in second. This is largely because Taiwan has been allocated ample IPv4 addresses and a lot of assets can directly connect to the Internet without needing translation. By contrast, the Chinese mainland has far fewer IPv4 addresses than required and so has fewer IP addresses exposed on the Internet. Presumably, more IoT assets will be exposed with the wide adoption of IPv6, and so will the security risk. Therefore, monitoring the exposure of IoT assets in IPv6 environments is also a must. In section 2.4 Exposure of IPv6 IoT Assets, we will dwell upon the exposure of IPv6 assets and explain the methods used to scan such assets.

Exposure of IPv4 IoT Assets in Some Asia-Pacific Countries
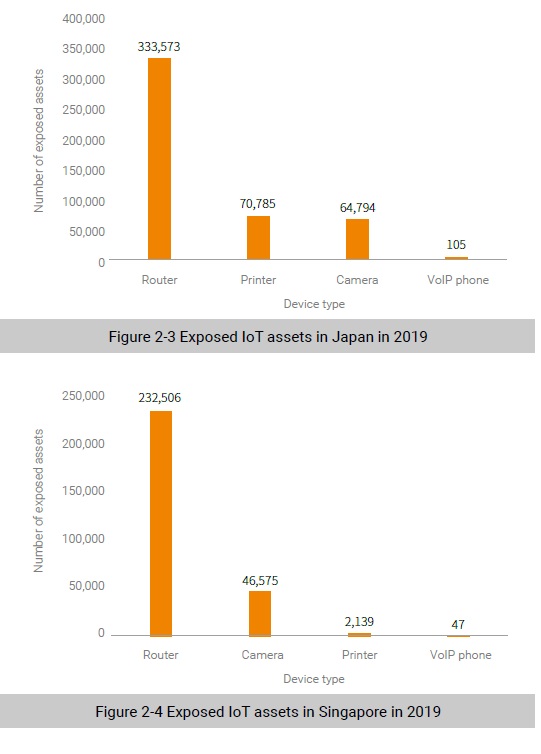
Finding 2: The total number of exposed IoT assets in Japan in 2019 did not change much from the previous year. However, the number in Singapore increased 40%, probably as a result of the Singaporean government’s wide deployment of IoT applications in the past few years.
In November 2019, we used the same method as described in section 2.2 Exposure of IPv4 IoT Assets in China to calculate the actual number of exposed IoT assets in Singapore and Japan. Figure 2-3 and Figure 2-4 show the result. In Japan, the total number of exposed IoT assets was 470,000, mainly represented by routers (333,573). Other exposed IoT assets included printers (70,785), cameras (64,794), and VoIP phones (105). See Figure 2-3. In Singapore, the total number of exposed IoT assets was 280,000, the majority of which were routers (232,506), followed by cameras (46,575), printers (2139), and VoIP phones (47), as shown in Figure 2-4.
To be continued.
