3.2Â DDoS Attack Type Analysis
3.2.1Â Proportions of Different Attack TypesÂ
In 2018, the most frequently seen attacks were SYN flood, UDP flood, ACK flood, HTTP flood, and HTTPS flood attacks6, which altogether accounted for 96% of all DDoS attacks. In contrast, reflection attacks contributed to no more than 3% of attacks. Compared with 2017, the year 2018 witnessed an 80% decrease in the number of reflection attacks, but a 73% increase in other attacks. This is because Chinese authorities took effective measures against reflectors (see section 3.1.1 “Attack Count and Traffic”).
In terms of attack traffic, ACK flood attacks generated 42.6% of the total attack traffic. The likely reason for this is that certain sectors (like gaming) have large quantities of users and sessions as well as longlived connections, making them easy targets of ACK attacks characterized by large packets.
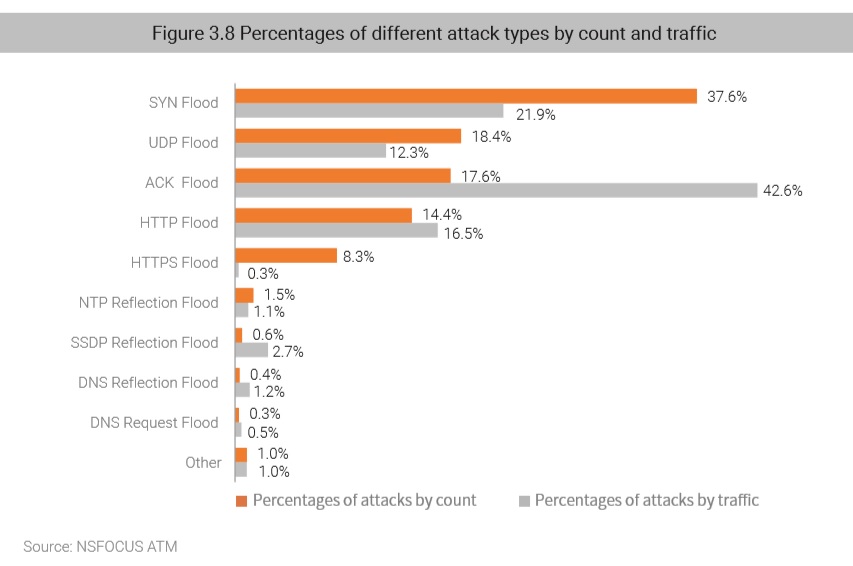
SYN flood attacks still stood out among all types of DDoS attacks. This attack exploits defects in the TCP protocol, where an attacker sends a large number of TCP connection requests to exhaust resources of a target. This exploit method is seldom used independently, but rather used with SYN floods to overwhelm hosts and firewalls that must perform large quantities of calculations to determine whether ACK packets are legitimate. This will deplete resources of the target and at the same time complete a traffic-based attack.
UDP floods are long-lived, traffic-based DDoS attacks. Usually, an attacker floods DNS servers, RADIUS authentication servers, or streaming media servers with a large number of small UDP packets. As a simple protocol, UDP makes it extremely easy to generate large amounts of traffic as UDP floods do not require setup of connections, thus becoming a most favored attack method.
HTTP floods and HTTPS floods are attacks launched at the application layer against web servers. An attacker conducts this type of attack by simulating a legitimate user accessing websites. This may cause serious chain effects. When a client keeps sending requests while performing frequent database operations, not only will the web frontend respond slowly, but the backend server program will also be indirectly affected. In the worst-case scenario, backend services, such as the database, may stop responding or crash, and even related hosts, such as the log storage server and image server, may be compromised.
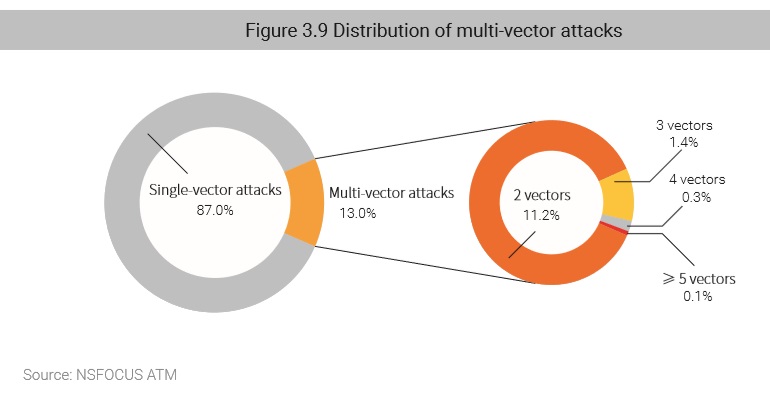
Of all DDoS attacks, 13% used a combination of multiple attack methods. By flexibly combining several methods to adapt to different environments of target systems, attackers can initiate large amounts of traffic and exploit vulnerabilities in different protocols and systems, thus bringing their capabilities into full play. On the other side of the fence, defenders find it rather difficult and costly to effectively analyze, respond to, and mitigate such distributed attacks involving various protocols and leveraging various resources.
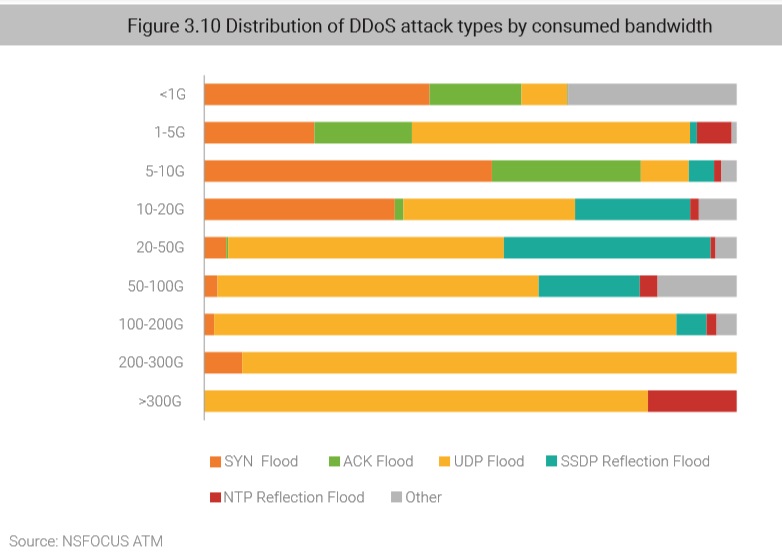
3.2.2Â Distribution of Attack Types by Consumed BandwidthÂ
In 2018, DDoS attacks with a peak rate of less than 10 Gbps were mostly conventional attacks like SYN and ACK floods. Attacks ranging from 10 Gbps to 100 Gbps mainly used UDP and SSDP reflection methods. Of all volumetric attacks peaking at more than 100 Gbps, UDP, NTP, SSDP, and SYN floods were dominant attack methods.
In 2018, UDP flood attacks overtook SYN flood attacks to contribute the largest proportion of volumetric attacks. In 2017, SYN flood attacks dominated this realm because of prevalent use of large SYN packets. However, this type of attack has a distinct pattern and is so easy to identify and block. This change in the dominant position of attack types reflects the constant iteration and evolution of offensive and defensive techniques and methods. At the same time, the security of IoT is becoming an increasingly serious issue as many connected devices of low power consumption can be converted to bots. Also contributing is bandwidths keep expanding all around the world. All these factors make UDP floods, which leverage the connectionless UDP protocol while providing low resource consumption and high bandwidth usage, a favored type of DDoS attack.
3.2.3Â Reflection AttacksÂ
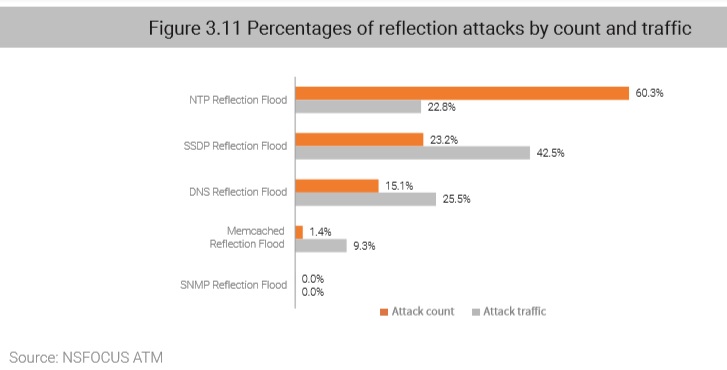
In 2018, the number of reflection attacks experienced a sharp drop, accounting for only 3% of the total DDoS attacks, but still contributed 10% of total DDoS traffic. Due to their amplification effect, reflection attacks are still a hazard that cannot be ignored.
In terms of the attack count, NTP reflection attacks topped the list, accounting for 60% of all reflection attacks. In terms of the attack traffic, SSDP reflection attacks generated 42% of traffic.
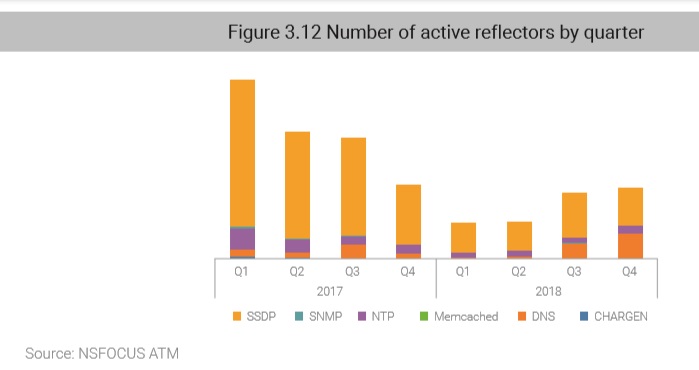
The number of active reflectors dropped 60% in 2018. Specifically, the number of SSDP reflectors decreased significantly, while that of DNS reflectors rose a bit. Within China, government crackdown on attack sources, especially SSDP reflectors, has borne fruit.
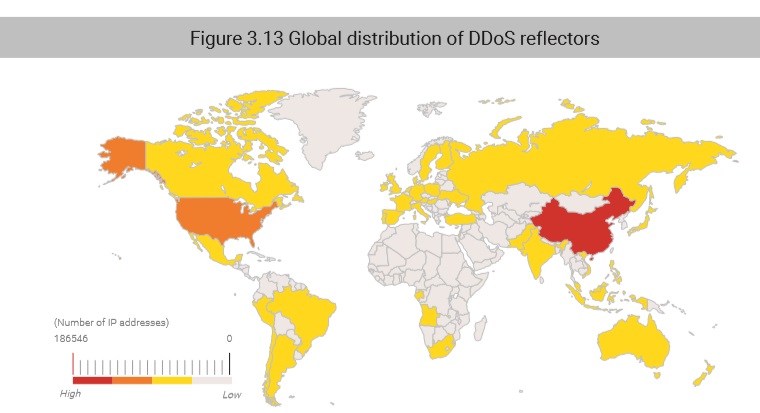
As for geographic locations of reflectors used for DDoS attacks, from the global perspective, China was home to the most reflectors (46%), followed by Russia, the USA, Brazil, and Canada.
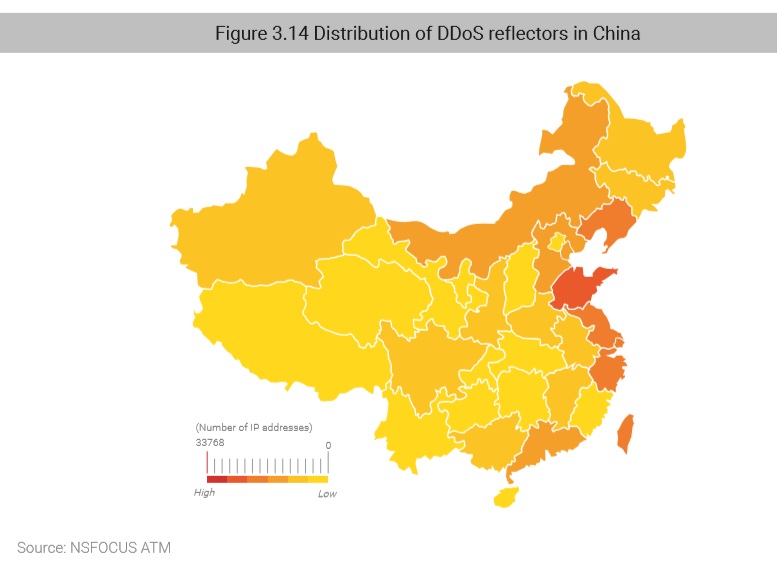
Within China, the largest percentages (18%) of reflectors were found in Shandong province, followed by Liaoning, Zhejiang, Taiwan, and Jiangsu.
to be continue