The security knowledge graph, a knowledge graph specific to the security domain, is the key to realizing cognitive intelligence in cyber security, and it also lays an indispensable technological foundation for dealing with advanced, continuous and complex threats and risks in cyberspace. NSFOCUS will publish a series of articles about...
Categoria: Research & Reports
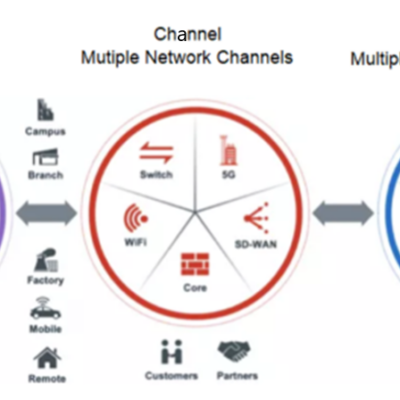
SASE: The Relationship Between SD-WAN and SASE
Last time we talked about the powerful features and rich usage scenarios of SD-WAN (SASE Popular Science Series: Understanding SD-WAN), what about the relationship between such a powerful SD-WAN and NSFOCUS SASE? This starts with the challenges faced by enterprises today...... Current Problems Faced by Enterprises Single node deployment security...
7 Gbps TCP-Middlebox-Reflection Incident Mitigated by NSFOCUS
In mid-April, NSFOCUS discovered that one of its Cloud DDoS Protection Service customer in APAC region has encountered a TCP-middlebox-reflection attack which became popular throughout the world during past months after its first discourse in Aug, 2021. The attack reached its peak at 7Gbps and lasted for several hours, after...
Information Collection Technology of Cloud Native Environment (I)
Abstract Information collection is a very important part of both attack and defense, and high-quality information collected is the basis and premise of follow-up work. However, fragmentary information and the complex composition of cloud native itself bring certain challenges to information collection in cloud native environment. This series of posts...
Thoughts on Encrypted Traffic Detection in the Era of Encrypt Everything
Background With the wide application of encryption technology and the continuous development of new network technology, the network structure becomes more and more complex and the encrypted traffic explodes. Furthermore, as the evolution and promotion of encryption protocols such as TLS1.3, the era of full encryption is silently coming. When...
How to Monitor Threat Traffic in Cloud Environment ?
Background The public cloud has become the hardest hit by cyberattacks. This article gives you an effective threat monitoring proposal by using VPC traffic mirror. Traffic Mirror In the traditional network environment, the data communications between devices are realized via cables or wireless networks. We can completely divert the traffic...