1. Vulnerability Description Recently, NSFOCUS detected that the foreign security company Secura disclosed detailed information and validation scripts about the Netlogon privilege escalation vulnerability (CVE-2020-1472), which increases vulnerability risks abruptly. Exploitation of this vulnerability requires a computer on the same local area network (LAN) as the target. When using the...
Blog
Microsoft Exchange Server Remote Code Execution Vulnerability (CVE-2020-16875) Threat Alert
Overview Microsoft has fixed a critical vulnerability in its September 2020 Security Updates, which is a remote code execution vulnerability (CVE-2020-16875) in Microsoft Exchange Server. Recently, relevant proof of concept (PoC) has appeared on the Internet. Due to incorrect verification of cmdlet arguments, an attacker may trigger this vulnerability by...
Microsoft September 2020 Security Updates for Multiple High-Risk Product Vulnerabilities Threat Alert
Vulnerability Description On September 9, 2020, Beijing time, Microsoft released September 2020 Security Updates that fix 129 vulnerabilities ranging from remote code execution to privilege escalation in various products, including Microsoft Windows, Internet Explorer, Microsoft Office, Microsoft Exchange Server, Visual Studio, and ASP.NET. (more…)
Botnet Trend Report 2019-12
This chapter describes active botnet families under long-term tracking of and other families newly captured by NSFOCUS Security Labs, from the perspectives of their background, activity, and association with other families. Botnet Families GoBrut Malware in the GoBrut family, written in Go, made its debut in early 2019, in a...
Apache DolphinScheduler High-Risk Vulnerabilities (CVE-2020-11974, CVE-2020-13922) Handling Guide
1. Vulnerability Description On September 11, 2020, NSFOCUS detected that the Apache Software Foundation released security advisories fixing Apache DolphinScheduler permission overwrite vulnerability (CVE-2020-13922) and Apache DolphinScheduler remote code execution vulnerability (CVE-2020-11974). CVE-2020-11974 is related to mysql connectorj remote code execution vulnerability. When choosing mysql as database, an attacker could...
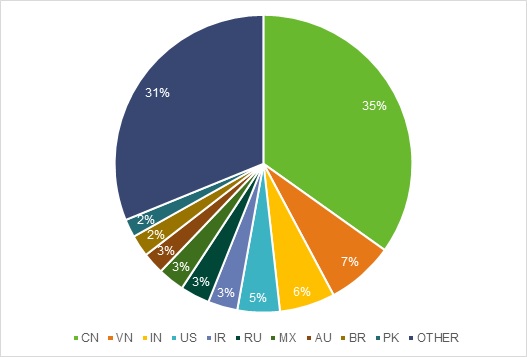
Analysis of the 2020 H1 Malware Trend
1. Overview From data collected throughout 2019 and data as of June 30, 2020, we extracted information about malware, whose distribution by type is shown in Figure 1-1. Compared with 2019, the percentages of various types of malware in 2020 H1 changed, with backdoors overtaking crytominers to become No .1...