In today's business security operations, the tide of security information and event management (SIEM) is on the ebb. Many enterprises have established the security operations center (SOC) and collected massive security data. But how to make use of and analyze such data remains a problem to be resolved. Data, after...
Author: Jie Ji
Insights into Ransomware Spread Using Exchange 1-Day Vulnerabilities 2-2
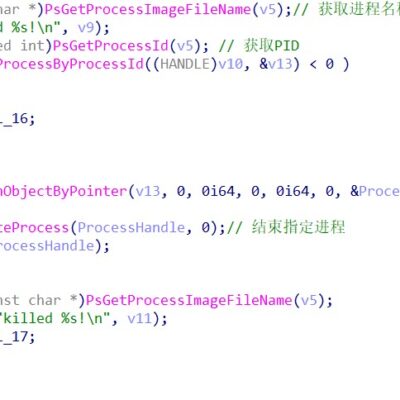
Analysis of the Kill Chain of the LockFile Ransomware Group KDU Tool Terminating Multiple Antivirus Processes The attacker renames the KDU tool (open-source Windows driver loader implementing DSG bypass via an exploit) autologin, copies the related program to the temporary directory, and loads and executes the designated driver file to...
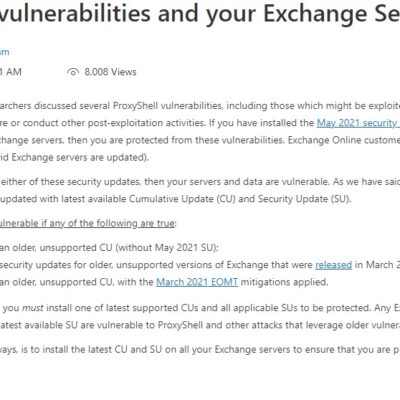
Insights into Ransomware Spread Using Exchange 1-Day Vulnerabilities 1-2
Event Overview Recently, NSFOCUS CERT discovered a slew of security incidents that exploited security vulnerabilities (ProxyShell) in Microsoft Exchange. Also, NSFOCUS found that the new LockFile ransomware group LockFile took advantage of these ProxyShell and PetitPotam vulnerabilities to target enterprise domain environments, finally encrypting quite a few hosts from enterprises...
New Architecture, New Challenges: Service Security Issues in the 5G Core Network and How to Detect Them
Abstract: 5G is the fifth-generation technology standard for mobile communication networks. The service-based architecture (SBA) of the 5G core network is designed with a cloud-native approach. By borrowing the "microservice" concept implemented in the IT field and dividing a whole entity with multiple functions into individual parts, each providing an...
Linux Kernel Arbitrary Code Execution Vulnerability (CVE-2021-3490) Threat Alert
Overview Recently, NSFOCUS CERT found that a security researcher published details and the PoC of an arbitrary code execution vulnerability (CVE-2021-3490) in eBPF and exploited this vulnerability to cause local privilege escalation on Ubuntu 20.10 and 21.04. This vulnerability exists because the eBPF ALU32 bounds tracking for bitwise ops (AND,...
Cloud Native Security in Infrastructure Construction
Cloud native security is the development trend of cloud security in the coming years. On the one hand, inherent security of cloud native is worthy of in-depth study. On the other hand, with the reconstruction and upgrade of infrastructure, there is a clear trend towards the integration of cloud native technologies...