Background The public cloud has become the hardest hit by cyberattacks. This article gives you an effective threat monitoring proposal by using VPC traffic mirror. Traffic Mirror In the traditional network environment, the data communications between devices are realized via cables or wireless networks. We can completely divert the traffic...
Author: Jie Ji
Microsoft’s March security update for multiple high-risk product vulnerabilities
Overview On March 9, NSFOCUS CERT detected that Microsoft released the March security update patch, which fixed 71 security issues, involving Windows, Exchange Server, Remote Desktop Client, Azure, etc., including privilege escalation, remote code execution and other high-risk vulnerability types. Among the vulnerabilities fixed by Microsoft's update this month, there...
1TB Multi-Vector DDoS Attack in LATAM Blocked after CVE-2022-26143 Vulnerability Exploited
In early March, NSFOCUS Cloud Scrubbing SOC team discovered that one of our customers in Latin America suffered a volumetric, multi-vector distributed denial-of-service (DDoS) attack. NSFOCUS Cloud DPS prevented this attack successfully. The captured entire attack and defense process is as follows: March 3, 10:00 a.m. GMT+8 NSFOCUS cloud-based Network...
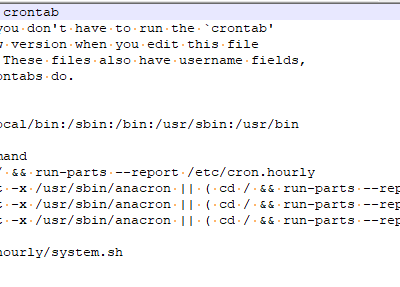
Linux Kernel Privilege Escalation Vulnerability (CVE-2022-0847) Alert
Overview Recently, NSFOCUS CERT detected that a security researcher disclosed a local privilege escalation vulnerability (CVE-2022-0847) in the Linux kernel. Due to a flaw in the correct initialization of the copy_page_to_iter_pipe and push_pipe functions in the Linux kernel, an attacker can overwrite the data in any readable file by exploiting...
Security Risks of 5G Core Network Introduced by New Technology
Intro This article cuts into 5G from the key technologies of 5G networks and discusses the security risks facing 5G networks. Today, 5G networks have achieved performance goals, namely high speed, low latency, and large capacity, and have started a new chapter for communications between mobile devices. Further, 5G will...
Spring Cloud Gateway Remote Code Execution Vulnerability (CVE-2022-22947) Alert
Overview Recently, NSFOCUS CERT detected that Spring released a report to fix the Spring Cloud Gateway code injection vulnerability (CVE-2022-22947). Due to a flaw in the Actuator endpoint of Spring Cloud Gateway, when a user enables and exposes an insecure Gateway Actuator endpoint, Applications using Spring Cloud Gateway are vulnerable...