NSFOCUS Speaking at TELECOM EXCHANGE NYC 2019

maio 14, 2019
Telecom Exchange, one of the largest C-level networking events that provides unparalleled collaboration, education, and one-on-one engagement with the industry’s top decision-makers, is heading to NYC next week. Executives from all around the world will be meeting to discuss the complex network infrastructure ecosystems, technology and what it means for telecom. The event will […]
A Look into RSA 2019: Interpretation of the Application Security Trend — DevOps and API Security

maio 14, 2019
As cloud computing, big data, Internet of Things (IoT), and mobile Internet evolve, application forms and requirements are going through changes. I believe that the application security trend virtually highlights technologies and design theories: technological innovations continue to focus on API concepts; the design theories of solutions, products, and services continue to move towards DevOps (development and operations). In this article, I will discuss the application security trend. (mais…)
New Words at RSA: Machine Learning Abuse, XAI, Election Security, and CISA

maio 13, 2019
The RSA Conference is the world’s biggest IT security meetings of the highest quality. Initially as a small cryptography forum set up in 1991, this conference has developed into a meeting at which renowned security experts from all around the world are invited to discuss the future cyberspace development and global security vendors are attracted to showcase their information security products. (mais…)
Using NLP-based Machine Learning to Automate Compliance and Risk Governance

maio 10, 2019
The Governance, Risk & Compliance track of the RSA Conference 2019 focuses on quantification of cybersecurity risks and related cases. For example, Superforecasting II: Risk Assessment Prognostication in the 21st Century by Rich Howard from Palo Alto Networks dwells upon how to evolve semi-quantitative risk assessment into more accurate quantitative risk assessment; Math is Hard: Compliance to Continuous Risk Management presents the entire process of quantitative risk assessment; NIST Cybersecurity Framework and PCI DSS provides practices of implementing PCI-DSS standards in the cybersecurity framework (CSF) and points out complex mapping relationships between the two. (mais…)
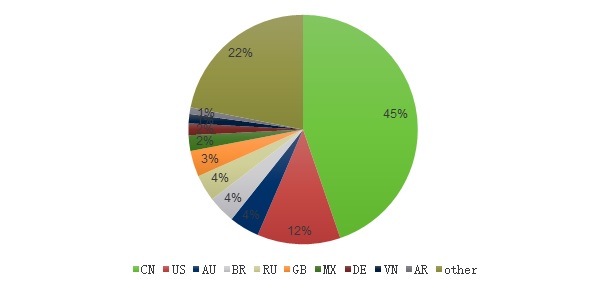
2018 DDoS Attack Landscape-5

maio 8, 2019
3.3 DDoS Attack Duration
3.3.1 Attack Duration Distribution
In 2018, the average duration of a DDoS attack was 42 minutes, down 17% from 2017. This indicates that DDoS attacks were upgraded in industrialization, weaponization, and efficiency and DDoS-as-aService gained momentum for fast growth. We noticed that the longest DDoS attack in 2018 lasted around 12 days, far shorter than attacks detected in previous years. (mais…)
A Look into RSA 2019-Automation of Threat Discovery and Response

maio 7, 2019
The RSA Conference 2019, which is dedicated to addressing worldwide information security issues, was held in March 4–8. This year’s RSA Conference took “Better” as its theme, aimed at exploring new cybersecurity development realms in a digital epoch and finding better security vendors, products, services, and solutions. In the past few years, with the rapid adoption of big data and artificial intelligence (AI) techniques, players across the security industry have been energetic in pushing “better” application of these new techniques in the security field. Detection and response are the two permanent security topics much talked about at both last year’s and this year’s conference. This indicates that security vendors are inputting more resources into AI-automated detection and response. By combining automation, process orchestration, AI, and machine learning, they try to optimize their centralized security management and operations platform for more automatic and intelligent threat discovery and response. (mais…)
Analysis of File Disclosure by APT34

maio 6, 2019
1 About APT34
APT34, exposed to the public view in 2014, mainly targets Middle Eastern countries and some international organizations. APT34 attacks a variety of sectors mainly in the Middle East, but not limited to finance, government, energy, chemical engineer, and telecommunications. (mais…)
Oracle WebLogic Server Deserialization Remote Code Execution Vulnerability Threat Alert

maio 3, 2019
1 Vulnerability Overview
On April 17, China National Vulnerability Database (CNVD) published details of a remote code execution vulnerability in Oracle WebLogic Server. Specifically, this vulnerability exists in the wls9_async_response.war component that comes with Oracle WebLogic Server as this component fails to properly deserialize the input information. An unauthorized attacker could exploit this vulnerability to gain server privileges for remote code execution by sending a carefully crafted malicious HTTP request. (mais…)