1 Vulnerability Overview
On April 17, China National Vulnerability Database (CNVD) published details of a remote code execution vulnerability in Oracle WebLogic Server. Specifically, this vulnerability exists in the wls9_async_response.war component that comes with Oracle WebLogic Server as this component fails to properly deserialize the input information. An unauthorized attacker could exploit this vulnerability to gain server privileges for remote code execution by sending a carefully crafted malicious HTTP request.
wls9_async_response.war provides asynchronous communications for the WebService component. This file, by default, is contained in WebLogic Server of most versions.
Reference link:
http://www.cnvd.org.cn/webinfo/show/4989
2 Scope of Impact
Affected Versions
- Oracle WebLogic Server 10.*
- Oracle WebLogic Server 12.1.3
This vulnerability affects all versions of Oracle WebLogic Server with the bea_wls9_async_response component enabled.
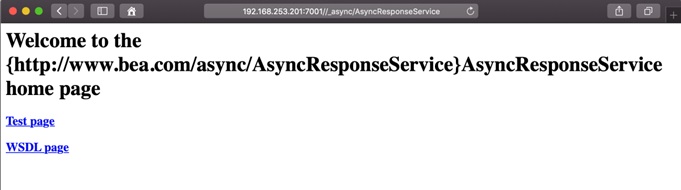
3 Vulnerability Check
This vulnerability exists in the asynchronous communication service. Users can access /_async/AsyncResponseService to check whether the bea_wls9_async_response component is enabled. If the following page is returned, this component is enabled. Users of this software should attach importance to this issue and take corresponding protective measures as soon as possible.
4 Vulnerability Mitigation
The vendor has not released patches to fix this vulnerability and users can adopt the following measures for temporary protection:
- Configure a URL access policy: Configure an access control policy to block access to /_async/*.
- Delete wls9_async_response.war and related folders and restart WebLogic Server.
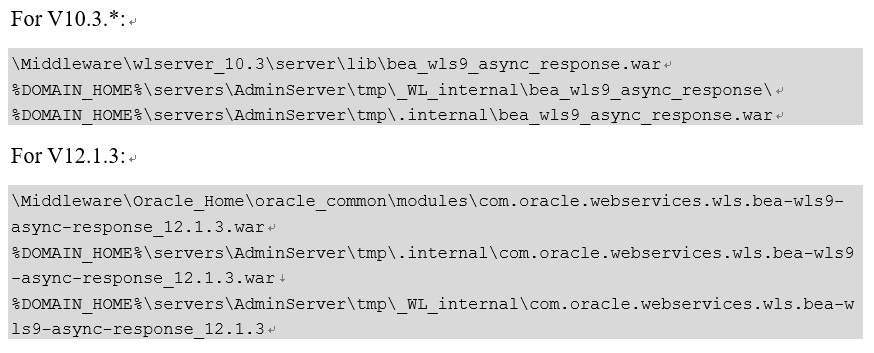
The following shows the path to the vulnerable file:
Note: wls9_async_response.war is a level-1 application package. Removing or renaming it could cause unintended consequences, and thus Oracle does not recommend such operations. For issues arising from the direct deletion of this package, Oracle does not provide technical support for resolution. In view of this, users, before performing such operations, should assess the resulting impact and back up this file.
Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.