1 About APT34
APT34, exposed to the public view in 2014, mainly targets Middle Eastern countries and some international organizations. APT34 attacks a variety of sectors mainly in the Middle East, but not limited to finance, government, energy, chemical engineer, and telecommunications.
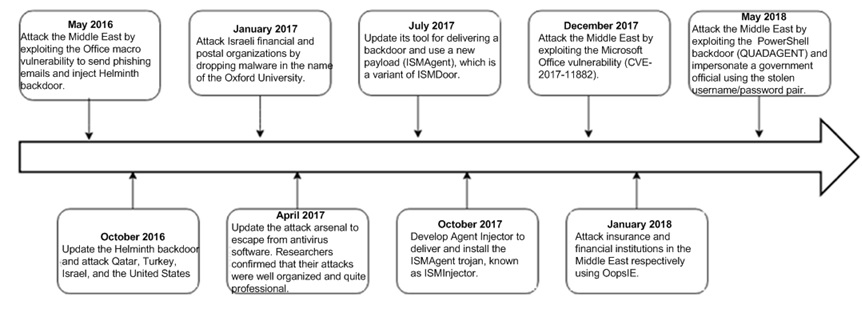
The following figure shows recent activities of APT34.
By tracking and analyzing attack events conducted by APT34, researchers from FireEye confidently concluded that APT34, backed by the Iran government, has so many similarities to OilRig in attack models that they are the same organization. So far, APT34 is also known as OilRig and Helix Kitten.
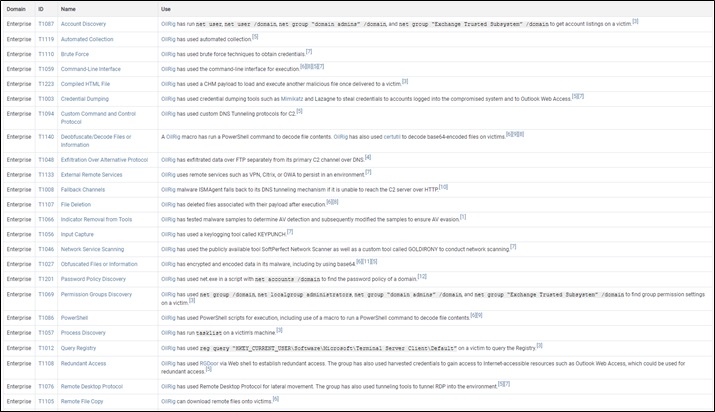
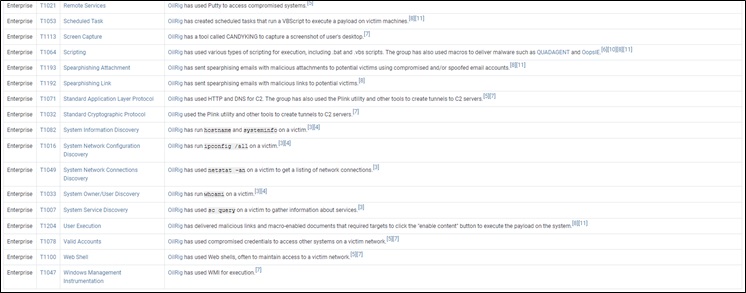
The following table lists the attack techniques exploited by APT34.
Source: https://attack.mitre.org/groups/G0049/
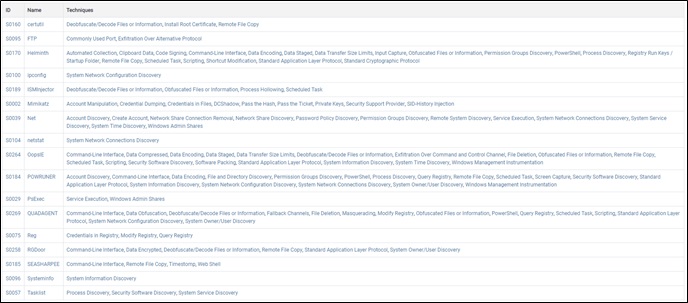
Attacks tools used by APT34 are as follows:
Source: https://attack.mitre.org/groups/G0049/
Recently, a hacking group named Lab Dookhtegan revealed some hacking tools on Telegram, claiming that they were attributed to APT34.
2 Disclosure Event
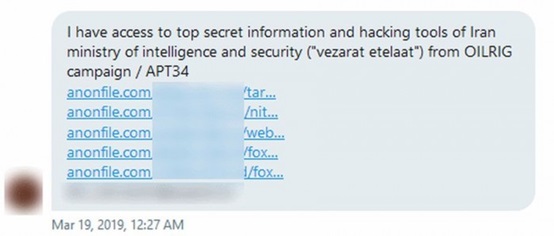
In a March post on Telegram, Lab Dookhtegan said that they had got attack tool used by APT34/OilRig.
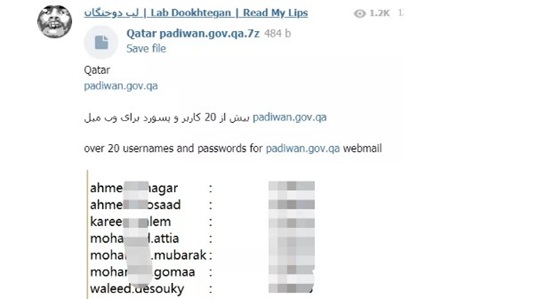
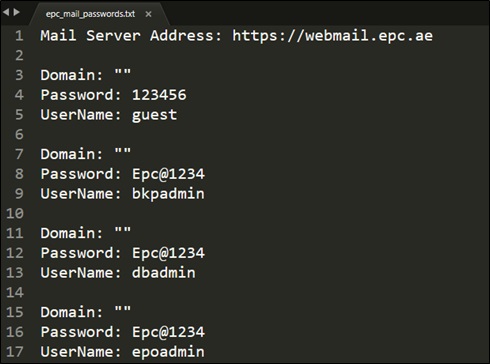
Lab Dookhtegan also disclosed evidences of APT34 operations and victim information, such as combinations of login user names and passwords possibly obtained through phishing attacks.
To download the disclosed hacking tools, click the following link:
https://s3-eu-west-1.amazonaws.com/malware-research.org/blogposts/apt34Leak/apt34leak.7z.
Decompression password: vJrqJeJo2n005FF*.
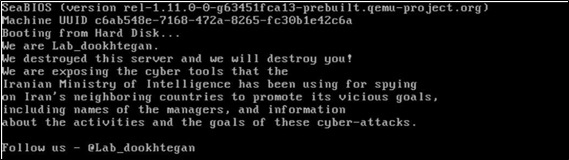
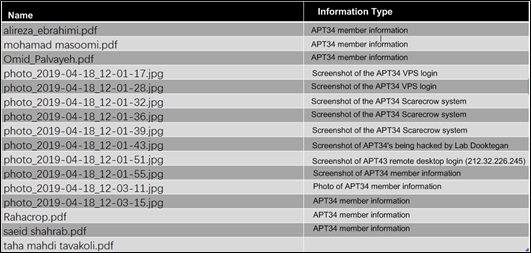
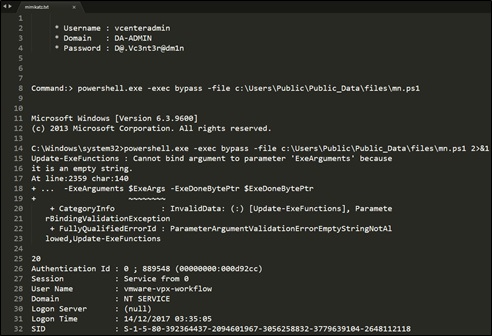
The analysis of the published files shows that Lab Dookhtegan gained the virtual private servers (VPS) system privileges used by APT34 Lab Dookhtegan, through penetration and then conducted in-depth traceback and forensics to finally get internal data of the APT34 group. After completing the forensics, Lab Dookhtegan destroyed the data stored in the hosts used by APT34 members. The following document content screenshots prove that the preceding speculation is correct.
3 Disclosed Data
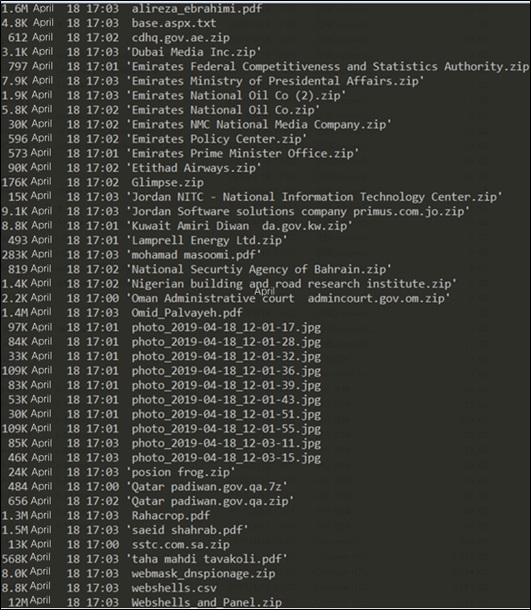
After downloading and decompressing APT 34 data disclosed by Lab Dookhtegan, we get a file list which contains 44 files, covering three categories of information, namely, APT34 intrusion results, APT34 members, and hacking tools used by APT34.
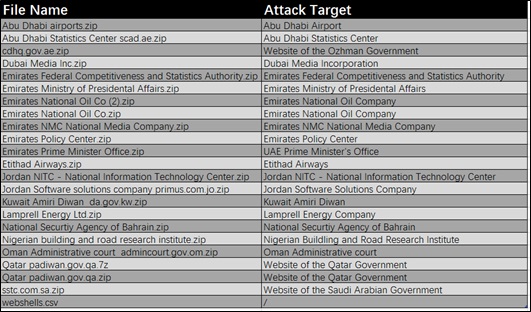
The following table lists the intrusion targets of APT34, mostly in the Middle East.
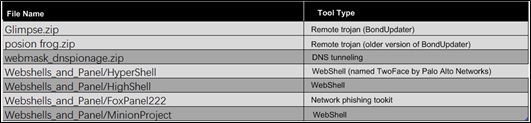
The following table lists some attack tools (other attack tools are contained in the Webshells_and_Panel.zip compression file).
The following table lists files that shows personal information of APT34 members and some screenshots of the systems they use.
4 In-depth Analysis of the Disclosed Data
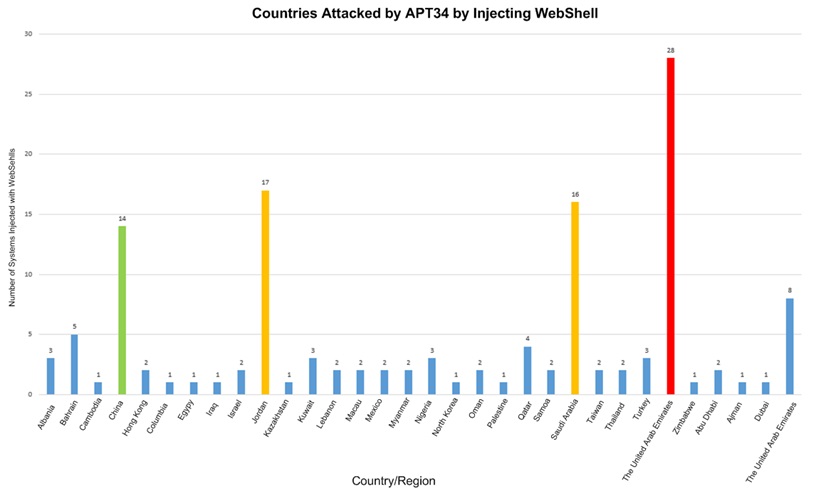
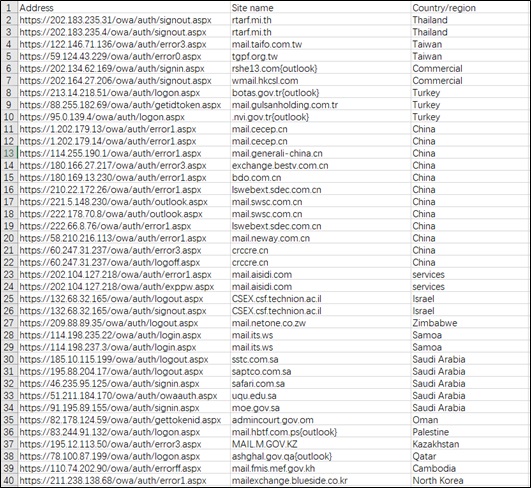
Deduplicating intrusion results recorded in the disclosed intrusion files (.zip) and webshells.csv, we mapped the distribution of countries in which APT34 injected WebShell, as shown in the following figure.
According to the number of systems injected with WebShell by APT34, top 4 countries are the United Arab Emirates (28), China (20), Jordan (17), and Saudi Arabia (16).
We can see that the above attack target distribution graph also shows that the attack targets are mainly located in the Middle East.
The following table lists the Chinese enterprises successfully compromised by APT34.
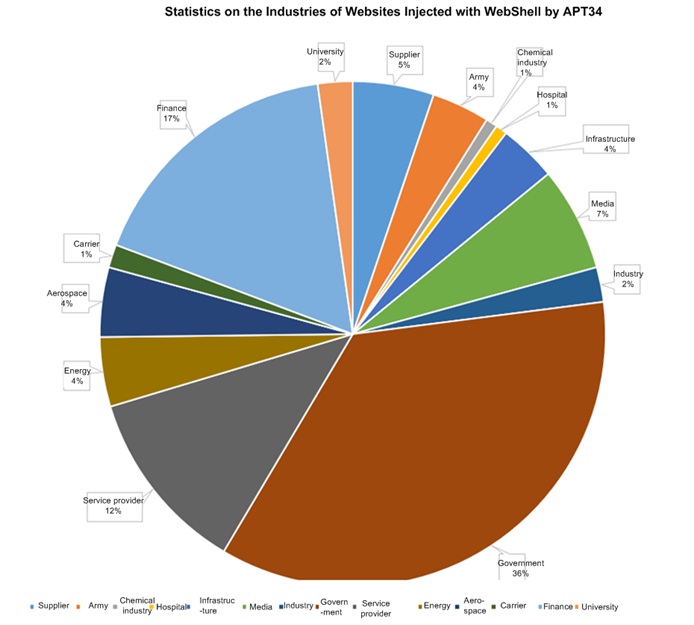
After querying the domain names of the websites compromised by APT34, we get the industrial distribution, as shown in the following figure (a small portion of unknown websites are ignored).
The statistics show that government (36%), finance (17%), service provider (12%), and media (7%) are mostly targeted.
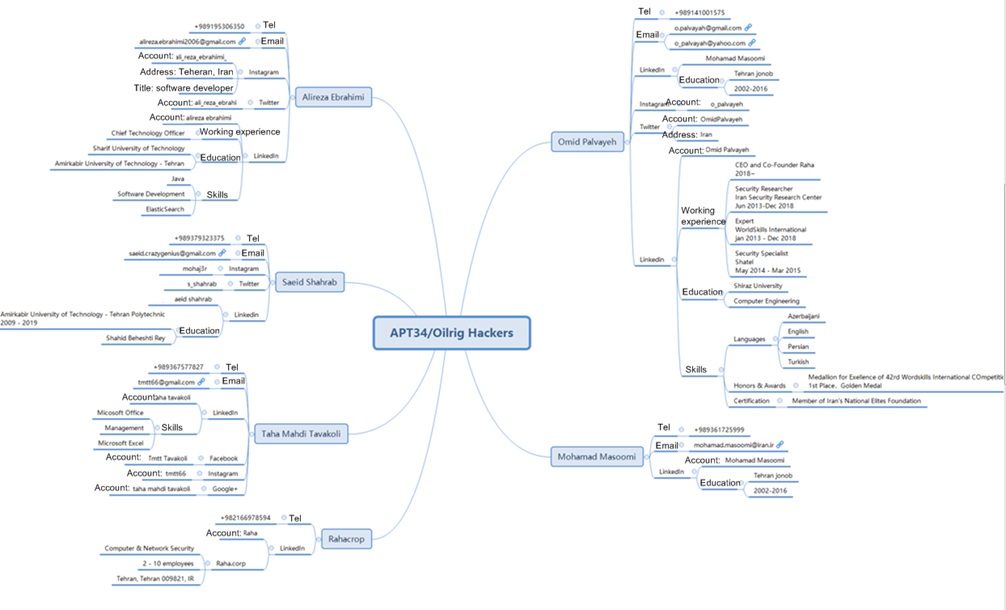
The APT34 data disclosed by Lab Dookhtegan contains the personal information of six APT34 members. The correlation analysis of APT34 members is as follows:
After analyzing the personal background information of APT34 members, we can conclude that APT34 is an Iran-linked organization, which proves FireEye’s speculation about the APT34 background.
By analyzing information of the compromised systems contained in the leaked intrusion record files, we can see that APT34 is good at breaching web security, breaking into the OA or WebMail system before penetrating into the target system.
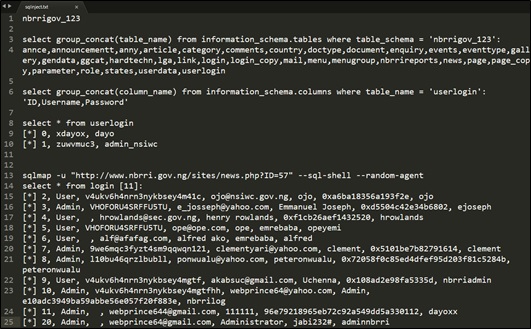
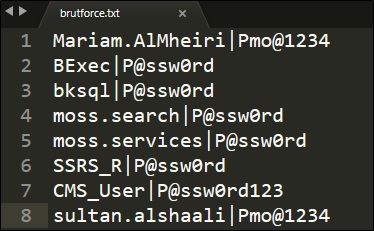
APT34 adopts various attack methods, including web security vulnerabilities (SQL injection), brute-force cracking, weak password dictionary attack, 0-day attack, and intranet penetration.
- Obtaining system data via an SQL injection attack.
- Brute-force cracking attack.
- Weak password dictionary attack.
- Using mimikatz for lateral movement during intranet penetration, extending the attack impact.
- It seems that APT34 has mastered the 0-day vulnerability of a webmail system. Intrusion records show that most attacks used the webmail system as the entry point.
5 Summary
Recently, advanced persistent threats (APTs) have been a hot spot in the cybersecurity field and one of the most eye-catching keywords at RSA conferences.
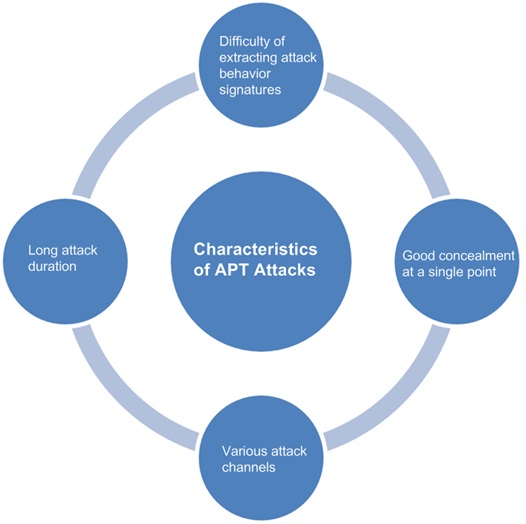
APT attacks are characterized as follows: 1. difficulty of extracting attack behavior signatures; 2. good concealment at a single point; 3. various attack channels; 4. long attack duration.
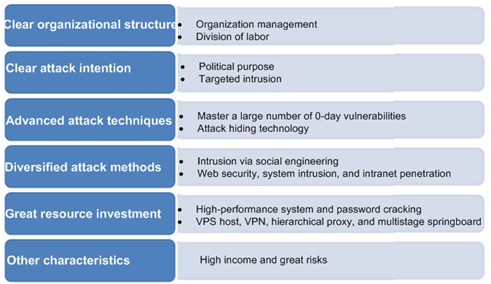
APT attack organizations are always regarded as very mysterious. They have such characteristics as a quite clear organizational structure, clear attack intentions, advanced attack techniques (mastering 0-day vulnerabilities), diversified attack methods, high income, great risks, and great resource investment (password cracking, VPS host, VPN, proxy, and springboard).
Since APT attacks and APT organizations have their own distinctive characteristics, analysts should not let go of any clues during analysis, and also need to broaden minds to seek new breakthrough points.
The event of hacking into APT34 for internal file disclosure provides a new idea for security defense systems. That is, black eats black. In the case of a penetration event, an enterprise, after going through the traditional emergency response procedure (policy, protection, detection, and reaction (PPDR)), could conduct proper reverse penetration for attack location and tracking.