The RSA Conference 2019, which is dedicated to addressing worldwide information security issues, was held in March 4–8. This year’s RSA Conference took “Better” as its theme, aimed at exploring new cybersecurity development realms in a digital epoch and finding better security vendors, products, services, and solutions. In the past few years, with the rapid adoption of big data and artificial intelligence (AI) techniques, players across the security industry have been energetic in pushing “better” application of these new techniques in the security field. Detection and response are the two permanent security topics much talked about at both last year’s and this year’s conference. This indicates that security vendors are inputting more resources into AI-automated detection and response. By combining automation, process orchestration, AI, and machine learning, they try to optimize their centralized security management and operations platform for more automatic and intelligent threat discovery and response.
As Nick Bilogorskiy, a security expert from Juniper Networks, points out in his Accelerate and Simplify Incident Response with Security Automation, techniques utilizing security automation can significantly simplify and accelerate incident response (IR).
Security Trend Study
Bilogorskiy starts the presentation with his investigation of development trends of advanced threats in tactics, techniques, and procedures (TTPs). First, with the constant leaks of personal information, attacks exploiting personal account passwords have steadily risen. According to his survey, 32% of hackers believed that accessing privileged accounts was the fastest and easiest way to hack; 81% of breaches were achieved by leveraging stolen/leaked accounts and passwords or existing weak passwords. Along with this trend, credential stuffing (brute-force cracking with a dictionary of stolen passwords) enabled by leaked passwords was becoming increasingly prevalent. Second, attacks targeting two-factor authentication (2FA) are also frequently seen. For example, in SIM swapping, an attacker manages to trick a mobile service provider by some stealthy means into moving a victim’s mobile number to an attacker-controlled SIM card. In this process, the 2FA mechanism that uses mobile phones as the receiving end becomes an accessory to hackers. Third, attacks targeting the software supply chain have also jumped sharply. Only in 2017, the number of such attacks surged 200%. Throughout the supply chain, third-party partners were most targeted. 42% of companies were affected by such attacks that resulted in serious data breaches. As is often said, we fear not God-like rivals, but pig-like team members. Finally, cyberattacks are now powered by a high degree of automation and packaging. Sophisticated attackers have their own automated, integrated attack toolsets that are capable of initiating an almost fully automated process of attack to effectively take down victims.
SOC Problems
To cope with the severe security situation of advanced threats, people often mention security platform products, such as the security operations center (SOC) and security information and event management (SIEM) software, as a possible cure. All “ambitious” security researchers from security companies dream of having their own security analysis platforms. The reality, however, is far less uplifting. Based on his investigation, Bilogorskiy listed four major problems currently facing SOCs:
(1) Too many alerts overload the platform.
(2) Operations require large amounts of manpower, resulting in staffing challenges.
(3) The complexity of functions adds to the difficulty in operations.
(4) Defenses, which always come after events, evolve slower than threats.
Machine Learning and Security
Bilogorskiy then moved on to explain the roles played by machine learning in the security realm. For starters, he illustrated the wide gap between hype (promotional ploy) and reality (academic research) in machine learning and described what he himself understood about security detection. My interpretation of his analysis is that the following three questions must be answered when a new event calling for file detection or human judgment occurs:
(1) Yes/No question: Is the file or event malicious?
(2) Multiple-choice question: If malicious, what type of malware is it (trojan, worm, adware, or something else)?
(3) Subjective question: Assess the risk based on information on hand.
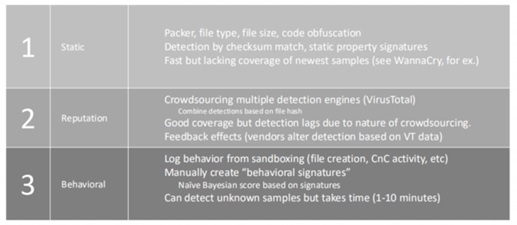
He listed three approaches to malicious file detection, as shown in the following table.
Figure 1 Traditional approaches to threat detection
The preceding table lists static detection, file reputation detection, and sandboxing-based behavioral detection approaches, accompanied with a brief introduction of each approach, including the detection content, method, performance, and effect. Of the three approaches, static detection and reputation detection work well for “known knowns”, while detection based on behavioral analysis is effective, more or less, for “know unknowns”.
Detection based on behavioral analysis speaks much for the advantages of machine learning as this approach can detect malware using indirect indicators (not necessarily malicious indicators, that is, users’ “normal” operations). Indirect indicators are superior to traditional indicators of compromise (IoCs) in that they are difficult to disguise or counterfeit thanks to the relative frequency of certain actions and combinations of actions. They may also be useful for more generalized detection to identify different families that share “tradecraft”. Besides, using malware training sets with particular composition, we can easily customize detection focus. Finally, this type of detection can adapt to deployment environments thanks to benign samples from a given organization.
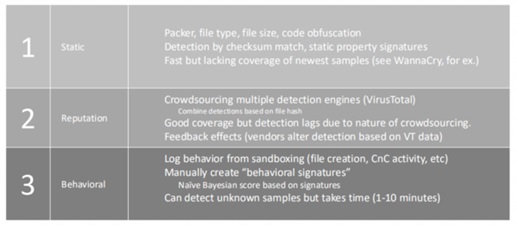
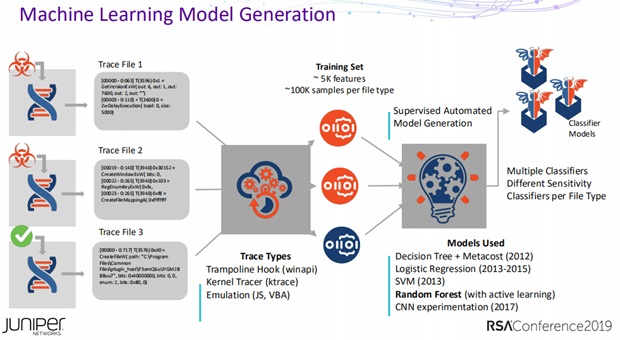
Next, Bilogorskiy quoted what people often say when speaking of machine learning: data is king. He believed that appropriate training data is the most important factor in the success of the model and used the following diagram to show the general process of model training.
Figure 2 General process of model training
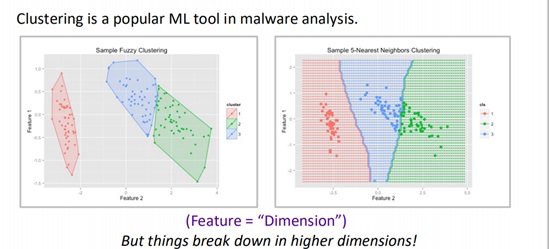
When it came to the topic of machine learning toolkits, he explained in detail supervised learning, unsupervised learning, and semi-supervised learning. In addition, he proposed the “Gold Standard” for successfully using machine learning: (1) Know your data; (2) Know the benefits and pitfalls of your algorithms; (3) Be ready to iterate, rinse, and repeat.
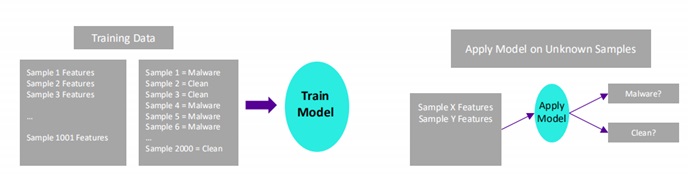
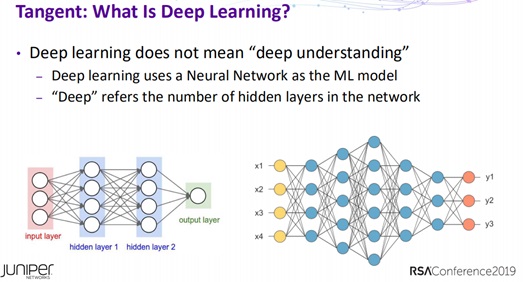
Following are some slides taken from his presentation that are worth studying.
Figure 3 Model training and using process of supervised learning
Figure 4 Deep learning
Figure 5 Generation of the machine learning model based on classification of file samples
Figure 6 Unsupervised learning
Figure 7 Clustering analysis
Automation of Incident Response
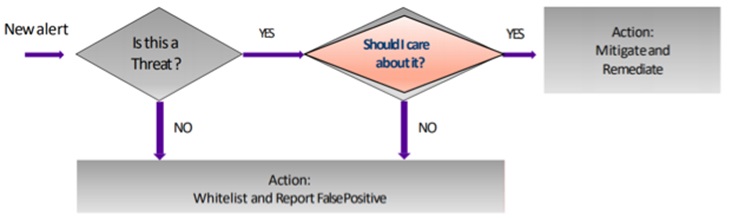
In what ways can the automation of threat response help? Bilogorskiy listed three ways: (1) Collecting, correlating, and understanding data from multiple sources to identify advanced threats; (2) Continuously learning threat behaviors and automatically working with security tools to contain threats; (3) Increasing detection accuracy and providing security professionals with better data with which to make decisions. He used the following flowchart to analyze the typical threat response process.
Figure 8 Typical incident response process
Throughout the process, in the face of new alerts that keep emerging, we need to repeatedly make decisions from the operational perspective, identifying the real threats and determining whether we should care about and further analyze them. If yes, we should take mitigating or remediating measures; if no, we should add them to a whitelist or report false positives. To better prioritize efforts in threat handling, we need a mechanism to evaluate what kinds of threat should be cared about. Bilogorskiy thought that a good mechanism should have the following characteristics: (1) intersecting incident targets with asset values: (2) factoring in the scope and progression context (how close it is to “action on objectives”). He also prioritized actions in threat response: (1) Identify basic properties of an attack (source, target, payload, …); (2) Determine the threat vector via which an attack is launched (web, email, document, or lateral spread); (3) Determine the malicious behavior (trojan, reconnaissance, C&C, or exfiltration); (4) Provide consolidated threat profiles for the IR team; (5) Extract end-user information from active directory; (6) Allow incidents to be identified by the user name rather than IP addresses or DNS machine names. We should also collect data, such as malicious files, PCAPs, and network telemetry data, as attack evidence to verify an attack and determine effective and appropriate mitigation measures. As for the impact of an attack, it is necessary to evaluate which devices/users are affected and how long the attack has been active (this requires time series data normalized by resource extending back weeks, months, or even years).
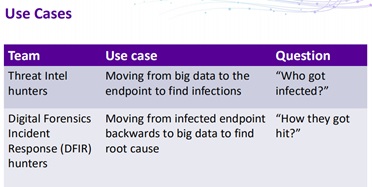
For further clarification, Bilogorskiy provided some use cases:
Figure 9 Use cases
And primary attack vectors:
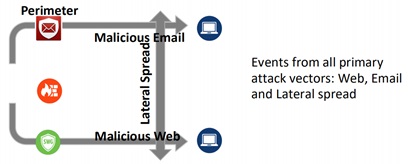
Figure 10 Primary attack vectors
And all the kill chain phases events may span:
Figure 11 Kill chain
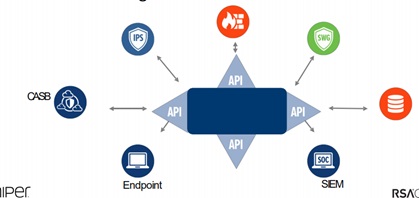
Automation solutions rely on open APIs provided by various products and modules to enable information exchange with other vendors and products.
Figure 12 Open APIs
In response to a security incident, what should we do? Bilogorskiy listed the following tasks: (1) Collect data from web, email, and other possible sources; (2) Analyze/detect advanced threats; (3) Identify infected hosts and users; (4) Ingest metadata from all possible sources; (5) Correlate all related host events; (6) Consolidate events on timeline; (7) Present the security incident. Automation of these tasks can reduce noise from SIEM alerts, eliminate manual correlation, provide insight into threats, and simplify the IR process.
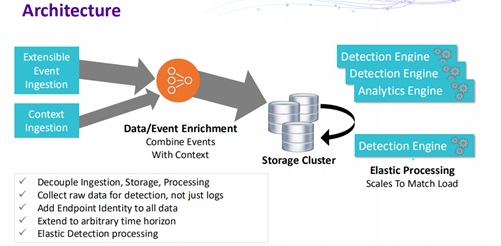
Bilogorskiy illustrated the IR architecture as follows:
Figure 13 Architecture
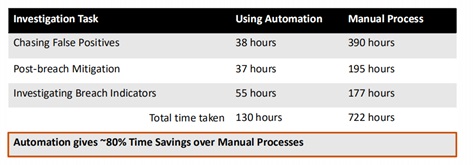
What benefits can automated IR bring to us? According to his company’s practice, Bilogorskiy said that automation saved about 80% of time compared with manual processes.
Figure 14 Automation in action
Bilogorskiy, being worried about the current security situation, ended his presentation with the following reminders:
(1) Attackers are embracing automation to enhance the efficiency and effectiveness, and so should we as defenders.
(2) When done right, machine learning can maximize threat detection.
(3) Human experts are needed to interpret machine learning results.
(4) IR can be accelerated by automating common IR tasks.
The battle between defenders and attackers is, to a great extent, a competition of the speed of action.
NSFOCUS’s latest research reveals that: (1) most Internet business systems get detected and attacked within half an hour after going live; (2) an Internet-facing system is attacked with the latest exploit code within 10 to 13 hours after a vulnerability in the system is made public. The first finding is obtained from a honeypot-based research. NSFOCUS’s researchers found that all honeypot systems became targets of reconnaissance and scanning attacks within 30 minutes after being put on the network, and each suffered 50+ attacks on average. Through continuous observation of these honeypot systems, researchers found that, within 10 to 13 hours after a critical or high-risk vulnerability is made known to the public, honeypots could capture new attacks targeting this vulnerability. All the above data points to a fact that the current Internet in China is imbued with various security threats that are evolving at an alarming rate.
NSFOCUS MDR Service
In the context of both the offensive and defensive techniques and methods evolving unbelievably fast, NSFOCUS, to better help customers overcome imminent threats, launched the Managed Detection and Response service (MDR) in 2018.
MDR is a one-stop security operations support service that integrates the security threat detection device, security threat analysis platform, and security expert service. Thanks to the security devices and platforms, such as Intrusion Detection/Prevention System (IDS/IPS), TAM (for threat analysis and monitoring), and Attack Trend Monitoring system (ATM), and cloud-side remote security analysis experts, MDR can offer professional threat detection and response services of various security threats to enterprise customers.
Compared with traditional security products and services, MDR has the following merits:
- Mitigation of management risks enterprises are exposed to during information security work
Nowadays, information security work of organizations in China often starts with procurement of security devices and platforms. Then they outsource the O&M service to ensure the security of their systems and networks. This model contains great risks in work completion on schedule, staffing, and technical integration. Besides, other factors add to enterprises’ vendor and outsourcing provider management costs and risks. These factors include unified O&M and management of security devices from different vendors, synchronous development of different security devices and platforms, joint commissioning and interconnections, security O&M outsourcing, and recruitment and training of security O&M personnel. It is almost impossible to ensure that an integrated, effective operations system can be built on procured security devices, platforms, and services to tackle increasingly sophisticated security threats.
MDR, as an end-to-end security operations support service that features an integrated design, incorporates the threat analysis platform, threat detection device, and security O&M expert resources. Working on the basis of an architecture supported by techniques, processes, and staffing, MDR effectively help enterprises mitigate risks in security assurance.
- Flexible configuration and controllable cost to reduce the total cost of ownership (TCO)
The MDR service can be procured flexibly. On the one hand, customers can determine which threat detection and analysis devices to buy according to the type and scale of and planning for their business systems. On the other hand, enterprises can choose to rent or purchase security devices or platforms based on their security budgets. Customers that have deployed NSFOCUS’s security devices can choose to purchase the MDR service to expand the original security capacity. Using the preceding methods, enterprises can significantly reduce the initial investment for information security assurance and can then make additional investments as required after confirming the effectiveness of the security operations support service.
- Reduction of the operating expense (OPEX) because of adaption to the original management process
Unlike the traditional model of purchasing security devices, MDR boasts an integrated architecture, which provides threat detection and protection capabilities that seamlessly connect to an enterprise’s original security O&M system. With this service, enterprises do not need to spend extra money on security O&M, thus reducing the OPEX of security operations.
The MDR service is best in class, whether technically or in the service model. It not only provides an integrated security solution for customers but also incorporates the state-of-the-art big data analysis, machine learning, and smart decision techniques for precision detection of security threats and incidents. Thanks to this service, enterprises can continuously and effectively mitigate security risks and reduce costs incurred by security incidents.