Overview On September 8, Beijing time, NSFOCUS CERT found that Microsoft released a security bulletin to disclose a remote code execution vulnerability (CVE-2021-40444) in Microsoft MSHTML. Attackers could craft a malicious ActiveX control to be used by a Microsoft Office document that hosts the browser rendering engine, and convince the...
Ano: 2021
Attack Path Visualization in Security Operations
Cyberattacks are becoming increasingly sophisticated, usually involving multiple steps. This necessitates corresponding protections. Attack path analysis is a process of analyzing detected attacks from the network attributes, alerts, vulnerabilities, and assets, finding out the attack logic, and identifying attack paths. Such analysis can inform security operations personnel in their event...
Atlassian Confluence Remote Code Execution Vulnerability (CVE-2021-26084) Threat Alert
Overview Recently, NSFOCUS CERT found that Atlassian released a security bulletin to announce the fix of the Confluence Server Webwork OGNL Injection Vulnerability (CVE-2021-26084). This vulnerability allows an authenticated attacker, and in some instances, an unauthenticated user, to execute arbitrary code on Confluence Server or Data Center by injecting a...
How to Analyze Security Alarms (1): A Perspective into Data
In today's business security operations, the tide of security information and event management (SIEM) is on the ebb. Many enterprises have established the security operations center (SOC) and collected massive security data. But how to make use of and analyze such data remains a problem to be resolved. Data, after...
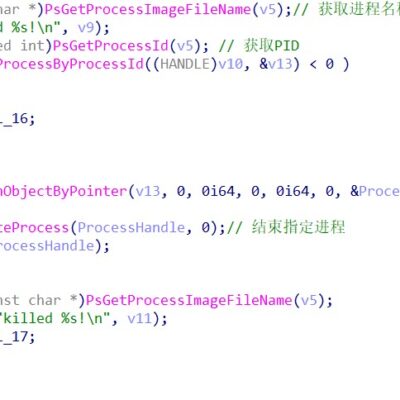
Insights into Ransomware Spread Using Exchange 1-Day Vulnerabilities 2-2
Analysis of the Kill Chain of the LockFile Ransomware Group KDU Tool Terminating Multiple Antivirus Processes The attacker renames the KDU tool (open-source Windows driver loader implementing DSG bypass via an exploit) autologin, copies the related program to the temporary directory, and loads and executes the designated driver file to...
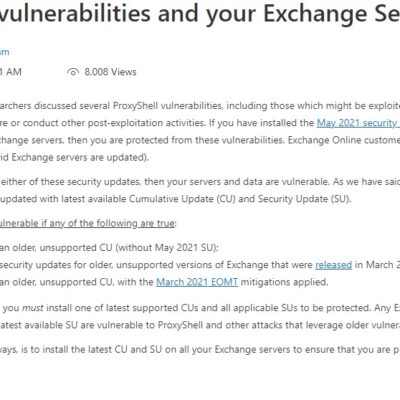
Insights into Ransomware Spread Using Exchange 1-Day Vulnerabilities 1-2
Event Overview Recently, NSFOCUS CERT discovered a slew of security incidents that exploited security vulnerabilities (ProxyShell) in Microsoft Exchange. Also, NSFOCUS found that the new LockFile ransomware group LockFile took advantage of these ProxyShell and PetitPotam vulnerabilities to target enterprise domain environments, finally encrypting quite a few hosts from enterprises...