Cyberattacks are becoming increasingly sophisticated, usually involving multiple steps. This necessitates corresponding protections. Attack path analysis is a process of analyzing detected attacks from the network attributes, alerts, vulnerabilities, and assets, finding out the attack logic, and identifying attack paths. Such analysis can inform security operations personnel in their event and risk analysis so that they can respond to events more promptly. This article discusses the importance of attack path visualization enabled by artificial intelligence (AI) in security operations.
Introduction
With compromise methods evolving day by day, current hackers are no longer content with single-step attacks. Alerts generated by security devices upon detection of an attack usually cannot reveal the attacker’s real intent, but only part of a sophisticated multistep attack. In a sophisticated multistep attack, the attacker carries out the attack step by step to achieve the ultimate end. Generally, we need to associate attack behaviors in each step before finding out the attacker’s real intent. These years, black industry chains related to cyberattacks have emerged on end. Most hacker groups successfully compromise hosts by means of multistep attacks. In a large-scale cyberattack exercise, we found a large hacker group took down multiple companies’ servers for such malicious activities as cryptojacking. Before the exercise, most companies had purchased and deployed protective devices from security vendors. However, many of them failed to discover that their intranets had been compromised. Even if some found the compromise, they failed to take any response measures for assets in the attack paths, inviting more attacks on these assets. Through repeated reviews of cybersecurity exercises, we find that hackers’ attack methods keep upgrading with an increasingly high level of concealment. Besides, multiple factors, including 0-day vulnerabilities, unauthorized access resulting from a low level of security awareness, noncompliant development of applications, and disorder in intranet environments, exist to cause security products to be unable to detect every move of an attack, hence the failure to provide the correct paths of a multistep attack. Moreover, companies tend to deploy security products from different vendors, which cannot work in a coordinated manner, making it impossible to promptly identify all attack paths of a campaign.
In a real-life cybersecurity exercise, experienced security experts are often needed to analyze alerts generated by different vendor’s security products. Besides, these experts’ knowledge is required for a forensic investigation, which will reveal complete paths, facilitating response efforts in each step. How long this process will take depends on what attack method is used, how much information security products can provide, and security experts’ familiarity with this attack method. Another important factor is whether security experts can log in to compromised assets as soon as the attack is detected so as to conduct a thorough investigation of alerts generated by security products. Now, experienced security experts’ analysis is still a must for obtaining complete attack paths aside from various threat detection products already deployed by organizations. In this sense, automating attack path visualization is an important basis for the cybersecurity system to evolve towards AISecOps.
Attack Path Identification
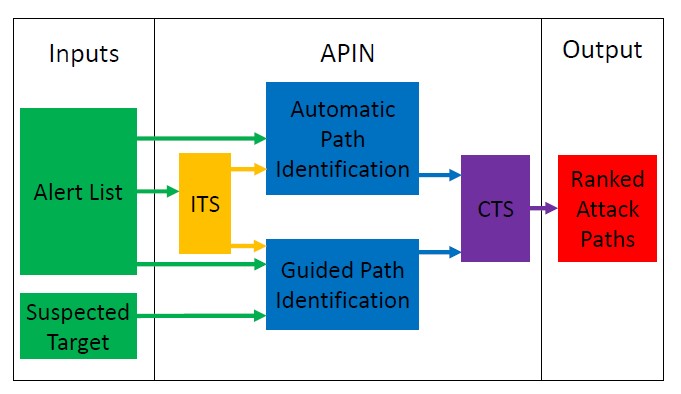
A major method of attack path identification in present days is to create a network-side graph model to extract an attack event from network attributes, threat intelligence, device alerts, and vulnerabilities. Then attack detection rules, data mining algorithms, and association techniques are jointly used to derive the attack pattern before attack paths are inferred or predicted. Take the framework for automatic attack path identification in computer networks (APIN)[1] (see Figure 1) as an example. Under this framework, attack paths in networks are automatically identified by leveraging observable malicious behaviors to quantify the threat score of a set of attacks. ITS stands for the independent threat score quantified based on the graph constructed according to alerts provided. CTS stands for the composite threat score, which is used to quantify the threat posed against a given path as a whole. The framework proposers prove through experiments that it is possible to use public datasets to reconstruct multistep attack paths provided that the network structure and size are limited.
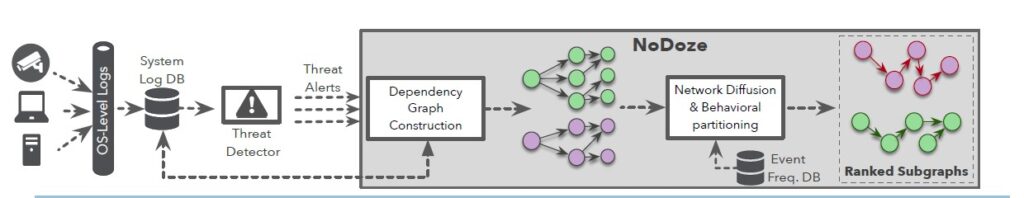
Methods of detecting threats from massive data on the network side and device side are also proposed. As the functional logic of modern operating systems is becoming more and more complicated, it seems especially important to identify anomalies and malicious intents from massive data for detection of potential advanced persistent threats (APTs) or other advanced threats. Considering the technical challenges, such as the dependency explosion of device-side data, identification of threats from vast amounts of data, and low level of scalability, it is very difficult to identify malicious behaviors from provenance data, which involves integrating different types of data to form a provenance graph and using an effective data mining method to reveal the logical dependence between attack behaviors, thus informing various threat hunting tasks. By far, multiple research teams have conducted research on the analysis of provenance graphs. For example, some researchers proposed NODOZE[2], as shown in Figure 2. Its mechanism is as follows: Threat detection devices generate alerts and send them to NODOZE, which ranks these alerts based on their anomaly scores and generates alert dependency subgraphs for security professionals. The core of this approach is to model normal behaviors in the system before an attack happens. The proposers try to resolve the dependency explosion issue by identifying low-frequency paths. Any behaviors deviating from the reference model are taken as attacks. The effect of this approach depends on the relationship between anomalous behaviors and attack behaviors. Typical provenance graph analysis techniques also include HOLMES[3], MORSE[4], and HERCULE[5]. The preceding provenance graph-based threat detection approaches can provide meaningful guidance to identification of attack paths in an attack scenario. But they are still very rudimental in contrast to highly antagonistic, targeted, and persistent cyberattacks that are launched by profit-driven sophisticated hackers. Some experiments set conditions such as limiting attack methods, and others devise scenarios that are much simpler than attacks in the real world.
Up to now, there has been no technique that can effectively detect and visualize attach paths regardless of attack/defense scenarios. How to make different detection and analysis engines work in a coordinated manner to produce all-round visualized attack paths is an inevitable problem that must be resolved for effective security operations in complicated scenarios that involve massive data. Moreover, when visualizing attack paths, we should find a balance between multiple factors, including the cost, efficiency, and data privacy, before bringing related products to life.
After a cybersecurity exercise, we may discover the attack method and path through a retrospective analysis. But the reality is that organizations in China tend to put business above security, so their development teams and O&M teams often speak insincerely when summarizing the exercise. That is why it is so difficult to make security operations a routine job in these companies. Besides, current cybersecurity products are not AI-enabled, making it impossible for companies without security experts to maintain routine security operations. By far, few products can intelligently identify attack paths. Even if some claim that they can automatically and accurately detect and predict attack paths of complicated multistep attacks, most of such claims are more rhetoric than real. In practice, the possibility of these products intelligently providing visualized attack paths is near zero. If a cybersecurity product is as intelligent as its vendor claims to be, it should not only intelligently discover paths of a multistep attack but also reveal related paths of the attacker in his or her lateral movement for further attacks. Only in this way can complete attack paths be visualized in the company’s network threat prevention system and can other modules of the system provide solutions and emergency responses to these threat paths. Finally, all systems in these paths will be remediated, thus ensuring the company’s cybersecurity. This will significantly improve organizations’ cybersecurity capabilities while reducing their security operations costs.
In conclusion, both academia and the industry have conducted research on attack path identification, but have made no substantial progress in intelligent visualization of these paths. This is because, on the one hand, it is impossible to capture every move in a sophisticated multistep attack and it is difficult to provide accurate alerts and attack information; on the other hand, it is hardly possible to intelligently and accurately associate all moves in a multistep attack. Graph analysis techniques are still a good tool to intelligently visualize attack paths. The future research is projected to be around how to build all factors contributing to a successful attack in a complex network environment into a unified, graph-based model. This model will be dynamic, allowing analysis of the context to discover and reproduce attack paths in an intelligent and visualized manner, thus removing the bottleneck of overreliance on security experts in the process of presenting attack paths.
Epilogue
Visualizing attack paths in a multistep attack can effectively facilitate security operations. Doing so intelligently will reduce security operations costs, reshape the current cybersecurity operations model, and make security operations techniques and processes more automated and intelligent, enabling organizations’ cybersecurity capabilities to stand the test of real-world attacks.
References:
- Ficke E , Xu S . APIN:: Automatic Attack Path Identification in Computer Networks[C]// 2020 IEEE International Conference on Intelligence and Security Informatics (ISI). IEEE, 2020.
- Hassan W U, Guo S, Li D, et al. NoDoze: Combatting Threat Alert Fatigue with Automated Provenance Triage[C]. NDSS,2019.
- Milajerdi S M, Gjomemo R, Eshete B, et al. Holmes: real-time apt detection through correlation of suspicious information flows[C]. 2019 IEEE Symposium on Security and Privacy (SP), 2019: 1137-1152.
- Hossain M N, Sheikhi S, Sekar R. Combating Dependence Explosion in Forensic Analysis Using Alternative Tag Propagation Semantics[J].
- Pei K, Gu Z, Saltaformaggio B, et al. Hercule: Attack story reconstruction via community discovery on correlated log graph[C].Proceedings of the 32Nd Annual Conference on Computer Security Applications,2016: 583-595.
