In the last series of popular science, we talked about Zero Trust Network Access (ZTNA) and learned the three critical technologies of zero trust—SDP, IAM and MSG. In this article, we will continue to introduce a security capability of NSFOCUS SASE – the SDP, one of the three major technologies.
What is SDP?
The SDP stands for Software Defined Perimeter, a new generation of network security technology architecture based on the concept of Zero Trust proposed by the International Cloud Security Alliance (CSA) in 2013.
In 1993, the famous American cartoonist Peter Steiner published a world-famous cartoon dubbed “On the internet, nobody knows you’re a dog.”
To solve the problem of verifying whether the remote connection is a human or a dog when you are sitting at the computer, the zero-trust concept of ​​”never trust, always verify” came into being. How to achieve stealth on the Internet, trusted control, and minimal on-demand authorization? Those are what the SDP can do. So how does it do these things?
SDP Implementation Principle
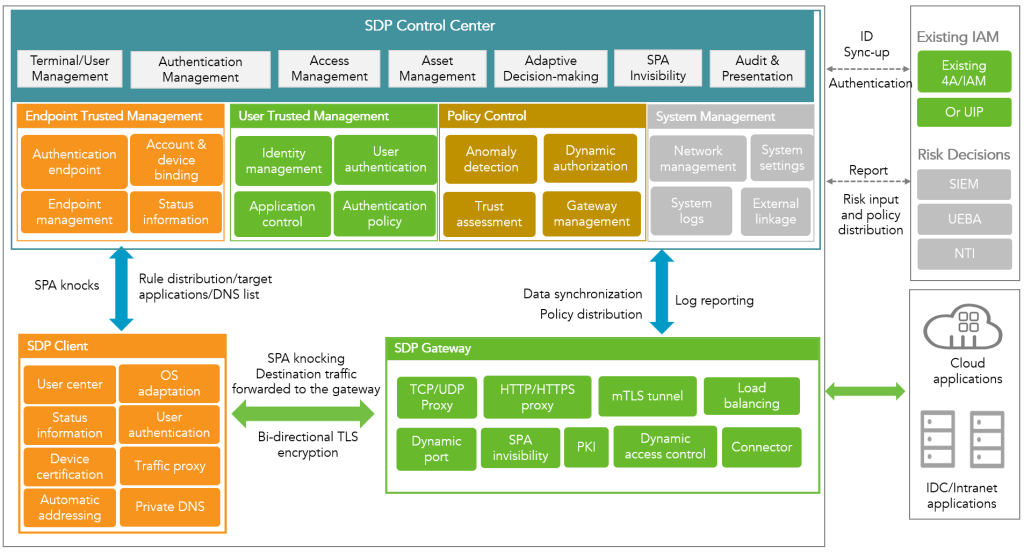
The function of SDP won’t be realized without the three core components: SDP control center, SDP client and SDP gateway.
The SDP control center is responsible for policy configuration, identity or device-based refined application authorization based on identity or device, log auditing, and docking authentication services;
The SDP client is responsible for uniquely identifying the terminal, reporting status information, and initiating single packet authorization (SPA) and authentication requests. It also provides private DNS, and cooperates with business traffic proxy to automatically address application traffic to the corresponding gateway;
The SDP gateway is responsible for service hiding. After the SPA knocking, it opens the dynamic TCP port to the authenticated terminal and implements the specific SDP control center policy after the user passes the authentication.
Three core components of SDP
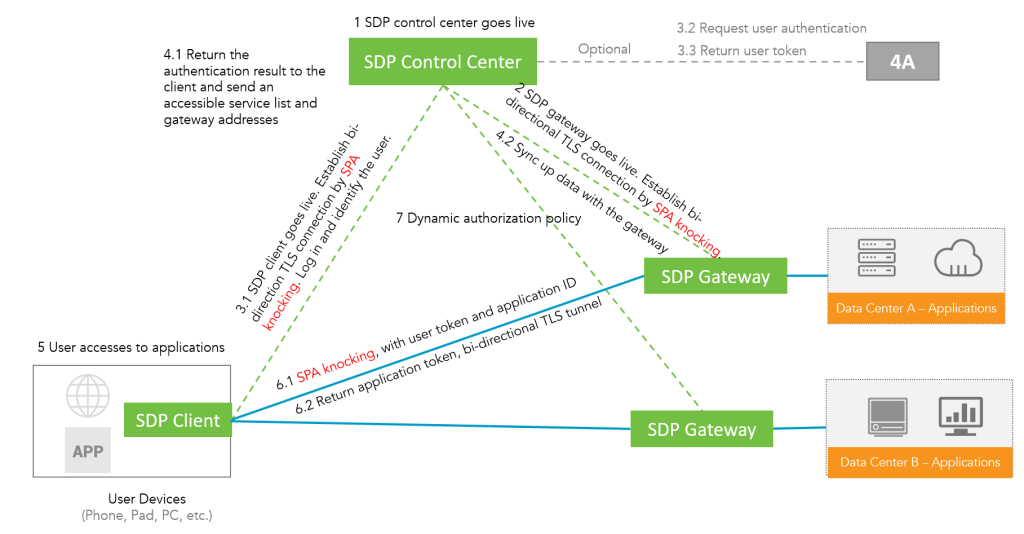
Before the client accesses data, it establishes an authentication and authorization channel through the control plane, the SDP controller and the application server. After the authentication is passed and the access authorization is obtained, the SDP controller determines a list of hosts that the client can be authorized to communicate with. Then the client can establish a data access channel with the application server on the data plane, allowing intended traffic to pass through.
SDP access flow
Once the user can be authenticated, we can be sure who the user is (could be a liar or a dog), and SDP creates a secure encrypted tunnel to protect communications between the user and the requested resource.
Advantages of SDP
So what benefits does it bring to safe deployment? Through the separation of the control layer and the service layer, continuous monitoring and evaluation of the context, it provides on-demand minimum authorization and mutual TLS communication encryption to ensure the security of the link. SDP can effectively deal with many network security threats, including:
- Data Breach
Reduce public exposure and implement a “least access†model to reduce data leakage.
- Weak Identity
Identity-centric, restricted access makes the security architecture more resilient to weak identities, credentials and access management.
- Insecure System Interfaces and APIs
Unauthorized users (i.e. attackers) cannot access the interface and therefore cannot exploit any vulnerability.
- Business System and Application Vulnerabilities
SDP significantly reduces the attack surface and hides the vulnerabilities in business systems and applications.
- Account Hijacking
Web requests carrying hijacked session cookies not pre-authenticated and authorized will not be accessed by the SDP gateway.
- Malicious insider threat
Restrict insiders’ access to only those resources needed to perform business functions and all other resources will be hidden.
- Advanced Persistent Threats (APTs)
Implement multi-factor authentication to limit the ability of infected endpoints to find network targets, and reduce the spread of APTs.
- Data Loss
Reduce the possibility of data loss by hiding network resources from unauthorized users through the principle of least privilege.
- DDoS Attacks
SPA can consume fewer resources than typical TCP handshake connections, enabling servers to process and drop malicious network request packets at scale.
SDP in SASE
Now we know the advantages of SDP. Next, let’s see how these advantages are reflected in SASE products.
First of all, SDP exists as an optional application publishing mode in the SASE-NPA service, which provides security, convenience and stability for enterprise application access.
Security is reflected in the fact that SASE can use the SDP technology to hide all kinds of applications deployed by customers on the cloud or locally, as well as the gateway IP and port of the cloud service itself. Only legitimate users can see the application, and hackers cannot scan corporate assets. This capability can well solve the problem of increased Internet exposure after asset cloudification and multi-location deployment, and comprehensive network and application cloaking makes it impossible for attackers to start.
Convenience is mainly reflected in the fact that enterprise users access the enterprise intranet anywhere through the Internet. Only deploying an agent on the user terminal can make users quickly access NSFOCUS SASE at any location and securely access back-end applications, which can avoid the dilemma of small carrier operators cannot establish VPN tunnels in the past.
Stability is another feature as SDP uses short links instead of VPN tunnels built by traditional VPN technologies. So it is more tolerant of poor network conditions, providing a more stable access experience without lagging and dropouts.
Finally, if we use a metaphor o describe SDP, we will say that SDP is like adding “Harry Potter’s invisibility cloak” to a safe so that attackers cannot find it, while authorized users of the enterprise are granted “Moody’s magic” Eye”.
Previous posts:
- NSFOCUS Empowers ISP/MSP with Zero Trust and Security Access Service Edge (SASE) Solution
- Zero Trust Network Access (ZTNA): Never Trust, Always Verify
- CASB, A Tech “Celebrity†from the Cloud Era
- SASE: The Relationship Between SD-WAN and SASE
- SASE Popular Science Series – Understanding SD-WAN
- SASE, Born for Digital Age