After the prior two posts (SASE Popular Science Series – Understanding SD-WAN and SASE: The Relationship Between SD-WAN and SASE), you may already have a basic understanding of SD-WAN, which is used for network connections among users, assets and NSFOCUS Cloud in SASE. What security capabilities does NSFOCUS offer then? In the next few sessions, we will introduce one by one. Today’s topic is ZTNA, the core access control capability of SASE.
What is ZTNA?
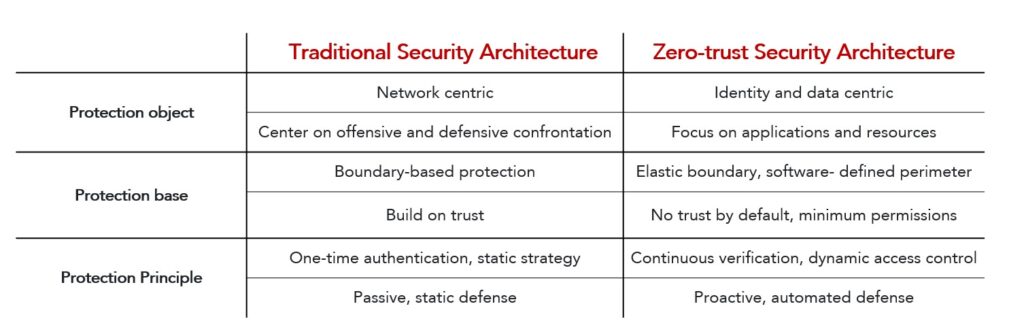
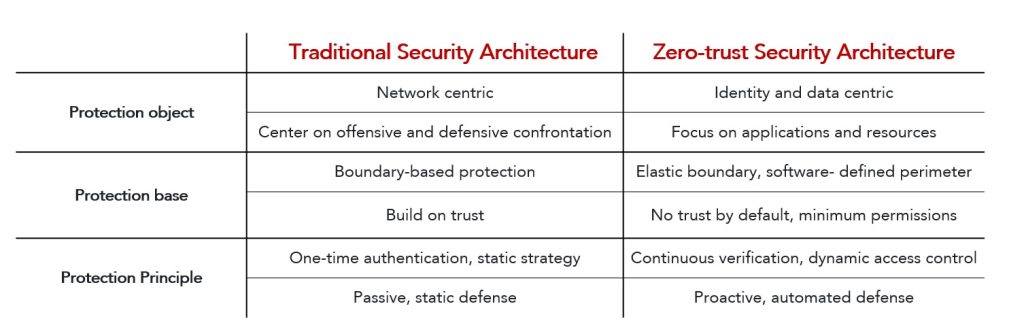
Since the early 1990s, enterprises have been using endpoint-based access control, relying on approved IP addresses, ports and protocols to verify applications, data and users and then trust them to allow the communication in the internal network. The traditional VPN gives trust based on IP address.
However, with the diversification of office scenarios, more and more users begin to use unmanaged devices to connect to enterprise applications through the Internet, which leads to unexpected security vulnerabilities when companies trust individuals or devices too much. In the BYOD scenario, ZTNA came into being.
ZTNA, zero trust network access, specifies that, any user (even if allowed to enter the network) should not be trusted by default. Every device and user needs to be verified in the whole network access process, not just at the boundary, and minimum access permissions are allowed based on device authentication during the access process.
In short, before the emergence of zero trust, as long as you access your intranet via your company’s VPN, the network will identify you as safe and allow access to all intranet resources. However, with ZTNA, the intranet will no longer provide IP address-based trust, but verifies your identity and your device, and provides corresponding access permissions according to your identity.
ZTNA’S Working principle
Since ZTNA has changed the traditional security mode, it must have its unique operation approach. Let’s see how zero trust does.
Zero trust security is the minimal permission security. When accessing resources like applications and data, users must first ensure its own security and is granted the minimum permission to establish an access session after authentication, followed with continuous verification. Once any abnormal behavior is discovered, the control policy will be dynamically adjusted, including reducing the access level, doing secondary authentication, even cutting off access sessions.
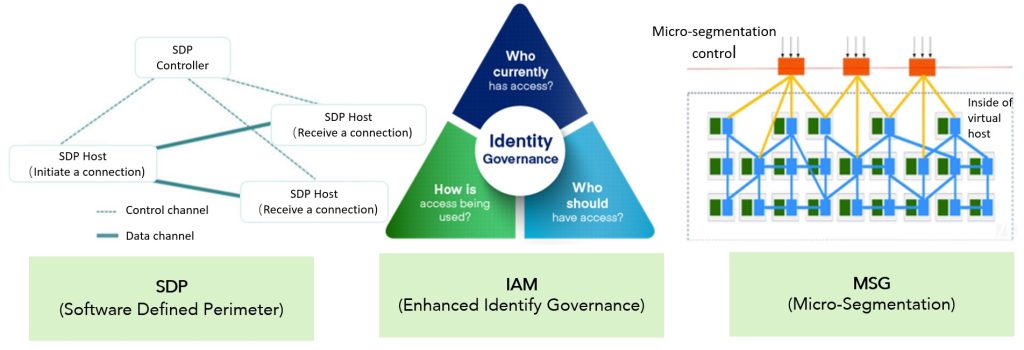
In the whole access process, SDP, IAM and MSG are the three key technologies:
SDP client performs multi-factor authentication, and then enters the user login stage. After authentication, the client can establish a connection with the server.
IAM has the capabilities of single sign-on, authentication management, central policy-based licensing, auditing, and dynamic authorization and so on. IAM decides who can access, how to access, and what can be operated.
MSG micro-segmentation is a fine-grained network segmentation technology, which can deal with the traffic segmentation of the traditional environment, virtualization environment, hybrid cloud environment and container environment, and prevent the horizontal translation of attackers after they enter the enterprise data center network.
These technologies work together to create a truly zero-trust access control.
Advantages of ZTNA
The protection mechanism of zero trust appears to be a little complex. What benefits does it bring?
First, only legitimate users can establish a connection with authorized applications. Enterprise applications are invisible on the public network. Through asset “stealthâ€, the security of enterprise digital property is fundamentally protected from the source of the attack chain.
Second, giving permissions to internal employees based on their identity in the organizational structure and allowing them to access their needed applications and resources only can reduce the risk of unauthorized access.
Finally, user’s behavior will be continuously monitored, and anomalies will be discovered and blocked timely.
ZTNA of NSFOCUS SASE
In NSFOCUS SASE product management interface, enterprises can launch new applications and publish applications using SDP mode, hiding applications’ real IP addresses and having the enterprise applications invisible and unreachable in the public network.
Enterprise’s internal access authorization is determined by the organizational structure. Employees of different departments and levels correspond to different authorization ranges, realizing the identity-based fine-grained access strategy and ensuring the minimum authorization on demand. Users’ access context is continuously monitored, and abnormal behavior detection and terminal exception detection are built in. In this way, anomalies are handled and blocked timely. If necessary, it can require a user to do a second authentication or can lower a user’s permissions.
After reading our SASE product introduction, I believe you have a deeper understanding of the access strategy of zero trust. For more security capabilities of SASE products, please look forward to the follow-up.