2020 is almost halfway through, it is indeed a troubled period. Covid-19 swept all over the world in just a few months. The epidemic continues to spread and repeat, and has also changed many people’s inherent perceptions, including health care, public safety, organizational mobilization, economics and politics.
The concept of computer virus is derived from biological virus. There are certain similarities between the two, such as mutation, transmission, infection mechanism, etc. Once a malicious software breaks out, the consequences caused are equally serious. A typical example is the ransomware WannaCry that took advantage of the NSA’s Eternal Blue in 2017. It infected 200,000 computers in 150 countries in just a few days, even paralyzed the production lines of manufacturers such as TSMC, broke through physical isolation and destroyed important assets of the intranet. It greatly impacted people’s inherent concept of cyber attacks and cyber warfare.
Analyzing and summarizing the gains and losses from ways of responding to the epidemic across countries may inspire cyber security professionals in dealing with future cyber attacks. The following points are worth discussing.
Economic (business) development vs Public (network) security
Reflection: It is not feasible to only emphasizes economic development and neglects public safety.
There is no doubt that the development of the epidemic will bring negative impact on the economy. At the end of February 2020, when the epidemic began to spread around the world, as an economic indicator, the stock markets of various countries fell sharply, as shown in Figure 1[16], which reflected concerns about future economy. After the outbreak in the United States, the three major U.S. stocks experienced 4 unprecedented circuit breakers within ten days from March 18. Later, the states adopted measures such as blocking cities and restricting gatherings, which gradually reduced the daily growth rate of infections. On April 17, the United States announced guidelines to restart economic activities, and in May the states reopened and the economy started to recover. However, in June, the number of confirmed cases of Covid-19 infection in a single day rebounded in some states. Due to concerns about the second wave of epidemic, the three major U.S. stock markets fell by more than 5% on June 11, the largest decline since March.

Figure 1: Covid-19‘s Influence on Economy
In the IT field, security always aligns with business. The ultimate goal of security is to ensure the normal business operation and reduce the loss caused by attacks. Therefore, the security team will also encounter similar situations. When a business is vulnerable or facing specific threats, does it need to be dealt with promptly? A prompt reaction may impose an unpredictable impact on the business availability, but if not, the business will be broken with more serious consequences. If it is a critical business (industrial control equipment) or an important business (core financial service), does CXO have the determination to act decisively? It seems to be caught in the same dilemma as US President Trump.
The most representative example is the Target data breach in 2013[17]. At that time, the security team discovered several attacks, but it happened during the Black Friday promotion, and they believed that attackers would not take further action. But in fact, attackers stole 40 million sensitive information such as credit and debit cards. After the incident was exposed, Target’s stock price, revenue and profits were greatly affected, and its CEO resigned in the following year.
Action: Balance business gains and risk losses
Compared with the United States, China handled the outbreak in Wuhan more decisively. Although the economic development of a metropolis with a population of 10 million is very important, there are lessons learned from SARS in 2013. Considering the serious consequences of virus spreading, Wuhan government took extraordinary measures to close the city at a critical moment, which is of vital importance to curbing the spread of the virus.
The fight against the virus is dynamic. Different nations, different people, and different epidemic situations will lead to different methods. The purpose is to ensure economic development and the stable operation of society under the premise of controlling the epidemic.
The same is true for network security. The goal of the security team is to protect various security attributes of the business, but considering that attackers will use various means to attack, there is no absolute security. Security is relative, dynamic, like a game. If the attacker fails under certain cost constraints, the defender can be considered to win. Therefore, the security team should analyze its own security objectives and the risks in current environment, investigate, design, deploy and operate various security mechanisms to increase the cost and difficulty of attackers under the constraints of a given budget and cost, then reduce the loss caused by the destruction.
Specifically, decision makers need to take a part of the cost from business investment into safety. Once it takes effect, the loss regained from this part of security investment is the safety gain, but the benefit from this cost does not increase linearly, so decision makers need to find a balance point. Table 1 illustrates the relationship between the cost xi of various safety inputs and the loss yi caused by avoiding risks. Under the constraints of ensuring that one’s own risk is controllable, adjust one’s own various safety inputs (xi) to minimize risk losses
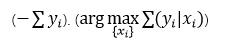
Table1: Balance between safety inputs and gains
Battle vs war
Reflection: Do not be rush to succeed
The coronavirus did not disappear in the summer like SARS, but instead took advantage of the lack of strict precautions and poor sanitation in some countries to continue to spread around the world. The high mutation rate and infectivity of coronavirus make WHO experts believe that it may never disappear [1]. Some Chinese experts also believe that the virus may become chronic and exist in human society for a long time [2].
Computer viruses also mutate and are contagious. They will continuously attack accessible vulnerable assets and continue to spread as an intermediate host. Therefore, it is unrealistic to hope to solve certain types of attacks through just one effective defense. Just like “Plants vs. Zombies”, security teams often encounter series of attempts and attacks.
For example, in 2016, the Mirai malware launched a >1Tbps DDoS attack for the first time, attacks from its variants can still be found. Our IoT threat acquisition system has been able to capture the detection of attackers using N-day vulnerabilities, and the botnets of major malwares are always active.
Battles are short-term, but wars are long-term contests. Fighting against various cyber attacks is not an one-time effort for security teams. The attack and defense are a long-term, continuous, and struggling war.
Action: Continuous risk assessment and mitigation
Security warfare is a long-term war, a dynamic process of ebb and flow. The focus of security protection is the risks faced by assets. The risk value is affected by various factors, such as attacker’s capabilities, constantly emerging vulnerabilities, changing business, changes in deployed security mechanisms and policies, etc. Although the asset risk obtained by the combination of the above factors at a certain moment is very low, its risk value will continue to change over time. If an attacker takes advantage of a slack moment of the defensive side of, he may succeed.
Therefore, the core of the adaptive security concept proposed by Gartner is CARTA (Continuous adaptive risk and trust assessment), which is a continuous adaptive assessment of the current balance of risk and trust. The so-called risk is the possibility of occurring problems, and the so-called trust is the confidence in the normal operation of the business. Obviously, no matter in the epidemic scenario or the safe operation scenario, both are dynamically changing, and only the possibility is unrelentingly Only by staying vigilant to new vulnerabilities and threats can we be confident in dealing with more challenges.
Border and control strategy
Rethinking: “Put Strong troops at the border to retreat the enemy outside the country” is unreliable
Relying on the heavy-guarded borders to defend enemies, this thinking not only exists in real world, but also has a broader impact on people’s reaction to crises including the epidemic and network security.
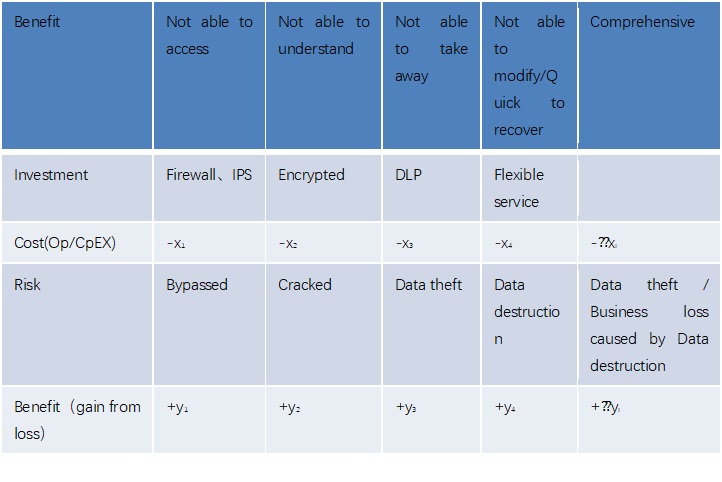
The United States announced in early February that it would close its borders to foreign citizens who had been to China, and on March 11 imposed a travelling ban on Europe excluding the United Kingdom. The United Kingdom began to adopt herd immunity but caused the wide spread of epidemic. From Figure 2, we can see that the number of deaths in the United Kingdom[4] and the United States[5] has been increasing since mid-March. It can be seen that the United States may be right to close the border from China, but it ignored that the virus can be brought from other countries. Just as Germany bypassed the Maginot Line in 1940 and broke into France from its border, history is repeating itself.
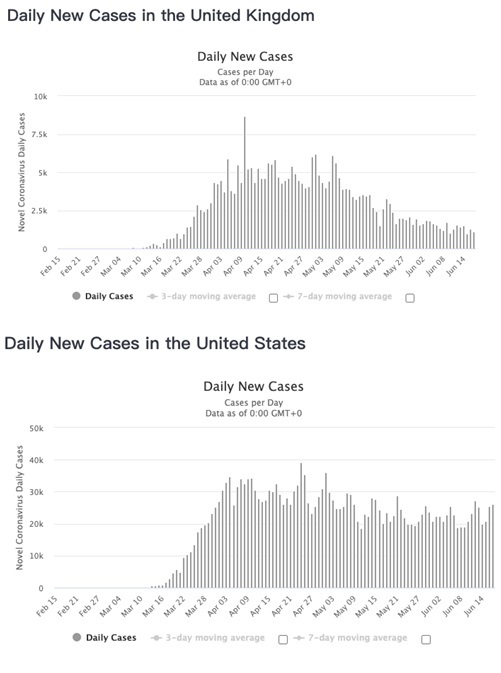
(a) New cases of new Covid-19 diagnosed in the United Kingdom
(b) New cases of new Covid-19 diagnosed in the United States
Figure 2 T New cases of new Covid-19 diagnosed in the United Kingdom and the United States
Going back to network security, a network security system based on firewall, intrusion detection and protection system, and anti-virus software has long been unable to withstand zero-day attacks, let alone advanced threats supported by the state-level and equipped with advanced weapons. Although the security industry keeps developing various technologies, data leaks and breaches have been emerging non-stop. That period was indeed a “dark age”.
Initiative: Reestablish boundaries and trust models
First of all, isolating dangerous factors is always our first thought when dealing with unknown threats. Therefore, the concept of borders is not problematic, but the core question is: where should the border be deployed and who should it defend against? Whether it is enemy bypassing the border or insiders destroying the border, the essence is that the border has not changed within the current situation. The former means that the border does not change according to the enemy’s action, and the latter means that the object of border defense has changed, so, to break through the “Dark Age”, it is necessary to construct a border that can be dynamically deployed between one’s own side and the enemy.
Specifically, a new border should have the following characteristics:
First, the border granularity should be fine enough to be close to the defensive target or individual enemy at any time. In the epidemic scenario, we not only can isolate the national border, but also draw a boundary for cities, streets, communities, families, and even individuals. Even if there is a diagnosed case, or asymptomatic case, or close contacts, they can be reliably isolated nearby without affecting other uninfected people.
We usually call this “Micro-Segmentationâ€. It first appeared in cloud computing systems. It is easy to achieve fine-grained isolation and access control through NFV and SDN technologies. With the further development of 5G, edge computing and SDWAN, this technology will be more widely used in traditional environment.
Second, the borderline can be adjusted at any time to closely follow the trajectory of the normal population (business) and abnormal population (attackers). The border policy can be updated at any time according to the context, and the access rules can be adjusted in time when the visitor or the visited object changes.
In the epidemic scenario, China has creatively introduced a unified “health code†mechanism. Each individual’s code corresponds to three risk levels of high, medium and low, and this level is related to their location (inherent attribute) and motion trajectory within 14 days (dynamic attribute), reflecting the threat level of the individual. Of course, the granularity of each border is different, thus the strategies followed are also different. This invisible border isolated a large number of people at risk, restricted their scope of motion, and helped epidemic in China declined rapidly.
Going back to network security, network access is based on identification (IP, MAC), so the rules of traditional firewalls are also based on network identification instead of the visiting subject and the accessed object identification. Therefore, as business transfers, attackers obtain resources like a gangplank, they are likely to bypass the existing rules of the firewall. In recent years, the industry has been discussing the concept of Zero-Trust. For example, the software-defined boundary proposed by CSA, and BeyondCorps by Google are all technical routes that embody the zero-trust. The zero-trust system requires major adjustments on the previous network access mechanism and access control model, so it has a significant impact on visitors and business, and therefore poses great challenges to its application. Of course, witnessing the good results of the dynamic access mechanism under the epidemic, its prospect appears very promising.
In the follow-up, we will introduce “Book Security vs. Actual Security”, “Epidemiological survey vs. Source tracing”, “Wait a minute vs Do it now”, stay tuned.
References:
[2] https://world.huanqiu.com/article/3x7Ezm6ETNY
[3] https://www.bbc.com/zhongwen/simp/world-51329860
