Biological virus and computer virus share similarities in some characters such as transmissibility. From the solutions to the COVID-19, we can learn the gain and loss of cyber security defense and protection, analyze the new trends and techniques and come up with the new ideas of defense and protection against attacks in the cyber security industry.
Security in book value VS security in real value
Reflection: the idea that “less check, less report†doesn’t work.
There are two examples against this idea. One happened in Japan. Given the upcoming 2020 Tokyo Olympic Games, the Japanese government at the preliminary stage of COVID-19 pandemic took a passive approach, which didn’t publicize the real number of affected patients and only tested the severe cases. As a result, the Japanese cases made public were quite different from those of Korea and Germany. The tested cases and confirmed ones in Japan were too small, while the positive COVID-19 rate was too high. The research of Keio University Tokyo showed that 6% of the patients admitted in hospital due to other pathological causes turned out COVID-19 positive in the PCR test. [6].
The other example took place in the US. The data on May 11 showed when 40 states locked down, the whole US was in short of testing kits. The average number of cases tested was much less than that in Italy and Germany. However, in April the New Coronavirus Tracking Project of US showed that the positive rate reached 20% after 3.57 million persons were tested.
Superficially, the less were tested, the smaller was the number of affected cases. But those positive but not checked must result in more severe cases.
Wuhan experienced a similar early stage due to insufficient testing capabilities. The scenario at that time was quite the same as the two examples above. With only a few cases confirmed, suspected cases flocked to hospitals. In contrast, Wuhan adopted clinical diagnosis as a confirmation method in mid-February. On Feb. 13, the confirmed patients of COVID-19 amount to 14,000. (Image 3) Although this number increased considerably, the whole view appeared no longer vague with accurate and reliable data. Later on, as more and more nucleic acid tests were taken, China implemented a nationwide policy of “all those in need are tested and all those who want a test are testedâ€. Afterwards, the number of daily new cases in China decreased dramatically. [9]
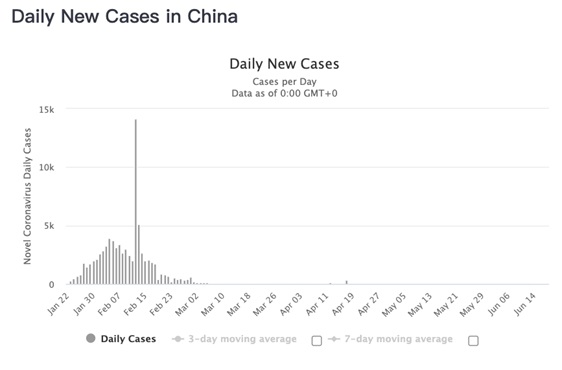
Image 3 Daily New Cases in China
In the field of cyber security, the current calmness doesn’t mean that everything is fine. No defense, no incidents. It seems safe but not secured.
Even if several security mechanisms were deployed, there still would be problems without a coordinated scheme. A single security mechanism only can check or respond to treats from one source. Lack of an overall and thorough induction will lead to incorrect evaluation of the status quo.
Measures: to build an overall and thorough sensing competence.
The competences in full-scope awareness, threat targeting and consequence prediction shall be prepared in advance when the cyber menaces are checked. More and more experts agree with the concept of visibility. You can tell it from the two metaphors below. The analysis of battlefields’ complexity place emphasis on scouts. The penetration into darkness relies on small bells and thermal imagers.
In practice, we acquire the visiting behavioral info. from global network via all types of flow statistics tools like Netflow, OpenFlow and so on. And we aggregate, associate and form a globally consistent analysis result by means of in-depth package testing and end behavior testing. Then we are enabled to provide visibility at different levels of needs. Further, active prevention mechanism such as deception technique deploys a variety of baits, monitor abnormal visiting behavior, tempt the attackers to expose themselves and tell their identity and objectives.
Epidemiological survey vs tracing to the origin
Reflection:the virus origins from the bat, the mink or the salmon?
A decade ago, SARS came and left without a trace. In the following 15 years, Wuhan Institute of Virology, Chinese Academy of Sciences explored 28 provinces and finally sourced the corona virus in bats from the Yunnan province, a natural habitat for SRAS. The COVID-19 epidemic broke out in Wuhan. But the World Health Organization (WHO) has confirmed the virus origins from nature according to the gene sequence analysis. What are the intermediate and natural hosts of COVID-19? The transmission routes are still to be confirmed.
Epidemiological survey is a significant subject to track the virus origin and control COVID-19 from the fundamental solution to the epidemic.
Measure:overall survey to trace to the origin
In February, at a department store in Baodi District, Tianjin municipality,China occurred an outbreak in clusters. Centers for Disease Control (CDC) sorted out the contagion path and sphere of influence after meticulous investigation and analysis, which was commented as a textbook level epidemiological survey.
In the cyber security sector, forensics is a niche subject. Forensics stands for protection, collection, verification and authentication of electronic evidences in the computer system and internet flow. Tracing the source of evidences happened after the attacks, including the detection of attacking timeline, attacking means and spheres of influence. In the next step, moves will be taken, like resuming business, upgrading, reporting and so on. Besides assistant to the system restoration, Tracing the source of evidences plays a crucial role in judicial practice. Therefore, it also deserves the attention of management team.
Those who wait and wait vs those who roll up their sleeves
Reflection: Breaking the early transmission routes means getting the upper hand over virus.
As collaborated above, the biological and computer viruses share a lot in common. They both transmitted in a speed growing exponentially. Without early intervention, the epidemic probably will burst out after some time. At that time, the virus will be out of control.
The epidemic in US experienced two stages. At the first stage prior to April, it turned out no enough efforts were made to call up the public. The US government expected the miracle disappearance of COVID-19 in the summer. Later, the number of confirmed cases grew exponentially. After this lesson, The US CDC proposed “flatten the curveâ€, i.e. active intervention, to decrease the infected number dramatically. (Image 4(a)). At the second stage starting from Apr.1, several states issued the home quarantine order. The increasing rate slowed down obviously. (Image 4(b))
The virus transmission is a scientific question in essence, captured in statics model. No early intervention, no miracle. Those who await miracle and put their hope on temperature change deluded themselves with a fancy. In front of real crisis, the sleeves shall be rolled up and then the lost time shall be taken back.
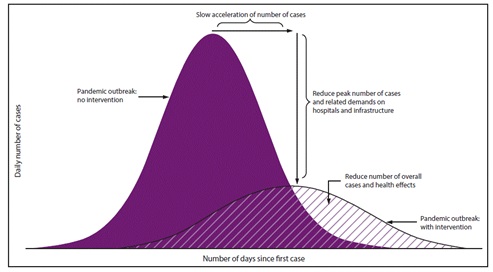
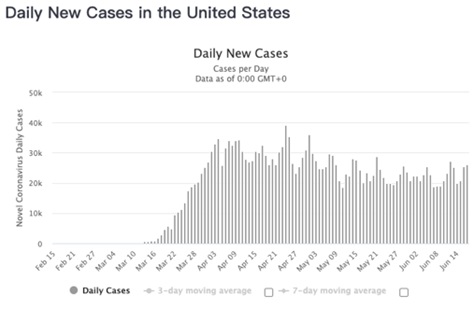
Image 4 the confirmed cases
Considering the balance of economic development and public security investment, it’s impossible that the curve was flatted to a straight line. But no doubt that the more measures taken effectively and accurately, the slope of curve would be smaller.
Back to the topic of cyber security, in the mechanism without active immunity and upgradation, the number of nodes attacked by worms soars but won’t decline at last. The worm will keep attacking all the week nodes. When there’s upgradation, the curve will converge to the line, which means that all the nodes were infected. (Image(5)) More severely, the computer worm acted more quickly will attack all the reachable nodes and spread virus and execute malicious codes automatically. Therefore, the slope of infectious curve of computer virus is bigger than that of biological virus. And the computer virus spreads faster.
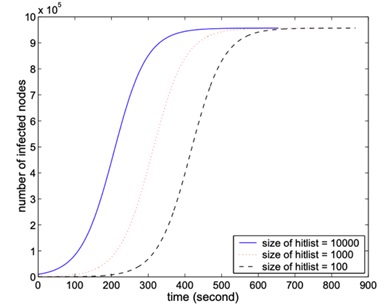
Image 5 change of infected nodes by time without security mechanism.
The security team not only need to deal with the nodes in the pure color part of image 4(a), but also flatten the curve as quickly as possible like the dash-line filled part of image 4(a).
Measure: Speed is the solder’s asset. Respond in an automatic way.
The key to curve flattening is early response. Meanwhile, the first step of response is to tracing and predicting. On one hand, the security team shall block attacks, delay the infectious speed and decrease the number of infected nodes. On the other hand, the security team shall resume the business as early as possible and minimize losses. In general, response by people will flatten the curve of infected nodes to the blue one in Image 6.
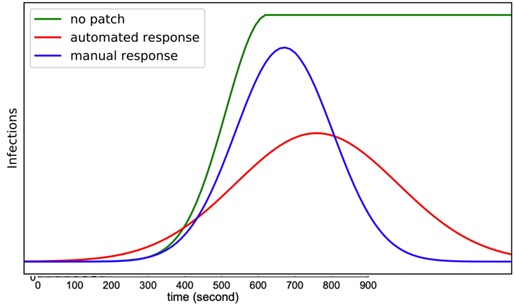
Image 6 automatic response to flatten the infected curve
The next step is to flatten the curve via automatic response to the red on in image 6. Back to 2013, Gartner proposed the idea of “software-defined security†from the idea of “software-defined†internet. The agility and flexibility of the whole security system will be enhanced by separating the control and data. Under this methodology, the automatic arrangement security system of Phantom in 2016 was recognized by industry. Later, the automatic response system SOAR was developed.
The automatic arrangement security engine can deploy the security resource in seconds, control the suspected flow quickly and adjust the security strategy flexibly. Even though the attacker is quick, the defender will be quicker to isolate the suspected business, block the malicious attacks and resume damaged business.
Conclusion
The COVID-19 pandemic is still on. Although US has restarted its economy, its daily increase of patients on June 26 reached the same high level as that in the most serious situation. On the other side, the virus reoccurred in Beijing China but was still in control. As the fight against the biological virus lasts, the attack and defense in the internet will never end. Only by learning from gains and losses and adjusting strategies, can we take the lead and win the fight against virus.
References
[6] https://www.bbc.com/zhongwen/simp/world-52484609
[7] https://cn.chinadaily.com.cn/a/202005/12/WS5eba6e1ca310eec9c72b86b3.html
[8] http://world.qianlong.com/2020/0420/4016055.shtml
[9] https://www.worldometers.info/coronavirus/country/china/
[10] https://tech.sina.com.cn/d/f/2020-01-20/doc-iihnzhha3638660.shtml
[11] http://language.chinadaily.com.cn/a/202006/19/WS5eec0ba3a31083481725413b.html
[12] https://www.zhihu.com/question/31346652/answer/52049615
[13] http://www.bjd.com.cn/a/202002/03/WS5e37d067e4b002ffe994092e.html
[14] https://www.livescience.com/coronavirus-flatten-the-curve.html
[15] http://www-unix.ecs.umass.edu/~lgao/paper/AAWP.pdf
[16] https://www.bbc.com/zhongwen/simp/business-51731992
[17] https://wjla.com/news/business/target-ceo-fired-following-last-year-s-security-breach-102788
