Overview Recently, NSFOCUS CERT detected that Fortinet officially fixed a remote code execution vulnerability (CVE-2022-42475) in FortiOS sslvpnd. Due to the flaw in sslvpnd's validation of user input, an unauthenticated attacker can trigger a buffer overflow by sending a specially crafted packet, which can eventually execute arbitrary code on the...
Categoria: Blog
Thinkphp Remote Code Execution Vulnerability Alert
Overview Recently, NSFOCUS CERT has monitored that the exploit details of the Thinkphp remote code execution vulnerability are publicly disclosed on the Internet. Due to the incoming parameter inspection defect in the Thinkphp program, when Thinkphp enables the multilingual function, unauthenticated attackers can pass in parameters through get, header, cookie,...
Security Researcher from NSFOCUS Security Labs to Speak at Black Hat 2022 Europe
Gao Jian at NSFOCUS Security Labs was invited to speak at the Black Hat 2022 Europe held at ExCel London, United Kindom from December 5 to 8, 2022. Gao Jian specializes in industrial control system security, focusing on PLC and SCADA vulnerability exploitation and ICS security enhancement. He has helped...
Google Chrome V8 Type Confusion Vulnerability (CVE-2022-4262) Alert
Overview On December 5, NSFOCUS CERT found that Google officially released a type confusion vulnerability (CVE-2022-4262) in Google Chrome V8. A type confusion error occurs because a program uses one type of method to allocate or initialize a resource, such as a pointer, object, or variable, but then accesses that...
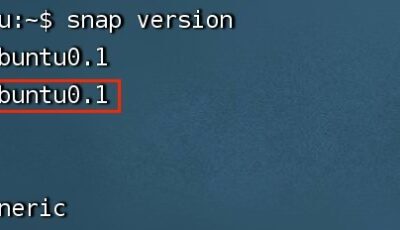
Snapd Local Privilege Escalation Vulnerability (CVE-2022-3328)
Overview On December 2, NSFOCUS CERT detected that Qualys released a local privilege escalation vulnerability (CVE-2022-3328) in Snapd. There is a conditional race vulnerability in the must_mkdir_and_open_with_perms() function in snap-confine, an attacker with normal user privileges can use Multipath Privilege Escalation Vulnerability (CVE-2022-41974) and Multipath Symbolic Link Vulnerability, bind the...
Security Concept for Software Supply Chain (Part 1) — Transparency of Software Supply Chain Compositions
Software supply chain security covers the whole software life cycle. In terms of software product complexity alone, apart from the software itself, it is necessary to ensure the security of the dependencies and transitive dependencies of software, as well as the security of the software ecosystem composed of these dependency...