By: Stephen Gates, Chief Research Intelligence Analyst, NSFOCUS It’s no secret that DDoS attacks are on the rise. Statistic-after-statistic, report-after-report, all say the same thing about DDoS. However, who are the companies that have perfected the technology, tactics, techniques, and procedures used in front-lines to defeat DDoS attacks every day? NSFOCUS...
Categoria: Blog
Swearing Trojan Exploit Overview
Author: Cody Mercer - Senior Threat Intelligence Researcher Executive Overview A new mobile banking Trojan titled ‘Swearing Trojan’ has been discovered by Tencent Security and Checkpoint researchers. The odd name of the malware is in part attributed to the various Chinese swear words sparsely distributed in the source code. The...
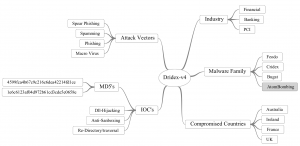
Dridex – v4
Author: Cody Mercer - Senior Threat Intelligence Research Analyst Executive Overview A newly discovered modified version of Dridex, now termed ‘Dridex v4’, has been recognized in the wild in recent days. The upgraded version of the Dridex Trojan was at one time one of the most successful bank Trojans originally...
Dahua Cameras Unauthorized Access Vulnerability Analysis & Solution
Overview Dahua Technology, a well-known security camera and digital video recorder (DVR) vendor in China, released firmware updates to address serious security vulnerabilities for several of their products. By exploiting this vulnerability an attacker can access the user database of a Dahua camera without needing administrative privileges and extract the...
StoneDrill – Shamoon & Shamoon 2.0 Variant
Author: Cody Mercer - Senior Threat Intelligence Researcher Executive Summary It would appear that a new variant titled 'StoneDrill' has now hit the wild and conducts operations very similar to that of Shamoon 2.0 and Shamoon malware. Moreover, Kaspersky Labs has evaluated the source code and it appears to contain...
Apache Struts2 Remote Code Execution Vulnerability (S2-045)
Overview Apache Struts2 is prone to a remote code execution vulnerability (CNNVD-201703-152) in the Jakarta Multipart parser plug-in. When uploading a file with this plug-in, an attacker could change the value of the Content-Type header field of an HTTP request to trigger this vulnerability, causing remote code execution. For details,...