Santa Clara, Calif. January 26, 2023 – NSFOCUS, a global provider of intelligent hybrid security solutions, announced today that it has been selected by Forrester as a sample vendor for its next-generation Web Application Firewall (WAF) in the report The Forrester Tech Tide™: Zero Trust Threat Prevention, Q4 2022 published...
Blog
NSFOCUS Selected as a Representative Vendor in IDC Perspective: Unified Security Management as a Service (USMaaS), 2022
Santa Clara, Calif. January 19, 2023 – NSFOCUS, a global provider of intelligent hybrid security solutions, announced today that it has been selected by IDC as a representative vendor in the report IDC Perspective: Unified Security Management as a Service (USMaaS), 2022 released recently, and NSFOCUS T-ONE Cloud was selected...
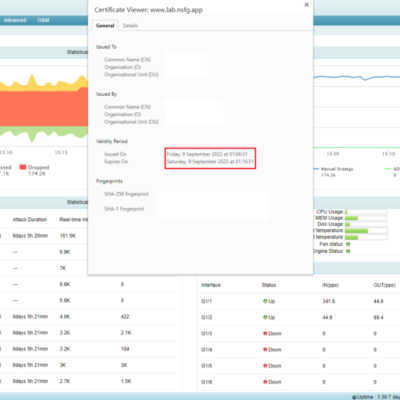
SSL Certificate Replacement on NSFOCUS ADS
A Secure Sockets Layer (SSL) certificate is digitally signed and issued by a trusted certificate authority (CA) to an organization for authentication of server identities and encryption of data in transit. Therefore, SSL certificates can protect user privacy and information security. For a website with an SSL certificate issued by...
NSFOCUS Cloud DDoS Protection Service Summary of 2022
NSFOCUS published the Summary of Cloud DDoS Protection 2022 recently. This summary comes from DDoS attacks protected by NSFOCUS Cloud DDoS Protection Service (Cloud DPS) in the year 2022. The following service highlights can be found in the report: DDoS attack timeline, volume and attack type distribution collected from NSFOCUS...
NSFOCUS Selected in Gartner’s Emerging Tech Impact Radar: Security
We are pleased to announce that NSFOCUS was selected by Gartner® as a sample vendor in the field of Deception as a Feature in the report Emerging Tech Impact Radar: Security (November 2022). According to the report, “This technology can significantly reduce the amount of time an attacker gets to...
Harbor Unauthorized Access Vulnerability (CVE-2022-46463) Alert
Overview Recently, NSFOCUS CERT detected that the technical details of the Harbor Unauthorized Access Vulnerability (CVE-2022-46463) were publicly disclosed on the Internet. Due to an access control flaw in Harbor, an attacker without authentication can access all information of public and private image repositories through this vulnerability and perform image...