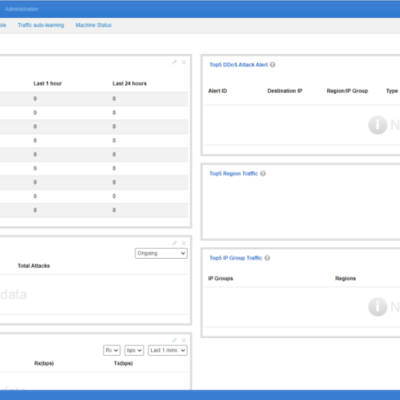
The Web API of NTA provides an interface for configuring regions or IP groups. Data can be obtained with a GET request and added, removed, or modified with a POST request, facilitating the query and configuration of NTA by O&M personnel. All API POST requests will be recorded in the...
Ano: 2022
Security Knowledge Graph | Drawing Knowledge Graph of Software Supply Chain and Strengthening Risk Analysis
The security knowledge graph, a knowledge graph specific to the security domain, is the key to realizing cognitive intelligence in cyber security, and it also lays an indispensable technological foundation for dealing with advanced, continuous and complex threats and risks in cyberspace. NSFOCUS published a series of articles about the...
Three Transformations of NSFOCUS ADS Solution
With the continuous transformation of telecommunication infrastructure in recent years, the popularization of 5G technology has promoted the sustainable and rapid growth of network bandwidth resources, and driven the rapid development of technologies such as big data, cloud computing, and the Internet of Things (IoT). However, due to security flaws,...
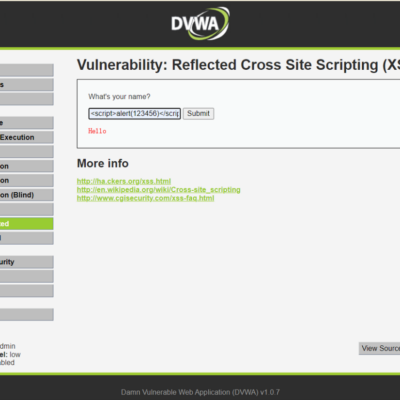
XSS Attack Protection
Cross-Site Scripting (XSS) attacks are a type of injection in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws...
APT Group Gamaredon Intensifies Cyber Offensive in Ukraine (Part 2)
Part 1: APT Group Gamaredon Intensifies Cyber Offensive in Ukraine (Part 1) Type 2: Send malicious HTML attachments by masquerading notification emails The second type of attack activity Gamaredon mainly carried out is spear phishing emails. This is a new attack process that emerged in the second quarter of this...
APT Group Gamaredon Intensifies Cyber Offensive in Ukraine (Part 1)
Overview Beginning in the second quarter of this year, NSFOCUS Security Labs discovered that the APT group Gamaredon began frequently using a number of different types of attacks to conduct cyberattacks against military and police targets in Ukraine’s Kherson, Donetsk and other regions. In this attack cycle, Gamaredon mainly used...