Overview
On April 1, the Guardicore Labs team uncovered a long-running attack campaign which aims to infect Windows machines running MS-SQL servers. At least since May 2018, the campaign uses password brute force to breach victim machines, deploys multiple backdoors, and executes numerous malicious modules, such as remote access tools (RATs). We dubbed the campaign Vollgar.
It is not uncommon for attackers to use password brute force to breach systems and then inject malware. However, according to the report, there are still 2000–3000 databases being attacked every day. Victims are distributed in different countries (including China, India, South Korea, Turkey, and the USA) and belong to various industry sectors (including healthcare, aviation, IT, telecommunications, and higher education).
Reference link:
https://www.guardicore.com/2020/04/vollgar-ms-sql-servers-under-attack/
Scope of Impact
- Windows machines running MS-SQL servers
Troubleshooting
detect_vollgar.ps1
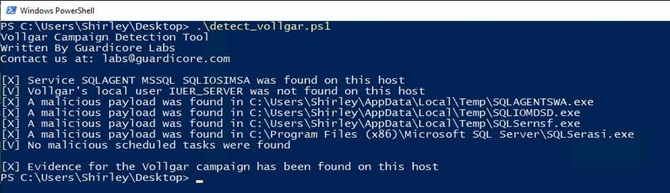
The Guardicore Labs team provides PowerShell script, detect_vollgar.ps1, for detecting local attack traces, including:
- Malicious payloads in the file system;
- Task name of the malicious process;
- User name of the backdoor.
The script is available in the following link:
https://github.com/guardicore/labs_campaigns/tree/master/Vollgar
Test procedure is as follows:
- Download detect_vollgar.ps1 to a local disk drive.
For details about the script, click the following link:
https://github.com/guardicore/labs_campaigns/blob/master/Vollgar/detect_vollgar.ps1.
- Press Window + R and then type in the PowerShell text box.
- Run the script.
If Evidence for Vollgar campaign has been found on this host is displayed in the returned content, it indicates that the current system is infected.
In the case of infection, please do as follows:
- Remove attack traces from the detection result.
- Terminate the malicious program.
Note: If the system prompts a message indicating that file ps1 cannot be loaded when PowerShell is directly executed, this is because script execution is disallowed in the system. For details, please see get-help about_signing. This message indicates that you are not allowed to execute the script.
You can run the following command to view the current execution policy:
get-executionpolicy |
Restricted indicates that no script can be executed.
You can run the following command to modify the policy:
set-executionpolicy remotesigned |
After successful modification, you can use PowerShell to execute the script.
To withdraw modification, you can run the following command to restore the setting.
set-executionpolicy Restricted |
Common Protection Suggestions
- Disable login to the database using a user name and password. Instead, log in to the database in Windows authentication mode and set the password strength in the Windows policy.
- Enhance network boundary intrusion prevention and management by configuring a firewall at the network ingress and egress to block unnecessary communication.
- Check the security of network devices, servers, operating systems, and application systems exposed on the Internet, including but not limited to vulnerability scanning, trojan detection, configuration scanning, web vulnerability detection, and website penetration test.
- Enhance security management by establishing a network security emergence handling mechanism, enable network and running log audit, arrange network attendance, and take detection measures, so as to detect and handle attack risks timely.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS Technologies Group Co., Ltd., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.