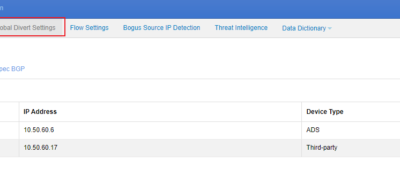
This document describes how to configure collaboration between ADS and NTA. NTA offers network monitoring and DDoS attack detection. If a DDoS attack is detected, NTA starts collaboration with ADS according to pre-defined rules to notify ADS. Then ADS starts the traffic diversion mechanism to divert suspicious traffic from the...
Tag: DDoS attack
Large-scale DDoS Attacks Target Many Critical Industries as Election Approaches in Brazil
1. Â Background As early as 2016, a report from BitSight, an American cybersecurity ratings company, showed that Brazil is one of the riskiest countries to do business in. According to the cyber threat report released by SonicWALL, Brazil suffered more than 33 million intrusion attempts in 2021, and suffered ransomware...
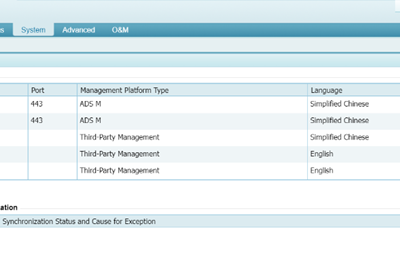
Introduction to Web APIs of ADS
O&M personnel can quickly and easily perform operations such as information query and diversion configuration through web APIs. If web APIs of ADS are to be used by the management platform, mutual authentication between the management platform and ADS must be performed first to ensure security. The procedure is as...
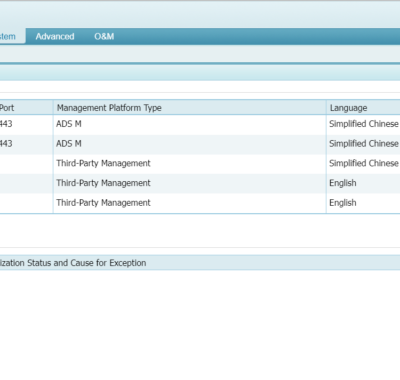
Configuring Collaboration Between ADS and ADS M
ADS M supports standalone management and cluster management. In standalone management mode, ADS M manages a single ADS in an in-path or out-of-path deployment. In cluster management mode, ADS M manages multiple ADSs as a cluster for automatic synchronization of device configuration and protocol synchronization among these ADSs. The following...
Cloud DPS – Optimization for a Managed Security Service Customer
Today DDoS attacks are continuing to increase in frequency, volume and duration to affect a business’s continuity and reputation. DDoS mitigation capability has become the top priority for CIO/CISOs in Enterprise, Internet content providers and government, while they may have to face the challenge of finding sufficient experienced security professionals...
Case Study: A 400G DDoS Attack Event Captured By NSFOCUS in Hong Kong S.A.R.
Event look back A NSFOCUS Cloud DPS customer with their servers located in Hong Kong SAR has encountered a series of mass DDoS attacks lasted for four (4) days, from June 20th to 24th. The attackers managed to create serval spikes including the biggest one reaching 399.2 Gbps and followed...