Beijing, China, September 18, 2024 – At the National Cybersecurity Awareness Week, the Cloud Security Alliance (CSA) Greater China Region unveiled the industry’s first-ever AI-empowered security map: AI Security Industry Map, 2024. This comprehensive map delineates four major categories and eighteen sub-categories, offering a clear depiction of the “AI+Security†ecosystem...
Tag: AISecOps
NSFOCUS Recognized as a Leading Innovator in AI-driven Cybersecurity Solutions at WAIC 2024
SANTA CLARA, Calif., July 12, 2024 — NSFOCUS is honored to announce that its Large Model Empowered Security Operations case has been featured in the 2024 Case Studies of Demonstration Application for Foundation Models at the World Artificial Intelligence Conference (WAIC). This prestigious recognition highlights NSFOCUS’s pioneering efforts in AI-driven...
AISecOps Development Trend
As an old saying goes, "Rome was not built in a day", it is impossible to build AISecOps capabilities simply by following the example of other businesses. In fact, the most topical and mature AI technology is widely applied, but needs to be delved a little deeper. For instance, typical...
AISecOps Development Trend
As an old saying goes, "Rome was not built in a day", it is impossible to build AISecOps capabilities simply by following the example of other businesses. In fact, the most topical and mature AI technology is widely applied, but needs to be delved a little deeper. For instance, typical...
AISecOps Technology and System
Core Connotations Literally, AISecOps is composed of three core technologies, i.e. AIOps, AISec, and SecOps. AISec-enabled technology fusion brings new expectations to the industry. Both AI security and AI-based security applications have become hot topics in academia and industry. AI has been successfully applied in multiple single-point security technologies and...
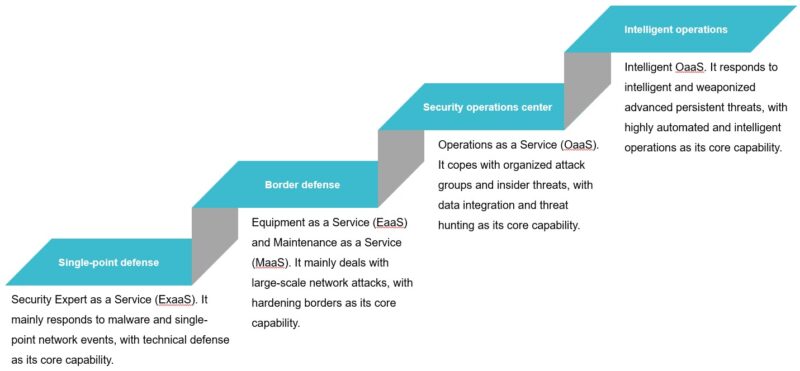
SecOps Development: Brief History, Outlook and Challenges
With the boom of the global digital economy, cybersecurity is converging with the Internet of Things (IoT), industrial Internet, cloud computing, and 5G, bringing about disruptive changes to security in various aspects, including traditional physical security, biological security, public security, and national security. Meanwhile, the attack surface keeps expanding in...