As an old saying goes, “Rome was not built in a day”, it is impossible to build AISecOps capabilities simply by following the example of other businesses. In fact, the most topical and mature AI technology is widely applied, but needs to be delved a little deeper. For instance, typical intelligence services like intelligence speech and image recognition only implements low-level perception. In security, economic, and political scenarios and life-critical technical scenarios like military, finance, healthcare, self-driving, and legal rulings, the current AI techniques can achieve partial automation for critical task decision-making, but remained far from achieving full automation. Cybersecurity operation is among the scenarios. Essentially, the reason why AI techniques fail to penetrate deeply in various sectors is because these techniques are not mature enough to win people’s trust. In view of this, in this chapter, we look ahead of the development of intelligent security operations techniques by explaining how to build a trustworthy intelligent security system and an AISecOps technique ecosystem.
Building a Trustworthy Intelligent Security Technology System
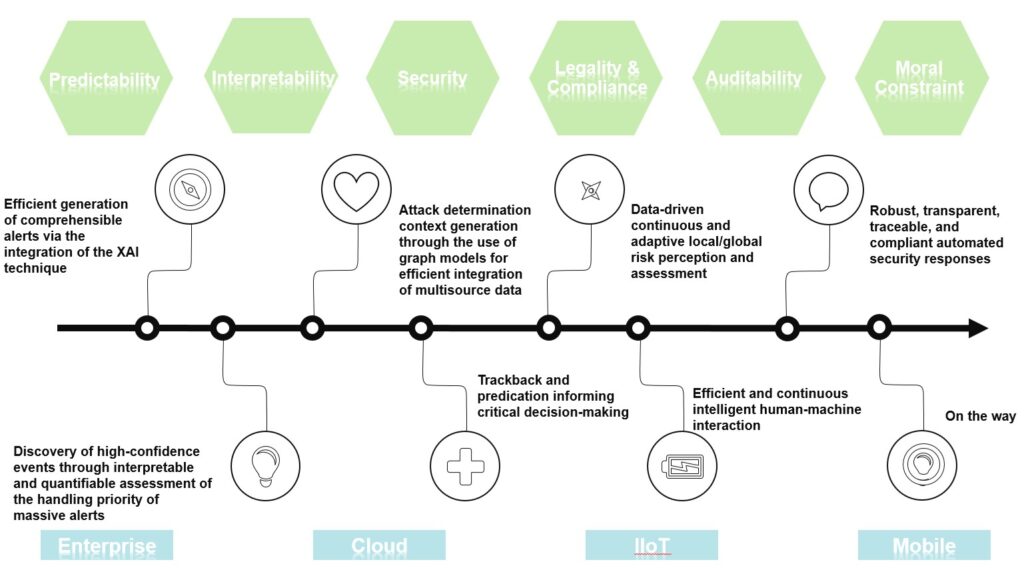
Anyway, building a trustworthy AI system to make up people’s inherent defects in handling massive data is the ultimate pursuit of practitioners. AI techniques that empower cybersecurity can be directly used in non-core scenarios and processes of cybersecurity data analysis to contribute to security assurance. For instance, use the natural language processing technique to analyze threat intelligence, build a conversational bot powered by the expert system, or use a mature image processing technique to detect malicious images and videos. Moreover, it is essential to sharpen AI technologies to apply them in core security phases like threat detection, assessment, association, and response. As shown in the preceding figure, from the perspective of building technical trust, to increase the automation of critical security capabilities, trustworthy intelligent security must meet the requirements of the following core technological elements: 1. Predictability: able to be adapted to highly dynamic network environments and attack scenarios. 2. Model algorithm: features transparency, interpretability, security robustness, and privacy protection. 3. Intelligent technique: ensuring legitimate, compliant, and auditable technique applications and application results; consistent with the code of ethics when applied for decision-making. These technological elements complement and depend on each other, and consideration should be given to them at the early design stage. Just as we prefer to work with those people that have good character, excellent communication skills, are able to work efficiently under great pressure, and observe laws, we can build trust in AI only if it has the same good traits to be competent to accomplish security operations tasks in a highly automated way.
While seeking to build a trustworthy intelligent security system, we need to fully integrate explainable artificial intelligence (XAI), privacy protection technology, graph mining and analysis, intelligent decision-making system, risk assessment, and human-machine interaction among other multidisciplinary and multifield intelligent technical capabilities so as to empower tasks at perception, cognition, decision-making, and action stages of the security operations process.
Building an AISecOps Technique Ecosystem
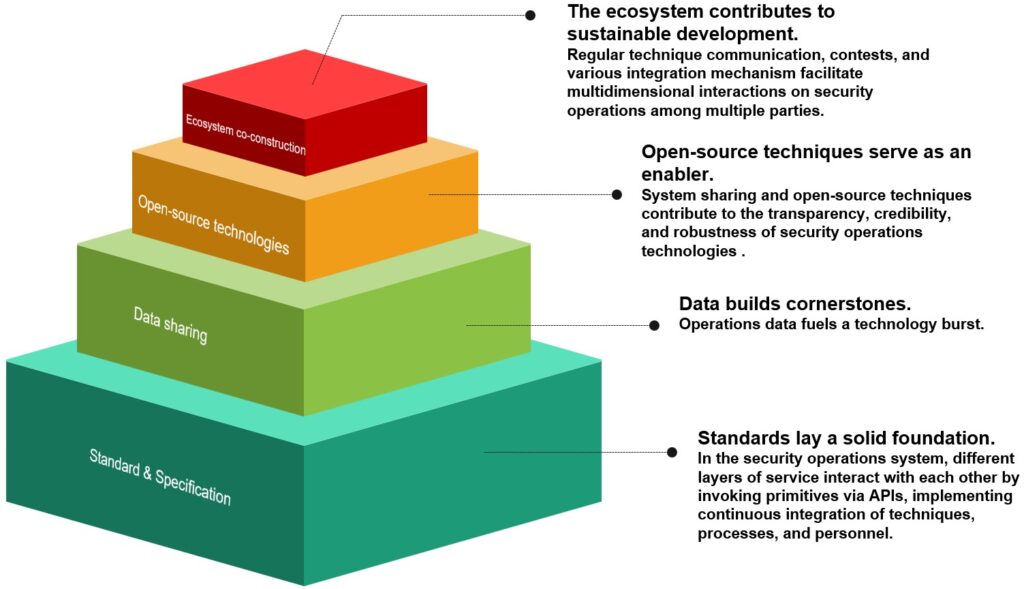
Therefore, it is urgent to build an AISecOps technique ecosystem, no matter whether to satisfy actual needs or better adapt to technique development. As shown in the preceding figure, the AISecOps technique ecosystem consist of four levels: standard & specification, data sharing, open-source technologies, and ecosystem co-construction. By establishing industrial and national standards, we can develop uniform and normative critical security operations process and technical interface to ensure a clear division of labor. Through data sharing, we should set up a test arena for security operations technologies to encourage competition and contests of technical capabilities. Making techniques open source, we should build a thriving technical community to attract and cultivate more security operations talents. Finally, we should set up a communication platform and mechanism to facilitate communication and cooperation, ensuring regular technical exchanges in all aspects.
Cybersecurity technologies have entered a new stage of development that centers on adaptative control and operations of security risks throughout the lifecycle. Given the influx and integration of massive, multisource, and high-dimensional operations data, it is vital to build a trustworthy and operable AISecOps system in a new era of digital infrastructure to advance towards a highly intelligent and automated cybersecurity defense system and greatly facilitate security operations.
Related posts:
