“Pay or Die†is an opening phrase often used by DDoS blackmailers. Github was attacked, NZX was unable to provide services for 4 days… these are all serious DDoS blackmail incidents this year. This is just the tip of the iceberg of such lucrative crimes. In various forms of digital black mailings, using “distributed denial of service attacks” (DDoS) to attack target companies has become attackers’ first choice.
The blackmailer generally takes one or two steps: 1. Conduct the attack for a period of time and then stop; 2. Ask for a ransom. Some blackmailers skip the first step and ask for money directly. Victims face two choices, either pay the money or be continuously attacked by DDoS. DDoS attacks are very harmful and difficult to prevent. They can directly cause the downtime, server paralysis, damage to authority and brand image, loss of property, and other huge losses, which seriously threaten the development of Internet information security.
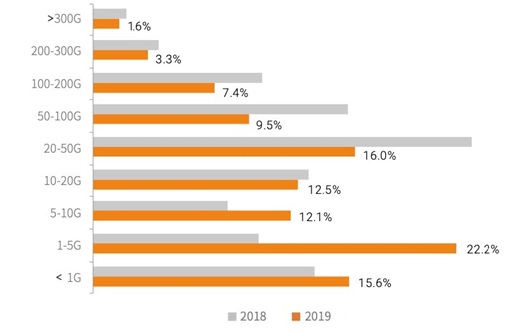
Base on the annual DDoS research conducted by NSFOCUS, the bandwidth of DDoS attacks is increasing every year and has become a major threat to enterprises and internet service providers (ISPs). In terms of the total traffic of DDoS attacks, the total traffic in 2019 decreased by 26.4% compared to that in 2018, which shows that the overall attackers’ willingness to attack has not increased with the maturity of technology.
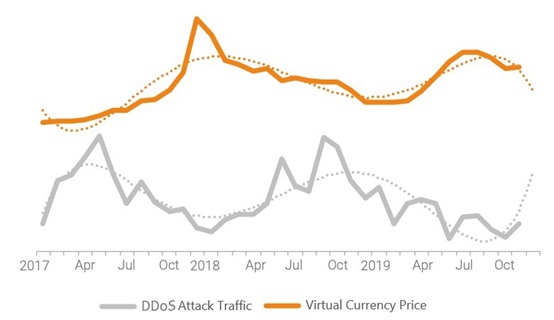
The uprising of the Bitcoin market and the functional migration of botnets may be the main reasons. Botnets are no longer limited to a single DDoS or remote-control function, but enjoying more choices like cooperating with ransomware and mining Trojans, or turning to distributed blasting attacks. The richness of functions and the flexibility of switching enable attackers to closely follow market trends and maximize their own profits.
In recent years, DDoS attacks have spread to all industries. From e-commerce to gaming sites, from competitors to partners, any enterprise or organization with online business may become the target, especially those that lack security protection.
On the other hand, the participation of IoT devices in DDoS attacks has increased year by year. The number of IoT attack resources participating in DDoS attacks throughout the year is nearly 170,000. Among the DDoS groups we have found, a single group contains up to 28,000 IoT attack resources, accounting for a high percentage of 31%. The large number of IoT devices, long online time, and long vulnerability update cycles have nurtured attackers to exploit vulnerabilities. We need to further strengthen the perception, prevention and governance of the attack.
At the same time, judging from the number of attacks in each month in 2019, the number of DDoS attacks was generally stable and the attack traffic tended to decrease in the second half of the year. We believe that the overall trend of DDoS attacks is related to the rebound in the price of virtual currencies. We pointed out in the “2017 DDoS and Web Application Attack Situation Report”1 that with the appreciation of virtual currencies, attackers have begun to shift the “high-quality” Botnet resources they possess from DDoS activities with higher criminal costs mining activities with lower costs but higher profits. In 2019, as the price of virtual currencies rebounded and the cost-effectiveness of mining increased, the tendency of attackers to choose DDoS attacks to make profits has weakened, which was particularly evident in the data in the second half of the year.
Comparing the Bitcoin price in each month with the total DDoS traffic trend, the Pearson correlation coefficient is -0.53, showing a certain negative correlation, which further confirms our view.
Initially, this type of DDoS ransomware attack only targeted Bitcoin transactions and operations. But now the goal has been extended to banks and other companies, depending on whether their websites can be used for online transactions. No matter what, DDoS attacks have disrupted the operations of some companies and caused huge economic losses and damage to many companies. Most companies do not have the ability to provide comprehensive and effective DDoS attack protection for their servers. Therefore, the use of network cloud defense that specializes in DDoS mitigation is the most ideal prevention method.
What should the customer do?
In order to assist customers in effectively mitigating DDoS attacks, NSFOCUS has not only launched ADS product suitable for single point protection, but in order to adapt to the international market, has also launched a service product specifically designed to solve DDoS attacks on the international Internet, NSFOCUS Cloud DPS (DDoS Protection Service).
When a customer encounters a large DDoS attack that exceeds its own export bandwidth, after adopting the Cloud DPS cleaning service, the attack traffic will be led to the NSFOCUS Cloud Scrubbing Center for cleaning.
The traffic scale after coarse-grained cleaning will be greatly reduced. It causes congestion on customer links and directly solves the problem of DDoS attacks in the cloud. After cleaning, clean business traffic is transferred back to the customer, so that customer will not be aware of being attacked when DDoS attacks come.
The Cloud DPS scrubbing service is targeted at cloud scrubbing for large traffic. It not only solves the problem of large traffic attacks for small-scale customers, but can also serve as a backup service for local scrubbing for some companies that have DDoS equipment locally. It is a key means to deal with large traffic attacks, helping customers break through the limitations of local scrubbing solutions and defend large-traffic DDoS attacks with minimal cost. Cloud DPS scrubbing service and local ADS also form a three-dimensional anti-DDoS system. This complete solution helps customers effectively mitigate current DDoS attacks through a hybrid method of cloud and local scrubbing, which solves the difficulty of the congestion in exporting bandwidth. It reduces the huge consumption of bandwidth expansion and the construction investment on large-capacity scrubbing nodes. The local scrubbing equipment ADS effectively responds to small and medium-scale traffic attacks (mainly application layer attacks, accounting for more than 80% of the attacks, and can be supplemented by MSS services, so that customers do not need to worry about security operation and maintenance). When encountering a large-traffic attack, use NSFOCUS Cloud DPS with the NSFOCUS Traffic Scrubbing Center to perform the scrubbing. (Simple attacks are the main type, accounting for less than 20% of the number of attacks encountered, and large bandwidth resources provide real-time effective response to large traffic attacks).
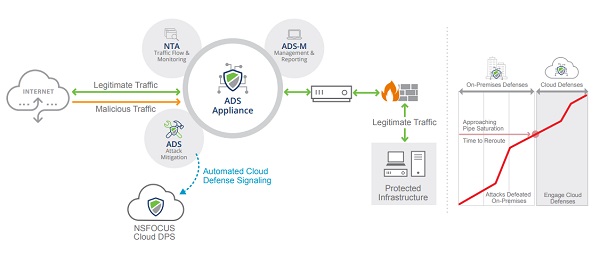
NSFOCUS has deployed multiple high-level defense centers based on the distribution of customers in the international market, and then opened the links between centers according to the changes and transfers of customer network traffic, and finally formed the protection system that can conduct multi-site cooperation and local scrubbing. It can effectively deal with large-traffic and mixed attacks at the application layer, allowing customers to relax no matter encountering what kind of DDoS attacks. When customers encounter small traffic attacks on complex application layer or pulse attacks, they can directly perform the scrubbing through the local ADS. When encountering a large-traffic attack, the Cloud DPS service is linked with a fast effective speed. Through the coarse-grained filtering of the cloud scrubbing service, most of the attack traffic is cleaned, and the remaining is filtered through the fine-grained defense algorithm of ADS. No matter how complex a combined DDoS attack is, it will fail.