Abstract
The real economy with manufacturing as the core industry is the basis for maintaining national competitiveness and healthy economic development. Based on the universal recognition of this concept, the Industry 4.0 strategy of Germany, the national advanced manufacturing strategy of the United States, and the national manufacturing policy of India, have taken place as national strategic plans.
In the above context, the cyber risks faced by global manufacturing companies are also increasing. The old “island operation” no longer exists, the boundary between IT and OT has disappeared, and the application of new technologies has gradually blurred the boundary of the network. The deployment of a large number of industrial Internet of Things equipment, while increasing system functions and improving production efficiency, has also brought many loopholes, which has gradually expanded the exposed attacks. At the same time, along with the ravages of ransomware, major manufacturers have also suffered different degrees of losses.
In June 2020, Honda was attacked by Snake ransomware and forced to shut down automobile factories in the United States and Turkey, as well as motorcycle production plants in India and South America.
This article summarizes the common types of attacks against the manufacturing industry, and gives suggestions for protection.

Phishing attacks
Phishing attacks remain as the most popular network attack tool. In order to carry out more harmful attacks or actions, it is usually necessary to open the “gate” to the target enterprise, and phishing emails are generally deployed. For example, in 2016, an employee of the global solar panel manufacturer received an e-mail claiming to be the CEO.
The e-mail mentioned that the detailed information of the company’s internal employees was required. The employee sent the details without checking the authenticity. The information was sent to the CEO, but the CEO was a cybercriminal, and the employee became a victim of a phishing attack, which leaked company’s confidential information. Perhaps the subsequent criminals will conduct even more crazy penetrations and attacks.
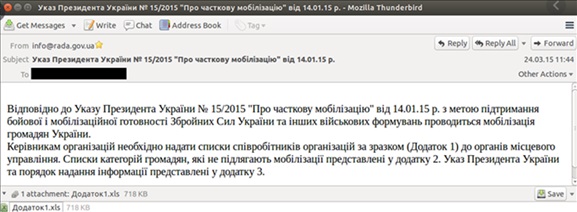
A phishing attack similar to this also appeared in the Ukraine power outage in 2015. Hackers released BlackEnergy 3 malware through phishing emails and successfully obtained access to the company’s industrial control network in subsequent attacks. One after the other, the circuit breaker is activated to cut off the power, and KillDisk malware is enabled to delete important log files and master boot records, so that the employees cannot quickly restore power and perform analysis.
At the same time, hackers also carried out DDoS attacks on the telephone network, making it difficult for employees to communicate with customers, understand the situation and restart power. The phishing emails are as follows:
Common characteristics of phishing attacks:
- Mail with malicious attachments;
- With hyperlinks that are different from known websites and misspelled;
- Eye-catching title or content;
- Unusual email sender;
- Urgent orders or to-do items.
Supply chain attacks
For the manufacturing industry, not one manufacturer can complete the whole production. It must rely on the parts and components of different manufacturers to complete the production and assembly of the entire product. Therefore, in the manufacturing process, multiple partners should collaborate to achieve efficient operation. In this process, the risk of supply chain attacks is introduced.
Supply chain attacks are an attack method used by many criminals, through which the sensitive data and intellectual property rights of manufacturers can be stolen. If a malicious attacker obtains the partner’s permission to access the manufacturer’s network, criminals can enter the manufacturer’s network, steal sensitive information or data, and even core process manufacturing documents, which will cause major harm to the company.
In addition, the external software or hardware used by manufacturers has security risks, and there is also a possibility of being attacked in the equipment and system supply chain. Most product development uses public open source or closed source components, but these components have, more or less, security vulnerabilities.
Embedding defective components into products may cause more security problems, such as Ripple20 vulnerabilities exposed in June 2020, Ripple20 vulnerabilities exist in the TCP/IP protocol stack developed by Treck. In the past 20 years, the protocol stack has been widely used and integrated into countless enterprise and individual consumer devices. This series of vulnerabilities will affect hundreds of millions of Internet of Things (IoT) and industrial control devices worldwide.
Ransomware attack
Ransomware is a type of malicious software that infects computer servers, desktops, laptops, tablets, and smartphones. It penetrates through various mechanisms and often spreads laterally from one machine to another. Once infecting the system, the virus will secretly encrypt data, video, text and other files, and then demand a ransom from the user. Extortion can range from hundreds to thousands of dollars (usually in the form of cryptocurrencies such as Bitcoin) by online payments, and then exchange them for the decryption keys needed to restore the user’s locked files. Extortion requirements usually include a series of payment deadlines, each missed deadline will increase the ransom amount and may lead to the destruction of some documents. If the victim does not pay, the attacker will discard the decryption key, thus permanently losing access to the data.
The WannaCry outbreak in 2017 and the attack on a car manufacturer is a notorious example of ransomware attack. The virus has infected more than 200,000 computers in more than 150 countries. Renault of France and its alliance partner Nissan were forced to temporarily suspend some factories in Europe because many of its systems were paralyzed by attacks. Facilities in France, Slovenia, and Romania were hit hard, and Renault was forced to temporarily shut down industrial production lines.
Manufacturers face heavy losses after being attacked by this kind of ransomware. On the one hand, the encrypted files are usually manufacturing production or other important data files. If such files are missing, the production line will be forced to shut down with various pressures from the partners and their economic losses; on the other hand, the infected files cannot be recovered after an attack. The time and workload of replacing new office equipment through virus detection or security protection are unacceptable to manufacturers. Therefore, manufacturers sometimes have to pay a ransom in hopes of quickly resuming production and getting on the right track. The lost working hours and production tasks during this period are a huge economic loss. Therefore, this type of attack is currently the most feared by manufacturers.
IoT attacks
With the deepening of the intelligent transformation of the manufacturing industry, the role of the Internet of Things in promoting this process is becoming more and more important. With a variety of IoT devices, manufacturers can optimize their production processes more effectively and accurately. For example, companies are using IoT sensors placed in devices to track assets, collect data, and perform analysis. These sensors monitor various operating parameters and key data of the equipment to achieve automatic recovery and reduce maintenance downtime.
With the increase of various types of IoT devices in manufacturing plants, more security risks are taking place. IoT devices have networking attributes and are easily exposed to the network environment. Manufacturers’ IoT, industrial control networks, and office networks are usually not effectively isolated. They can penetrate into the industrial control network through public vulnerabilities or 0Day of IoT devices, and carry out malicious attacks on key production equipment, affecting production and causing incidents such as processing accidents.
One example of the industrial control security incidents with detailed reports of IoT device attacks is as follows. On August 5, 2008, an explosion occurred on a transnational oil pipeline in Turkey, destroying the oil transportation pipeline and interrupting the oil transportation. A detector and a camera were installed in this pipeline but no alarm signal was received, and the camera failed to capture the scene of the explosion. After investigation, it was found that the cause of the accident was the surveillance camera itself.
Hackers used the webcam software loopholes to break into the internal system, and installed a malicious program on a computer responsible for alarm management, and then infiltrated the pipeline operation control system to increase the pressure in the pipeline without triggering the alarm. The high pressure in the oil pipeline caused the explosion, and the hacker deleted 60 hours of surveillance video to destroy the evidence without leaving any clue. Although the incident occurred in the oil and gas industry, hackers’ attack methods and technologies can often be copied to other industries. Manufacturing companies targeted by hackers are most likely to experience increased product failure rates, damage to key processing equipment, and employee casualties.
Complex industrial equipment attack
The core assets of manufacturers are different from other industries. In addition to common PLC, HMI and other equipment, there are also unique CNC machine tools, industrial robots, optical measurement systems, etc. These assets usually have complex systems and programming environments. For example, an industrial robot is composed of control systems, drive systems, and execution joints.
It executes corresponding manufacturing tasks according to task programs. These task programs are parsed in the control system and decomposed into multiple execution steps (for example, ” Move to the right”, “open the pliers”, “move down”, “pick up”) to complete the corresponding production process of the product. Each machine supplier has its own special language to write task programs, such as ABB’s Rapid, Comau’s PDL2, Fanuc’s Karel, Kawasaki’s AS, Kuka Robot Language (KRL), Mitsubishi’s Melfa Basic, and Yaskawa’s Inform. These industrial robot programming languages (IRPLs) are proprietary, and each language has a unique set of features.
IRPLs is very powerful because it allows programmers to write automated programs, read and copy data from the network or files, access process memory, execute code dynamically downloaded from the network, and so on. If used improperly and without safety awareness, powerful programming functions can be very dangerous.
For example, a worm program can be written to propagate itself among robots on the network. After infecting a new robot, the worm will start scanning the network for other potential targets and use the network to spread. The worm program includes a file collection function to obtain sensitive data and files from the infected robot. The following figure shows an example of a network scan for worm malware:
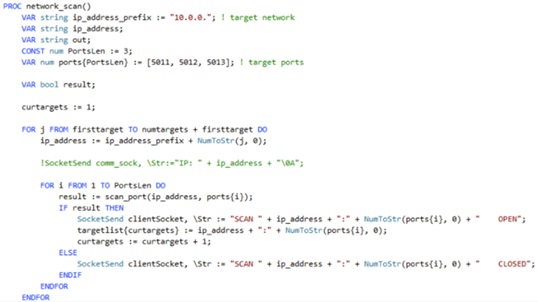
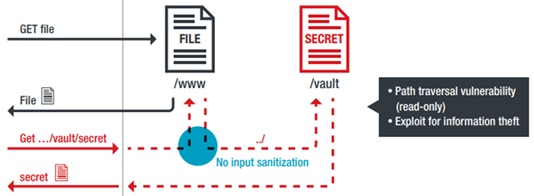
In addition, there are many vulnerabilities in industrial robots, such as directory traversal which enables attackers to steal log files that record the movement of the target robot.
The log files contain sensitive information such as intellectual property rights (such as product construction methods). Then, the attacker can access other files in other directories (including files with authentication secrets) and use these files to finally access the control system. The following figure shows a connection to access confidential files without verification confirmation.
The above are only examples of industrial robot systems to illustrate the possibility of attacks on complex industrial equipment in the manufacturing industry. Other key equipment such as CNC machine tools and laser measurement systems may have loopholes or normal functions used maliciously due to their powerful functions and complexity.
Protection advice
The above analysis focuses on the most common types of attacks in the manufacturing industry, and manufacturers need to take protective measures in advance to deal with possible attacks. Here are some suggestions:
- Strengthen the safety awareness of employees, organize relevant trainings to teach employees how to recognize phishing and how to prevent them, and conduct phishing tests from time to time.
- Introduce the security assessment and management mechanism of the equipment supply chain. For various operating machines, IOT devices, and mobile devices that are used daily in the factory, before purchasing or using them, they should evaluate the security by themselves or find professional security vendors, try to build a vulnerability repair mechanism with suppliers, and set product security access thresholds.
- Compliance management and control of upstream and downstream vendors in cooperation, establishing different authority levels from multiple dimensions such as business, data, and documents, and making detailed records for external network access for traceability and inquiries.
- Actively analyze existing assets, carry out zoning and domain division based on indicators such as importance level, deploy network-wide security management products, and form an in-depth defense system with rapid response capabilities. Excellent security management products can detect the source of virus infection in time and conduct isolation treatment by monitoring network traffic, effectively blocking the spread of the virus. After the domain is divided, it can also avoid the spread of ransomware in the whole factory.
- Establish a strict and effective data backup plan, save key business data and files locally, remotely, and in private clouds, to avoid production shutdown due to ransomware infection of key files.
- Strengthen endpoint security protection capabilities such as hosts. Consider deploying appropriate terminal security management software. For machines that do not meet the deployment conditions, install system patches as much as possible on the basis of compatibility testing; if there is no need to use sensitive ports such as 3389 and 445, close them as much as possible.
- Perform regular security checks on IOT devices, contact the manufacturer to obtain the latest version of the firmware for real-time updates, to prevent attackers from launching attacks using known vulnerabilities.
- Manage wireless connections in the manufacturing plant area, change passwords regularly (using strong passwords), manage private access to APs, and turn off wireless functions of unnecessary printers and other devices.
- When external personnel access the network in the manufacturing plant, use VPN or other encrypted connection schemes, and record their behavior.
- Perform security scanning processing on the program files of CNC machine tools, industrial robots and other equipment to ensure that the program files do not carry known viruses.
- If possible, automatic or regular source code review of the programs of CNC machine tools, industrial robots and other equipment is required. If abnormal functions are found, timely feedback to the programmer for modification, filing, recording, sharing experience, etc.
- Establish a program file security review library shared with integrators, and establish an access and identity verification mechanism. Only certified programmers have the authority to read and store programming programs.