Incident discovered
In early 2021, a private cloud service provider in the United States was hit by a massive hybrid SYN Flood attack.
As the service provider is a customer of NSFOCUS Cloud DDoS Protection Service and subscribed with Managed Security Service (MSS), the malicious traffic is noticed instantly by NSFOCUS Managed Security Service team, followed by expert intervention immediately triggered within 10 minutes and further analysis and countermeasures applied quickly.
Attack vector analysis
Step 1
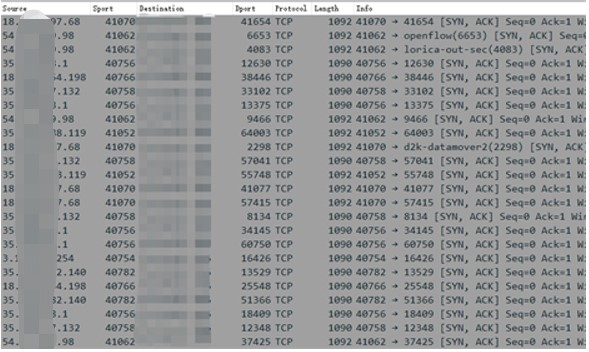
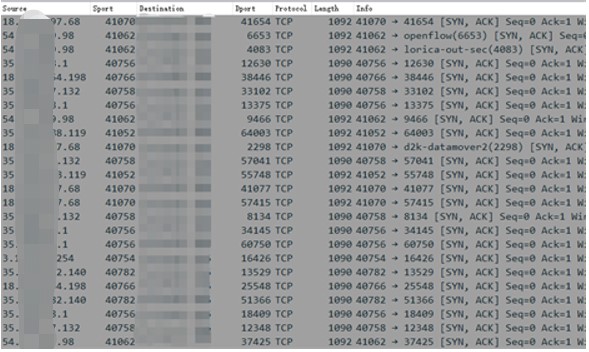
We first found that the attacker is sending a large number of SYN/ACK packets, and the packet length is ranging from 1090 or 1092 bytes.
Step 2
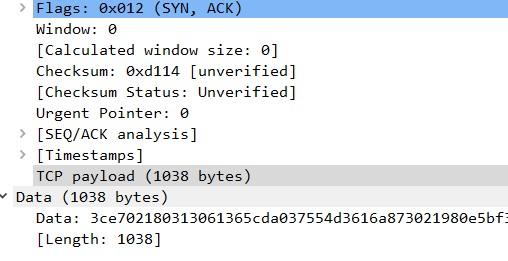
The legitimate payload of most SYN/ACK packets is filled with Data. However, for legitimate SYN/ACK, the payload should be TCP Options (e.g.: MSS, SACK, NOP) and its length is usually around 100. In other legitimate cases, SYN/ACK should not have any payload.
Step 3
The packet is a mixture of SYN and SYN/ACK, and sent from the same port, which is unusual.
Step 4
In a typical TCP reflection attack, the TTL of the SYN and SYN/ACK packets shall be different.
In this case, the TTL is the same so we could exclude the possibility of TCP reflection and it is reasonable that the attack packet is generated by an attack tool.
Step 5
Finally, we also checked the source IP of the attack through the NSFOCUS Threat Intelligence, and find that the source IP address is owned by Amazon AWS, marked as a medium threat.
Solution
NSFOCUS Managed Security Service team applied accurate SYN/ACK protection algorithm on NSFOCUS Anti-DDoS System (ADS).
Automated pattern matching rules are also applied on the ADS to make it match and drop the packet with TCP flags ‘SYN’ and ‘ACK’ and packet lengths at 1090 and 1902.
Result
Legitimate traffic is effectively dropped and no false-positive are observed. Our customer is happy that normal services are not affected during the incident.