Background
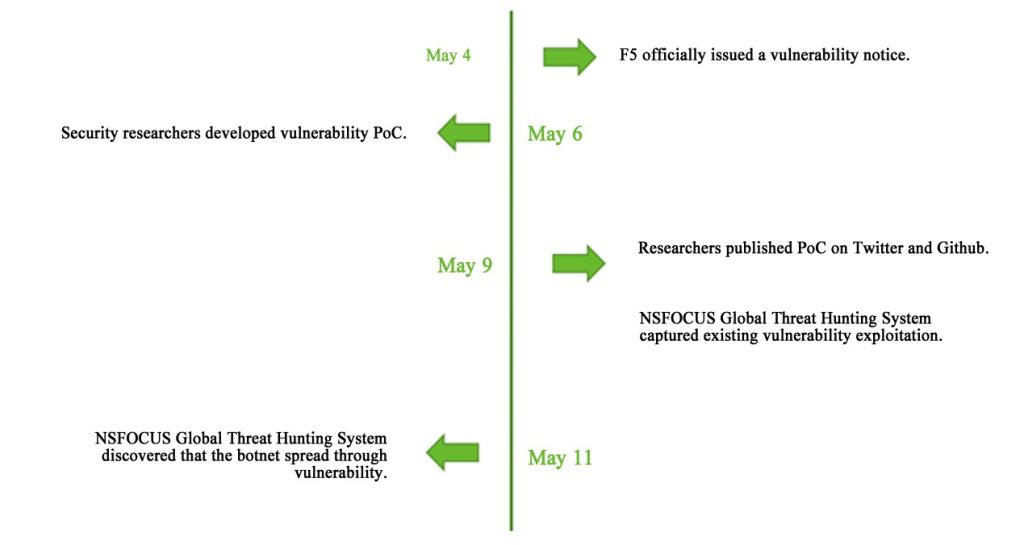
On May 4, 2022, F5 issued a security bulletin regarding a remote code execution vulnerability in iControlREST component of BIG-IP products. The CVE number of the vulnerability is CVE-2022-1388. The vulnerability can bypass authentication and remotely execute arbitrary code with a vulnerability score of CVSS up to 9.8. Since the bulletin, attackers have sought out unfixed systems to exploit the vulnerability on a large scale.
NSFOCUS Global Threat Hunting System monitored the spread of the vulnerability, and found that Yeskit botnet exploited the vulnerability to attack F5 BIG-IP devices. The C2 address used by the attacker was myjiaduobao.xyz.
Vulnerability Information
F5 BIG-IP is an application delivery platform of F5 Company, which integrates network traffic management, application security management, load balancing and other functions.
There exists access control error vulnerability in F5 BIG-IP, which allows unauthenticated attackers to access the BIG-IP system through the management port or their own IP addresses to execute arbitrary system commands, create or delete files, and disable services on BIG-IP.
The vulnerability score of CVSS is as high as 9.8, and the hazard level is serious. The affected versions are as follows:
- 16.1.0 – 16.1.2
- 15.1.0 – 15.1.5
- 14.1.0 – 14.1.4
- 13.1.0 – 13.1.4
- 12.1.0 – 12.1.6
- 11.6.1 – 11.6.5
Global Threat Hunting System monitoring shows that 60,000 of the 1.2 million F5 BIG-IP devices worldwide were affected, while in China, the number amounted to 10,000.
Vulnerability Exploitation
Vulnerability Monitoring
Global Threat Hunting System of NSFOCUS Fuying Lab first detected the F5 BIG-IP vulnerability (CVE-2022-1388) exploitation with the attack source IP address of 88.xxx.xxx.164 at 19:12:27 on May 9.

Vulnerability Exploitation Trend
According to the system monitoring, after F5 BIG-IP vulnerability was first detected on May 9, the number of vulnerability exploitation showed an obvious upward trend in the following two days.
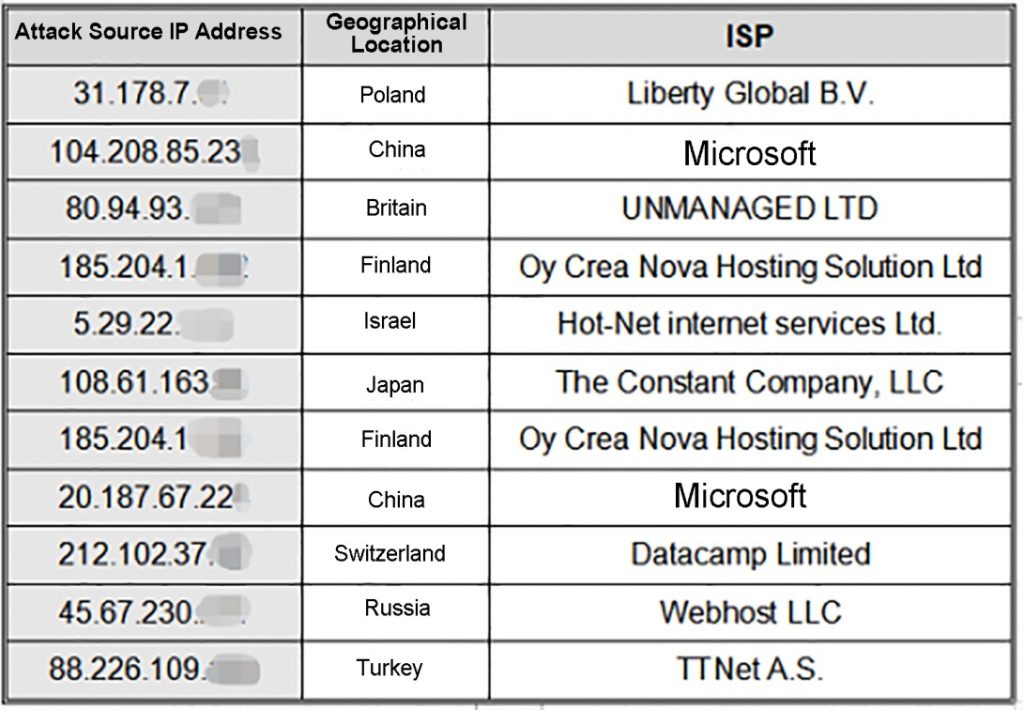
Attack Source Distribution
According to the system monitoring, some attack source IP addresses are as follows:
Execution Command Distribution
According to the system monitoring, the TOP10 execution commands of existing vulnerability exploitation are as follows:
| Serial Number | Vulnerability Exploitation Command |
|---|---|
| 1 | Id |
| 2 | rm -rf |
| 3 | curl |
| 4 | None |
| 5 | wget |
| 6 | cat |
| 7 | ping |
| 8 | pwd |
| 9 | ls -la |
| 10 | uname |
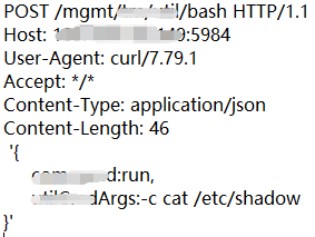
Vulnerability verification stage: From May 9 to 10, attackers executed harmless commands such as ID or cat /etc/shadow after exploiting the vulnerability, indicating that most of the attackers were currently in the early verification stage. The attack payload is as follows.
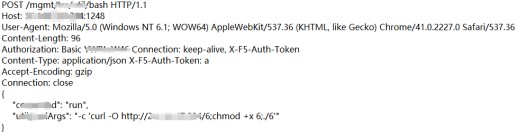
Vulnerability attack stage: On May 11, the system detected malicious code spreading, indicating that the attackers successfully exploited the vulnerability and were in the attack stage of download and execution. The attack payload is as follows:
Analysis of Yeskit Botnet Family
At 22: 49: 14 on May 11, NSFOCUS Global Threat Hunting System detected that Yeskit, a new botnet family, began to spread through the unauthorized RCE vulnerability of F5 BIG-IP. The attack source IP address was 20.xxx.xxx.224, and the attack payload is shown in the above figure.
The botnet family sample captured this time was written in go language, and the attacker adopted version go 1.18, which adjusted the format of go function name storage, so most tools cannot restore the function name of the sample normally, which can be seen as a new countermeasure.
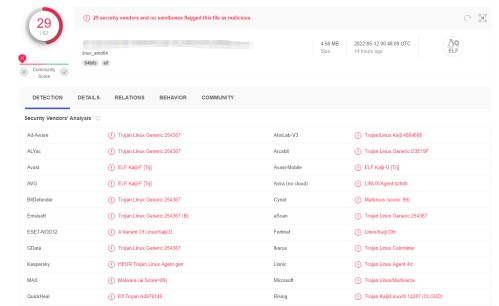
The attacker compressed the sample file through UPX shell to facilitate transmission. However, detection cannot be evaded. The current detection results are shown in the figure below:
After analysis and confirmation, some codes in this sample refer to MEDIOCRE BOTNET (aka kaiji) discovered by Fuying Lab, and most manufacturers also identify it as the family. As the MEDIOCRE family code is not open source, we assume that Yeskit and the MEDIOCRE family are developed and operated by the same group. For MEDIOCRE BOTNET, please refer to our previous analysis report: http://blog.nsfocus.net/mediocre-botnet-ssh
The C2 address used by the attacker is myjiaduobao.xyz, while the C2 address used by MEDIOCRE Botnet is luoyefeihua.site, which are quite similar to each other, but the naming style of the code in this sample is completely different from that of MEDIOCRE. MEDIOCRE normally names functions in pinyin:
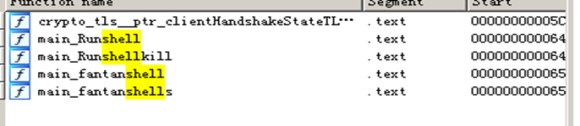
However, the sample is named in English:
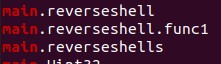
Although both adopt AES to encrypt their data, the monitored sample is inconsistent with MEDIOCRE in behavior.
The functions of the malicious sample detected this time are as follows:
- Anti-debugging function;
- It can be copied to the root directory, renamed it .img, and changed to a hidden file, which is difficult to find through the ls command.
- Persistent resident means is added, and “*/1 * * * * root /.img .†command is added in /etc/crontab.
- Perfection of DDoS function code;
- The function of remote control is added, such as command execution and file acquisition.
Therefore, the malicious file monitored this time is a new botnet family, which we named Yeskit.
Vulnerability Protection
With reference to influence scope of the vulnerability, F5 has officially provided a solution, which can be upgraded to an unaffected version or refer to official website documents: https://support.f5.com/csp/article/K23605346
