2.2 ICS-Targeting Malware Analysis
In recent years, more and more malware took ICSs as targets, causing an increasingly great damage.
The following sections analyze major ICS-targeting malware.
2.2.1 Electric Energy Malware Industroyer
- Overview of the Industroyer incident:
On June 8, 2017, the security company ESET discovered the ICS-targeting malware Win32/Industroyer. Dragos verified analysis results of ESET and released the hash information and analysis report of Win32/Industroyer on June 12. Those behind Industroyer have a deep knowledge and understanding of ICSs, especially industrial control protocols used in electric power systems. Support for four different industrial control protocols, specified in the standards listed below, has been implemented by the malware authors:
- IEC 60870-5-101 (aka IEC 101)
- IEC 60870-5-104 (aka IEC 104)
- Â IEC 61850
- OLE for Process Control Data Access (OPC DA)
Compared with the malware causing power outage in Ukraine in 2015, Industroyer has a more advanced functional structure and can cause the system to crash, making it deny service to legitimate users. Dragos’s analysis and speculation show that Industroyer may be related to Ukraine’s power outage incident that occurred in December 2016.
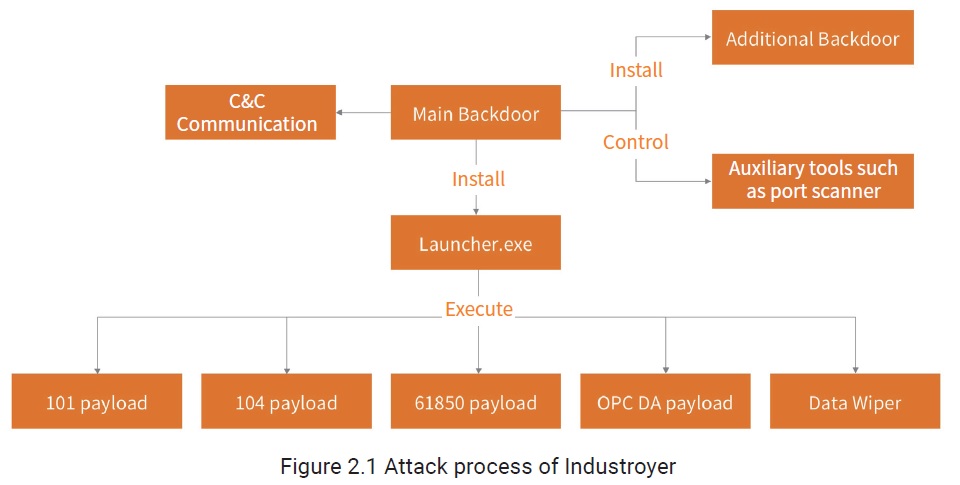
- Industroyer’s attack process is shown as follows:
Functional Modules
This malware consists of the following modules:
- Main Backdoor
A main backdoor communicates with port 443 on the remote C&C server through port 3128 of the local agent, receiving commands from the server for local execution.
- Launcher
The Launcher module is responsible for launching payloads. A new thread loads payload.dll, calls the export function called “Crash”, and performs attacks against industrial control protocols. Another thread loads the data wiper module haslo.dat, calls the export function called “Crash”, and performs the wipe operation.
- Data wiper component
The data wiper provides the following functions:
- Traverse registry keys in SYSTEM\\CurrentControlSet\\Services to change the value of ImagePath of all services to null. This operation will make system services unavailable and the system unable to restart.
- Traverse all local and network disk drives assigned disk letters from C to Z. If a file with a related extension is found, create a new thread to overwrite all contents of this file to compromise it.
- Enumerate system processes and terminate related ones, which will cause the system to crash.
- Scanner
As Industroyer has a port scanner built in, the -ip and -port parameters can be set to an IP address range and a port range for scanning.
- Additional tools: DoS tool
The DoS tool exploits the vulnerability (CVE-2015-5374) to target a SIPROTEC device from Siemens by sending a crafted 18-byte UDP packet to port 50000. After the attack is completed, the device stops responding to legitimate instructions until the device is manually rebooted.
Sum-up
Win32/Industroyer is a type of malware designed to target ICSs. It supports four industrial control protocols: IEC101, IEC104, IEC61850, and OPC DA. The sample contains multiple modules, with the main backdoor responsible for installing and running other modules, communicating with the C&C server to receive C&C commands, and performing the next-step operation as instructed. Attacks against industrial control protocols are completed by different payloads, causing the ICS to crash and making it deny service to legitimate users.
To be continued.