IcedID Banking Trojan Sample Technical Analysis and Solution Date of Release: November 17, 2017 Overview Recently, the IBM X-Force research team discovered a brand new banking Trojan dubbed IcedID. This Trojan was first found spreading in the wild in September 2017, mainly targeting systems used in the financial sectors of...
Categoria: Blog
BadRabbit Sample Analysis and Recommended Solution
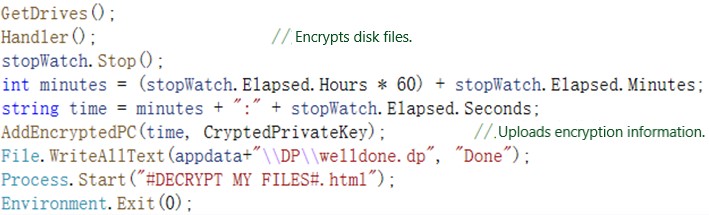
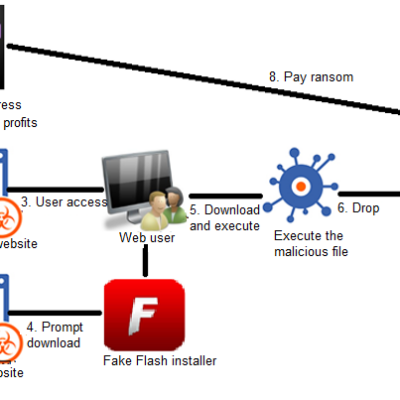
Overview A new type of ransomware was detected on October 24, when it had not been even half a year from the extensive breakout of the notorious ransomware Petya and WannaCry. This ransomware dubbed BadRabbit has been distributed in a number of European countries, including Russia, Ukraine, Bulgaria, Turkey, and...
Technical Analysis Report on Rowdy, A New Type of IoT Malware Exploiting STBs
In August 2017, NSFOCUS's DDoS situation awareness platform detected anoma-lous bandwidth usage over a customer's network, which, upon analysis, was confirmed to be a distributed denial-of-service (DDoS) attack. The attack was characterized by different types of traffic, including TCP flood, HTTP flood, and DNS flood. Tracing source IP addresses, we...
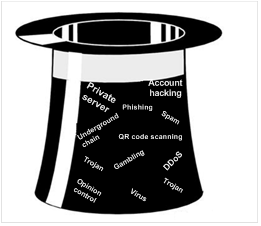
Past and Present of Underground Network Industry
The underground network industry has a long history and extensive coverage. What happened throughout its history? This document presents the definition, category, means, and examples of the underground network industry, as well as protection measures. Overview What is Underground Industry? Underground industry is a general name for a wide variety...
A Step Further — Demystifying XSS
Here is a comprehensive tutorial on cross-site scripting (XSS) attacks, ranging from entry to practice. Overview Note that XSS attacks are classified according to different angles in the preceding figure, but not simply classified into reflective XSS, stored XSS, and DOM-based XSS. In essence, XSS is injection of HTML code...
Analysis and Solution of Spring Data REST Server PATCH Request RCE Vulnerability
Overview Recently, Pivotal released a security advisory to reveal the Spring Data REST server is prone to a remote code execution vulnerability (CVE-2017-8046) when processing PATCH requests. Attackers could exploit this vulnerability by sending a crafted PATCH request to the Spring Data REST server. The submitted JSON data contains...