Overview
A new type of ransomware was detected on October 24, when it had not been even half a year from the extensive breakout of the notorious ransomware Petya and WannaCry. This ransomware dubbed BadRabbit has been distributed in a number of European countries, including Russia, Ukraine, Bulgaria, Turkey, and Germany, and is now found also in the USA.
Currently, BadRabbit mainly spreads via watering hole websites and does not use the previous EternalBlue vulnerability. Therefore, it is projected that its propagation scale will be smaller than that of Petya and WannaCry. Despite this fact, we should remind our customers to remain vigilant against attacks related to this ransomware.
Background
On October 24, 2017, a new type of ransomware called BadRabbit was found to be widely propagated in East European countries and Russia. Victims are enticed to install a fake flash player program. After this program is installed, the victim’s machine will be infected and files on it will be encrypted. To decrypt these files, the victim has to pay the demanded ransom.
Targets
BadRabbit mainly plagues East European countries and Russia, but it also shows its presence in Bulgaria and Turkey.
Attack Process
Propagation and Infection
Sample Delivery
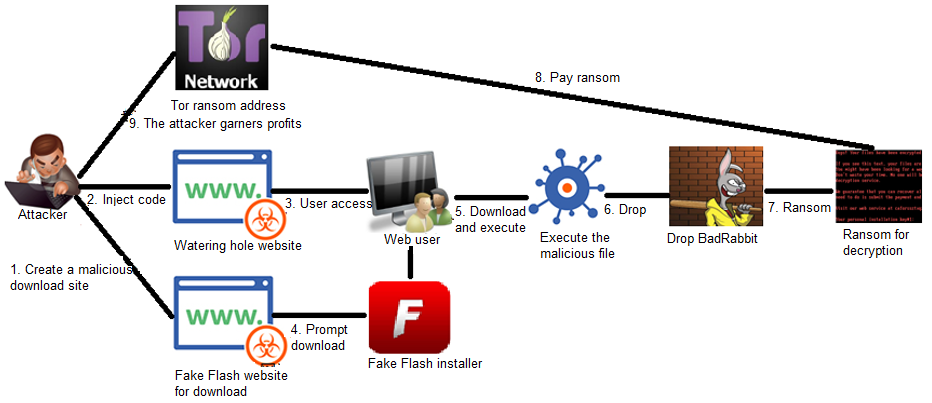
The sample is delivered via watering hole attacks. When accessing a watering hole website in which the attacker injects malicious code, a legitimate network user is prompted to install the Flash Player plug-in. If the user permits such operation, a fake Flash Player installer will be downloaded from the crafted malicious website (h**p://1dnscontrol[.]com/flash_install[.]php). Once the installer is executed, the user’s machine is infected.
Watering hole is a hacking strategy by which a watering hole is set up on the path that a victim must go through to the destination. The most common practice is as follows: A hacker analyzes the target’s network behavior patterns and finds weaknesses in the website that the target often visits. Then the hacker compromises the website and injects attack code in it, thus completing the process of infecting a website with a trojan. The target will get infected when he or she accesses this website.
Propagation and Infection
The sample uses brute-force methods to enumerate accounts and passwords for use of the SMB service. At the same time, the ransomware is spread by exploiting the EternalRomance (MS17-010) vulnerability.
Machine Analysis (Dynamic Behavior Detection)
NSFOCUS Threat Analysis Center (TAC) captured this malicious sample and graded its risk as “high”. The sandbox also detected the entire process from dropping the sample, creating scheduled tasks, and scanning ports 139 and 445 to attempting infection.
File-related Operations
According to detection by the sandbox, the executed sample drops and creates a number of malicious files and also creates scheduled tasks in the C disk drive to implement different functions.
Network Operations
According to detection by the sandbox, the executed sample scans ports 139 and 445 for subsequent propagation and infection.
Process Control
According to detection by the sandbox, the executed sample starts various malicious functional modules by dropping files and creating processes.
High-Level Analysis
The following figure shows the sample execution process.
File Structure
Original sample information:
- File Name: install_flash_player.exe
- Size: 441899 bytes
- File Version: 27.0.0.170
- MD5: FBBDC39AF1139AEBBA4DA004475E8839
- SHA1: DE5C8D858E6E41DA715DCA1C019DF0BFB92D32C0
- CRC32: 5FA1C9A5
Drop and create the sample (scheduled task):
- install_flash_player.exe: masqueraded as the Flash Player installer, which is actually the BadRabbit dropper
- infpub.dat: dropped dll file, which is the ransomware BadRabbit for subsequent encryption and ransom
- cscc.dat: for disk encryption (DiskCryptor)
- dispci.exe: used for installing BootLocker, encrypting files, and decrypting files after a reboot
- 4.tmp: Mimikatz module
- rhaegal.job: scheduled task for executing discpci.exe to encrypt files (/c schtasks /Create /RU SYSTEM /SC ONSTART /TN rhaegal /TR “C:\WINDOWS\system32\cmd.exe /C Start \”\” \”C:\Windows\dispci.exe\” -id 423694064 && exit”)
- drogon.job: scheduled task for rebooting the infected host and displaying the ransom note (/c schtasks /Create /SC once /TN drogon /RU SYSTEM /TR “C:\WINDOWS\system32\shutdown.exe /r /t 0 /f” /ST 15:40:00)
Technical Analysis
The fake Flash Player installer drops and executes the malware BadRabbit by creating files, writing to these files, and then creating processes pointing to the dropped files.
Infpub.dat drops the main programs dispci.exe and cscc.dat:

Infpub.dat creates a scheduled task (reboot):
Infpub.dat creates a scheduled task (for starting dispci.exe on boot):
Infpub.dat creates a decryption drive service:
Extensions of files that can be encrypted are listed as follows:
dispci.exe generates a ransom note:
dispci.exe uses the user’s password and public key for decryption operation in the decryption process:
Propagation Mode
After being executed, the sample drops Infpub.dat, which will attempt to propagate through IPC$ and SMB.
IPC$:
SMB:
The sample has built-in keys for cracking weak passwords for access to shared folders:
Encryption Algorithm
The sample calls the encryption drive to use the AES algorithm for disk encryption. The 32-byte random key is saved in memory.
This key, which is randomly generated by the CryptGenRandom function and Base64-encoded, is used for disk encryption and as a power-on password (password#1). The system can be accessed after the selected string is typed.
On the system, run dispci.exe (or its shortcut DECYRPT on the desktop) and type the key. Then the disk is decrypted and the boot is restored.
Files are encrypted as follows:
This part is conducted within infpub.dat. The sample randomly generates a 32-byte key to encrypt files with AES. This key is also saved in memory.
Like what have done before, run dispci.exe and type this binary string at the prompt for password#2.
The key generated by the sample will, together with the boot ID, computer name, and work group information, use the built-in RSA2048 key for encryption and Base64 encoding. The structure before encryption is shown in the following figure. The selected binary string is the disk decryption key.
Type the selected binary characters to unlock and access the system.
If no key is successfully captured from memory, the victim can only use the attacker-controlled RSA private key to decrypt the installation key before obtaining the correct password.
Mode of Payment
After the encryption is completed, the following extortion note is displayed:
The victim is instructed to access a Tor network address, type the personal installation key, and pay the ransom with bitcoin.
Ransom Amount
The ransom is 0.05 bitcoins which is about $285.00 or ¥1890.00 according to the current exchange rate.
Attack Location
Sample Download Website
The following is the queried information about the malicious sample download website (h**p://1dnscontrol[.]com/flash_install[.]php):
IP Address Location
IP address: 5.61.37.209
Country code: DEU/DE
Country: Germany
Latitude: 51.299301147461
Suggestions
Security Bulletin
NSFOCUS suggests that a security bulletin be published in either of the following ways (among others) across the company to let the entire staff be aware of the danger of ransomware and follow instructions so as to avoid unnecessary losses arising from negligence:
- WeChat/SMS/email
- Notice in the office environment
The following is an example of a security bulletin:
| Recently, the BadRabbit ransomware surfaced, following the outbreak of the WannaCry and Petya malware. We provide the following suggestions to help you prevent the ransomware from encrypting personal data and office documents:
1. Do not install software from unidentifiable sources. 2. Think twice before clicking the files and links from unspecified emails. 3. Turn on User Account Control (UAC) in the system, carefully read UAC alerts, and block the running of suspicious processes in time. Once finding that you have already been infected with the virus, you must immediately disconnect computers and servers on which files are encrypted by the virus, from the network. |
Secure Operations
- Do not download and install software before ascertaining its security.
- Turn on UAC in the system, carefully read UAC alerts, and block the running of suspicious processes in time.
- Disable the Windows Management Instrumentation (WMI) service and turn off ports 135, 139, and 445 on Windows-based hosts.
- If network sharing is unnecessary, disable it.
- For personal terminal devices, install antivirus software and upgrade rules to the latest version.
Ongoing Security Monitoring and Protection
The ongoing security monitoring and protection solution from NSFOCUS provides a dynamic security protection system in which NSFOCUS Threat Analysis Center (TAC) that detects known and unknown threats collaborates with on-premise NSFOCUS Network Intrusion Prevention System (NIPS), while NSFOCUS Threat Intelligence (NTI) provides security reputation data for the two devices. Besides, NSFOCUS’s professional emergency response team, together with regional service teams that offer onsite response and handling capabilities, provides onsite rapid troubleshooting, handling, and security enhancement for customers across the country.
Note: For details on the threat analysis capability of TAC, see Machine Analysis (Dynamic Behavior Detection).
Comparison Among Ransomware Families
| Ransomware Family | BadRabbit | WannaCry | Petya |
| Delivery method | Watering hole attack (PE) | Email attachment | Email attachment |
| Outbreak date | 2017-10-24 | 2017-05-12 | 2017-06-27 |
| Affected area | East Europe and Russia | Whole world | Multiple European countries, including Russia, UK, and Ukraine |
| Whether to create services | Yes | ||
| Exploit | EternalRomance | EternalBlue | EternalBlue |
| Whether to restart the system | Yes | No | Yes |
| Encryption algorithm | AES-128 RSA-2048 | ||
| Whether to modify the master boot record (MBR) | Yes | No | Yes |
| Ransom amount | 0.05 BTC (about $350 Nov. 2017) | 0.05 BTC (about $350 Nov. 2017) | 0.05 BTC (about $350 Nov. 2017) |
| Weakness | Randomly generated keys are not erased so that encrypted files may be decrypted by the ransomware. | If the killswitch domain is resolved, the ransomware’s malicious function can be blocked. | If a particular local file exists, the ransomware’s malicious function can be blocked. |
Detection and Protection Methods
NSFOCUS Detection Services
- NSFOCUS engineers provide onsite detection services.
- NSFOCUS online cloud detection: You can log in to NSFOCUS Cloud to apply for a trial use of the scanning service.
NSFOCUS Solutions for Removing Trojans
- Short-term service: NSFOCUS engineers provide the onsite trojan backdoor removal service (manual services + NIPS + TAC) to ensure that risk points are immediately eliminated from the network and the event impact is minimized. After the handling, an event analysis report is provided.
- Mid-term service: NSFOCUS provides 3- to 6-month risk monitoring and preventive maintenance inspection (PMI) services (NIPS + TAC + manual services) to eradicate risks and prevent events from recurring.
- Long-term service: NSFOCUS provides risk solutions for the fund industry (threat intelligence, attack source traceback, and professional security services).
Appendix
- Files with the following extensions can be encrypted by the ransomware:
.3ds .7z .accdb .ai .asm .asp .aspx .avhd .back .bak .bmp .brw .c .cab .cc .cer .cfg .conf .cpp .crt
.cs .ctl .cxx .dbf .der .dib .disk .djvu .doc .docx .dwg .eml .fdb .gz .h .hdd .hpp .hxx .iso .java .jfif
.jpe .jpeg .jpg .js .kdbx .key .mail .mdb .msg .nrg .odc .odf .odg .odi .odm .odp .ods .odt .ora
.ost .ova .ovf .p12 .p7b .p7c .pdf .pem .pfx .php .pmf .png .ppt .pptx .ps1 .pst .pvi .py .pyc .pyw
.qcow .qcow2 .rar .rb .rtf .scm .sln .sql .tar .tib .tif .tiff .vb .vbox .vbs .vcb .vdi .vfd .vhd .vhdx
.vmc .vmdk .vmsd .vmtm .vmx .vsdx .vsv .work .xls .xlsx .xml .xvd .zip
- Indicators of compromise
|
Item |
Value |
|
SHA256 hash |
630325cac09ac3fab908f903e3b00d0dadd5fdaa0875ed8496fcbb97a558d0da
8ebc97e05c8e1073bda2efb6f4d00ad7e789260afa2c276f0c72740b838a0a93 682ADCB55FE4649F7B22505A54A9DBC454B4090FC2BB84AF7DB5B0908F3B7806 0b2f863f4119dc88a22cc97c0a136c88a0127cb026751303b045f7322a8972f6 579FD8A0385482FB4C789561A30B09F25671E86422F40EF5CCA2036B28F99648 2f8c54f9fa8e47596a3beff0031f85360e56840c77f71c6a573ace6f46412035 301b905eb98d8d6bb559c04bbda26628a942b2c4107c07a02e8f753bdcfe347c |
|
Task |
viserion_
rhaegal drogon |
|
Domain |
1dnscontrol.com
caforssztxqzf2nm.onion |
|
IP address |
5.61.37.209 |