This chapter discusses various aspects of botnet behavior. Behavioral characteristics include activity level of botnets overall and per botnet family, DDoS attack characteristics, C&C server use and distribution, and geographical locations of attack victims. Also discussed are characteristics of the most active botnet families themselves.
3.1 Botnet Instructions
3.1.1 Behavior Seen
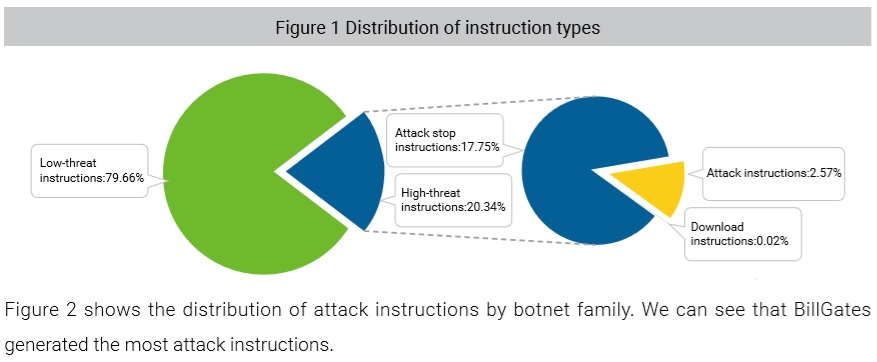
Botnets receive instructions from C&C servers. Instructions detected in 2018 can be divided into high-threat instructions and low-threat instructions. The former includes attack, attack stop and selfreplication/download instructions. The latter include heartbeat, information collection, and other communication instructions. Figure 1 shows the distribution of instruction types.
3.1.2 Analysis
Botnets Take Low and Slow Approach Through Reconnaissance and Testing
NSFOCUS has observed botnet controllers behaving more cautiously by repeatedly conducting reconnaissance and testing activities before issuing attack instructions.
It is generally accepted that the botnet kill chain consists of two phases: pre-intrusion and postintrusion. Controllers are very careful about delivering malicious programs prior to intrusion. They often try to reduce the odds of being detected by forging source IPs and domains, using multilingual texts, and adding misleading or meaningless information. In contrast, the delivered malicious programs behave more recklessly; they may use simple communication formats and exposed attack sources. Thus, detection of malicious behavior is traditionally performed at the post-intrusion phase.
Statistics show that many botnet families remain cautious during the “control” and “execution” phases. Botnet controllers often use information collection instructions to detect honeypots and obtain information about the host and running process. Using this information to better detect the running environment adds to the difficulty of spoofing them through sandbox masquerading.
Figure 1 shows the percentage of attack stop instructions and attack instructions among high-threat instructions. We see from this figure that botnet controllers minimize manipulating the infected bot. We suspect that the far larger number of attack stop instructions sent are redundant to guarantee that controlled nodes hosted on poorer performance networks can are made dormant in order not to be easily identified after the attack.
Based on how successful and prolific certain botnet attacks are, the above-mentioned information collection and attack stop instructions greatly raise the probability of survival of individual bots, making these botnet families less likely to be detected and tracked.
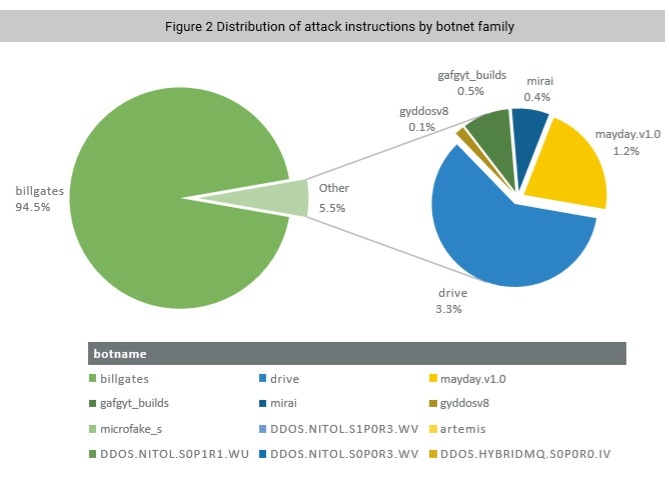
Several Mature and Full-Featured Botnet Families Starting to Dominate
Organized botnet groups prefer using stable botnet family versions and C&C servers. This reveals that botnet lifecycle includes a maturity phase.
According to statistics, although each botnet family has diverse variants and countless C&C servers distributed throughout the world, most of the effective attack instructions are issued from just a small group of C&C servers.
Let us use the BillGates botnet, the 2018 Q4 quarterly champion for the most active families, as an example. Among all its C&C servers detected in 2018, the two most active IP addresses, 23.*.*.131 and 207.*.*.245, issued more than 90% of all effective attack instructions. Of the family’s four variants in the wild, the original version discovered is the most active1.
Interestingly, different controllers exercise version control and C&C in a remarkably similar way, whether using DDoS families or families delivering other types of payloads, and on both mainstream and IoT platforms. Controllers using long-established and well-known families launch most attack tasks. While large numbers of attack instructions often lead to massive attack events, a mature full-fledged attack group with several elite bots receiving less attack instructions can impose far more damage than a looser collective of bots that churn out a larger number of attacks. NSFOCUS believes that improving our ability to detect and track different high-threat variants is important.
1ï¾ For detailed description of the BillGates family, see BillGates: Best Cross-Platform Family.
to be continued