Introduction to SYN Flood A three-way handshake is required to establish a TCP connection. First, the client sends a TCP SYN packet to the server. The server responds to the client request with an SYN-ACK packet. Then the server waits and expects an ACK packet from the client. At this...
Blog
NSFOCUS Continuously Dominating the Anti-DDoS Hardware Market in China with Unparalleled Market Share
According to the IDC China Anti- DDoS Hardware Market Share, 2022: Opportunities and Challenges Coexist published on June 29, 2023, NSFOCUS, with its Anti-DDoS solution powered by a robust protection algorithm and excellent services, has again claimed the leading position in China's Anti-DDoS hardware market. NSFOCUS keeps ahead of this...
Oracle Products Key Patches Update Notice for July 2023
Overview On July 19, NSFOCUS CERT found that Oracle officially released the Critical Patch Update in July with 508 vulnerabilities included. This security update involved Oracle WebLogic Server, Oracle MySQL, Oracle Financial Services Applications, Oracle Enterprise Manager, Oracle Retail Applications and other commonly used products. Oracle strongly recommends its customers...
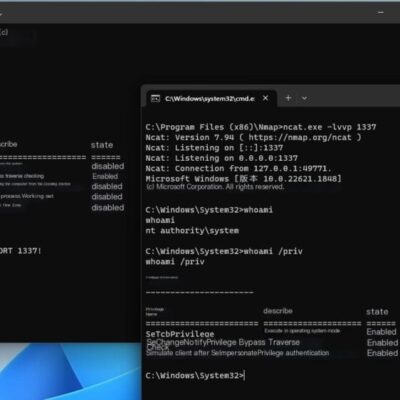
Windows Error Reporting Service Privilege Enhancement Vulnerability (CVE-2023-36874)
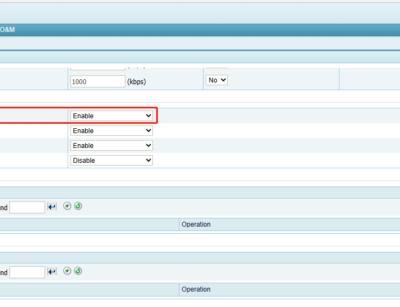
Overview NSFOCUS security team recently monitored that Microsoft released a security patch, fixing the Windows Error Reporting service privilege escalation vulnerability (CVE-2023-36874). An attacker who successfully exploited this vulnerability could gain administrator privileges. Microsoft's official security update announcement in July stated that attackers must have local access to the target...
Adobe ColdFusion Multiple Security Vulnerabilities Notification
Overview Recently, NSFOCUS CERT monitored that Adobe has officially released security notices and fixed multiple Adobe ColdFusion vulnerabilities. Affected users should take measures as soon as possible. The key vulnerabilities are as follows: Adobe ColdFusion Access Control Bypass Vulnerability (CVS 2023-29298): Adobe ColdFusion has an access control bypass vulnerability that...
Enhancing Campus Network Resilience: How NSFOCUS Anti-DDoS Solution Safeguards the Education Sector from DDoS Attacks
Customer Overview The customer is a leading research-intensive university in Asia, with a distinguished history and a reputation for excellence in teaching and research. The university has a large campus network that serves students, faculty, staff, external partners, and visitors. With the increasing threats of DDoS attacks, the customer recognized...