1. Â Background As early as 2016, a report from BitSight, an American cybersecurity ratings company, showed that Brazil is one of the riskiest countries to do business in. According to the cyber threat report released by SonicWALL, Brazil suffered more than 33 million intrusion attempts in 2021, and suffered ransomware...
Blog
IndoSec 2022
IndoSec was held at Hotel Mulia Senayan at Jakarta, Indonesia on September 6 and 7, 2022. We joined this event and showcased our hybrid DDoS mitigation solutions. Indonesia, the country with the fourth-fastest growth in internet users in the world, faces both great opportunities and significant threats as digital technology...
NSFOCUS Report: DDoS Attacks Skyrocketed by 205% in H1 2022
Santa Clara, Calif. September 6, 2022 – NSFOCUS, a global network and cyber security leader, today released NSFOCUS Global DDoS Landscape Report for the first half of 2022. Compared to the first half of 2021, DDoS attacks has a sharp increase of 205% year over year. Terabit attacks are not rare...
Investigation Report on New APT Organization MurenShark: Torpedoes Fired to Turkish Navy [2]
Part 1: Investigation Report on New APT Organization MurenShark: Torpedoes Fired to Turkish Navy [1] Characteristics of Attack Tactics Use compromised sites: MurenShark tends to use compromised sites as the file server and the C&C server in the attack process. As shown in the last chapter, the organization used the...
Investigation Report on New APT Organization MurenShark: Torpedoes Fired to Turkish Navy [1]
Overview In 2022 Q2, NSFOCUS Security Labs detected a series of cyberattacks against Turkey. After analysis, the researchers confirmed that this round of attacks originated from Actor210426, a new threat entity identified by NSFOCUS Security Labs in April 2021. Through the clues of behavior pattern, attack method, attack tool, attack...
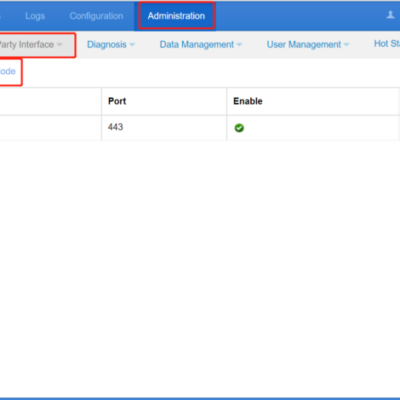
Configuring Collaboration Between ADS M and NTA
ADS M can manage NTAs, including checking NTA running status, time synchronization, dispatching IP group configuration of a region, displaying traffic information of NTAs, and receiving logs uploaded from NTAs. The steps to configure the collaboration between ADS M and NTA are as follows: Configuring NTA Step 1: Choose Administration...