Part 1: Investigation Report on New APT Organization MurenShark: Torpedoes Fired to Turkish Navy [1]
Characteristics of Attack Tactics
Use compromised sites:
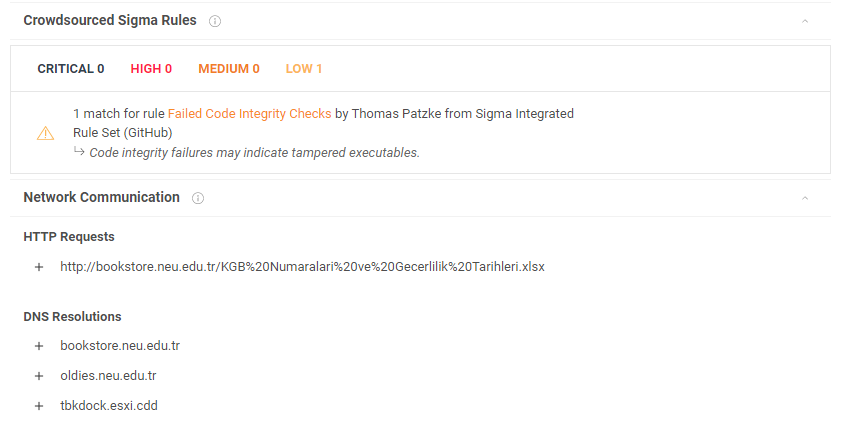
MurenShark tends to use compromised sites as the file server and the C&C server in the attack process. As shown in the last chapter, the organization used the Near East University site (Yakın Doğu Üniversitesi) (https://neu.edu.tr/) as a remote server.
The Near East University is a private university located in Northern Cyprus. The known attack process shows that MurenShark has controlled the official website server of the university for more than one year, placed Trojan horse programs in multiple locations on the website, run the LetMeOut Trojan horse server program, and even deployed the server of the CobaltStrike penetration platform to continuously control the victims.
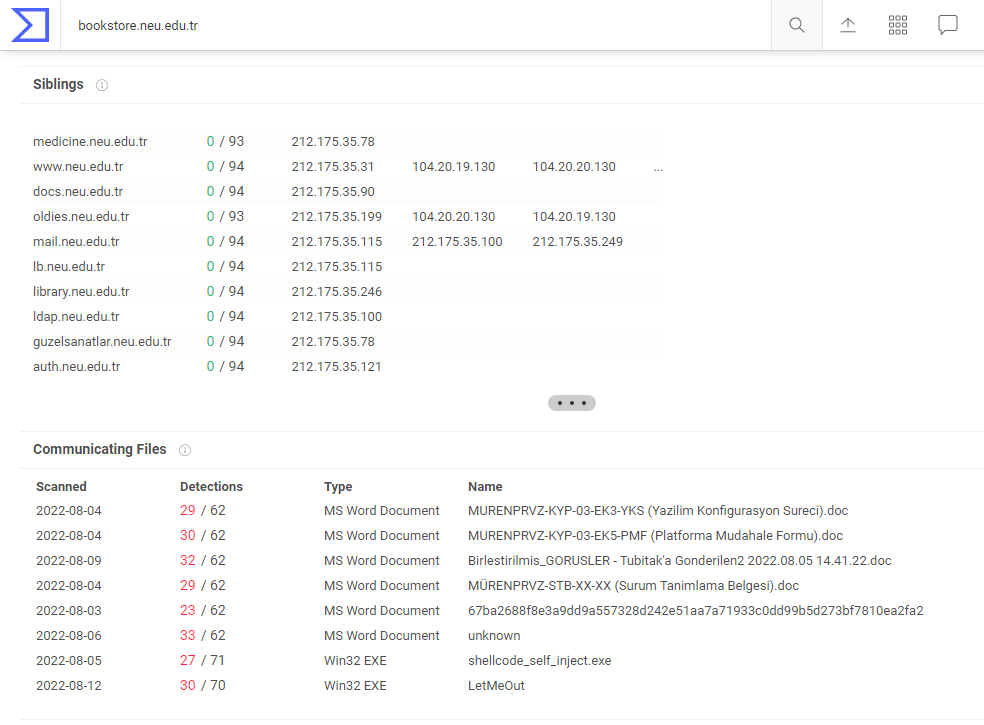
Although it has such attack resources, MurenShark is relatively restrained in the use of the compromised sites. These sites are silent for most of the time and have not been traded or abused. This utilization of the compromised sites by MurenShark effectively hides the traces of organization and extends the available period of resources.
Breakdown of component behaviors
When designing the process, MurenShark follows a special pattern of behavior splitting.
For example, the new version of NiceRender attack component recently used by the organization divides the malicious documents’ normal functions into two parts. Part A is designed as a macro code reader and injector, and part B is designed as a macro code carrier and injection carrier. Part A needs to obtain Part B through network connection to carry out the complete component behavior.
For example, the LetMeOut Trojan program commonly used by the organization will also split its download function into two parts. The Trojan first uploads the Trojan information and the victim host information to the C&C server . After receiving the confirmation information from the server, the Trojan obtains the download path of the subsequent payload through calculation.
The advantages of this design are obvious. In cooperation with the compromised site described above, when the remote address of these components fails or stops service, there will not be any malicious behavior characteristics on the network side and the process side, and even untrained personnel cannot detect abnormalities when opening the corresponding files. These subdivided component behaviors also interfere with forensics analysis and attack process restoration. A large number of interaction mechanisms effectively protect the network resources and attack components in the process and reduce the exposure probability.
When the C&C server is disconnected, the behavior of the new version of NiceRender is similar to that of the normal document:
Known Attack Tools
NiceRender
This tool is a malicious macro type document with a specific execution mode. MurenShark attackers use this tool to create various phishing documents and use them as the preliminary step of attack activities. There are currently two versions of this tool.
NiceRender Ver.1
The early version of NiceRender includes three functional parts: bait decoding, online notification and payload release.
(I)Decoy decoding
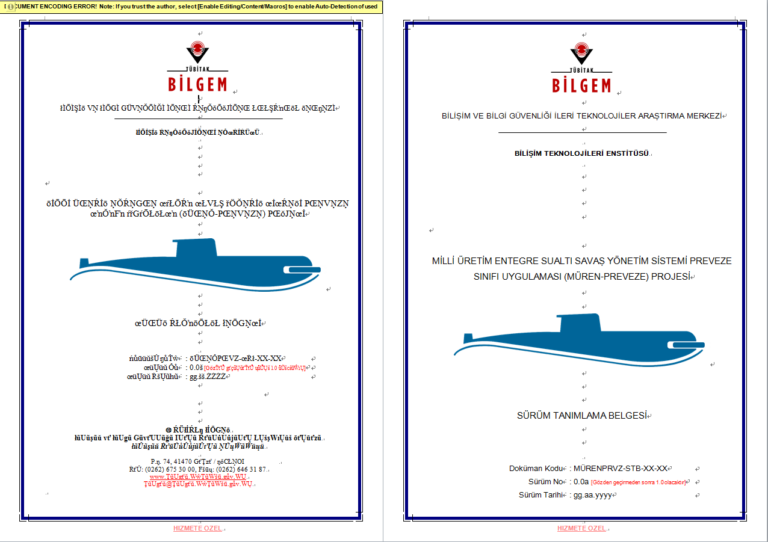
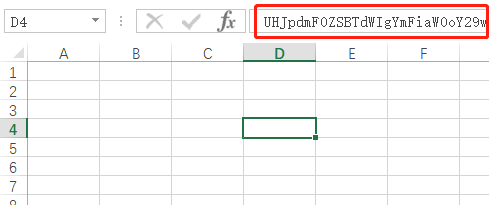
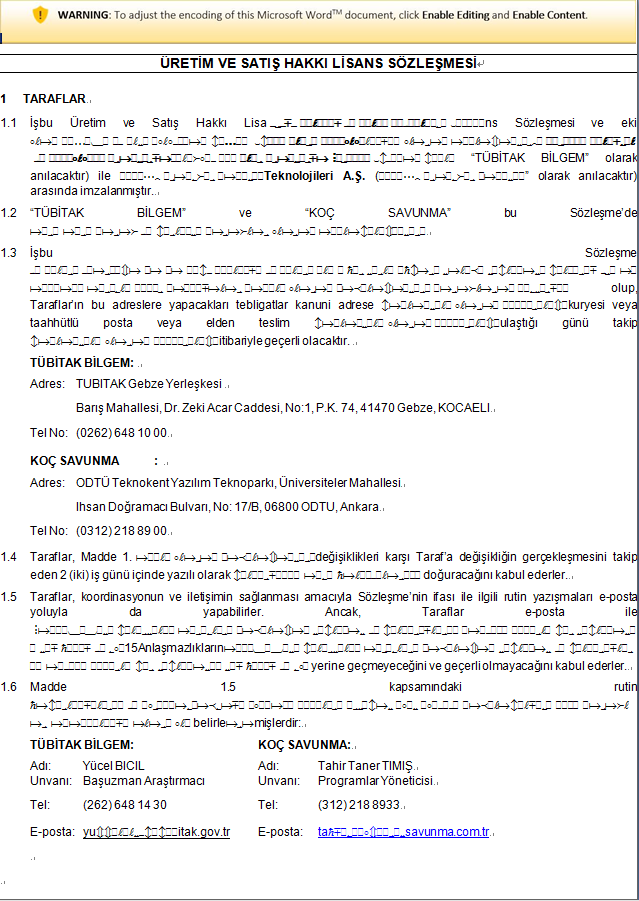
The biggest difference between NiceRender and other common phishing documents is that the component will use a unique logic to transcode the text content in the document into garbled characters, and decode these garbled characters, giving the victim an illusion that the encrypted document has indeed been decrypted, thus increasing the credibility of such phishing documents.
NiceRender’s character transcoding logic is to search for specific wide byte characters and convert them into corresponding ASCII characters.
The decimal value sequence corresponding to the wide character to be converted is:
[321, 325, 338, 334, 332, 331, 324, 329, 335, 333, 341, 340, 339, 322, 345, 353, 357, 361, 370, 366, 364, 363, 356, 367, 365, 373, 372, 371, 354, 377]
The corresponding ASCII character sequence is:
[A, E, R, N, L, K, D, I, O, M, U, T, S, B, Y, a, e, i, r, n, l, k, d, o, m, u, t, s, b, y]
After the conversion is completed, NiceRender will hide the “enable editing” notification at the top of the original content to further improve the credibility of the document.
The following figure shows the comparison between the original content of a typical NiceRender bait and the effect after transcoding.
(II) Online notification
This version of NiceRender has a special operation, which will notify the attacker through the network when the macro code is running.
This notification operation is realized through the DNS resolution mechanism. The NiceRender producer first registers the domain name “cachedns. IO” and binds the resolution server of the domain to itself:

When the macro code of the NiceRender document runs, the current timestamp will be obtained and combined into a domain name in the following format:
[timestamp]. D0g3.cachedns.io
The Trojan then performs DNS query on the domain name. Since the attacker has set the primary domain as described above, the DNS related query request will be directly sent to the domain name server deployed by the attacker. The attacker can read the domain name and obtain the tag (d0g3) and running time (timestamp) information of the corresponding NiceRender component to control the running state and attack scale of the component.
(III) Payload release
NiceRender then reads the text information in the specific object in the document, obtains a PE file and saves it to %LOCALAPPDATA%\Microsoft\EdgeFss\FileSyncShell64.dll. The PE file is the UniversalDonut Trojan.
It should be noted that NiceRender uses a COM component hijacking policy to load the DLL file. The tool adds a running key to the windows scheduled task MsCtfMonitor by modifying the registry key, which points to the above DLL file path to run malicious programs.
The specific implementation of the hijacking logic can be referred to:
https://github.com/S3cur3Th1sSh1t/OffensiveVBA/blob/main/src/COMHijack_DLL_Load.vba
UniversalDonut
MurenShark attackers frequently use a Trojan program in the form of DLL as a transitional component in their attack process. NSFOCUS Security Labs named it UniversalDonut according to the key information of this component.
UniversalDonut is a Trojan program of shellcode loader type. After the Trojan is executed, first detect the following items:
- Check whether the parent process name is C: \ windows \ system32 \ taskhost.exe;
- Detect whether it is a high privilege process
After the detection passes, the Trojan uses the multibyte XOR algorithm to decrypt a section of shellcode contained in the resource section and run it.
The shellcode carried by UniversalDonut is a complete payload generated by an open source framework Donut (https://github.com/TheWover/donut). With this framework, UniversalDonut can implement a large number of countermeasures in the shellcode execution stage, including Chaskey algorithm encryption, AMSI / WDLP bypass, connectivity detection, etc. Most importantly, the. Net support provided by Donut allows MurenShark attackers to use this shellcode to load LetMeOut, the main Trojan horse in subsequent stages.
LetMeOut
LetMeOut is a kind of .Net downloader Trojan, equipped with a unique insurance mechanism. MurenShark has used this Trojan horse many times in the invasion process.
The main code logic of LetMeOut is divided into two parts:
The program first confirms whether there is a binary file named FileSyncShell64.dat under the directory %LOCALAPPDATA%\Microsoft\EdgeFss\. If the file is found, decrypts and decompresses the file using the multibyte XOR algorithm and gzip compression algorithm, and then loads it into memory for operation.
Judging by the behavior, the FileSyncShell64.dat is an encrypted Trojan file cached locally by the Trojan program after C&C communication.
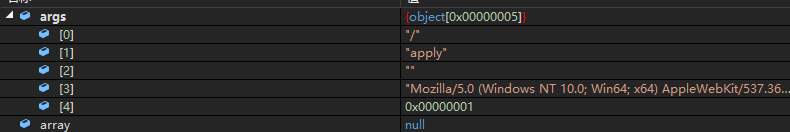
If a file named FileSyncShell64.dat is not found in the specified directory, the Trojan will specify the C&C server address for HTTP communication, and attach three pieces of information in the HTTP parameter section.
P1 base64 transcoding, Current proxy content
P2 base64 transcoding, http User-Agent content
P3 Boolean value, TRUE or FALSE on 64-bit process
Thenthe program makes a second HTTP request to obtain the contents of a hash path obtained through calculation. The hash path is calculated by the following parameters:
The decryption method of the encrypted content contained in the reply package is the same as that of the FileSyncShell64.dat file. The LetMeOut Trojan will run the decrypted content in the form of shellcode.
CobaltStrike
MurenShark uses the famous CobaltStrike penetration platform to manage the invaded hosts, and completes horizontal movement and secret theft through the CobaltStrike Beacon Trojan horse program.
Related Investigation
Attack on Scientific and Technological Research Council of Turkey
According to the investigation conducted by NSFOCUS Security Labs, one of the main targets of MurenShark, Scientific and Technological Research Council of Turkey, is not the first time to be attacked. As a top scientific research institution that has undertaken a large number of national projects in Turkey, it is a key victim of various hacking activities and even APT activities.
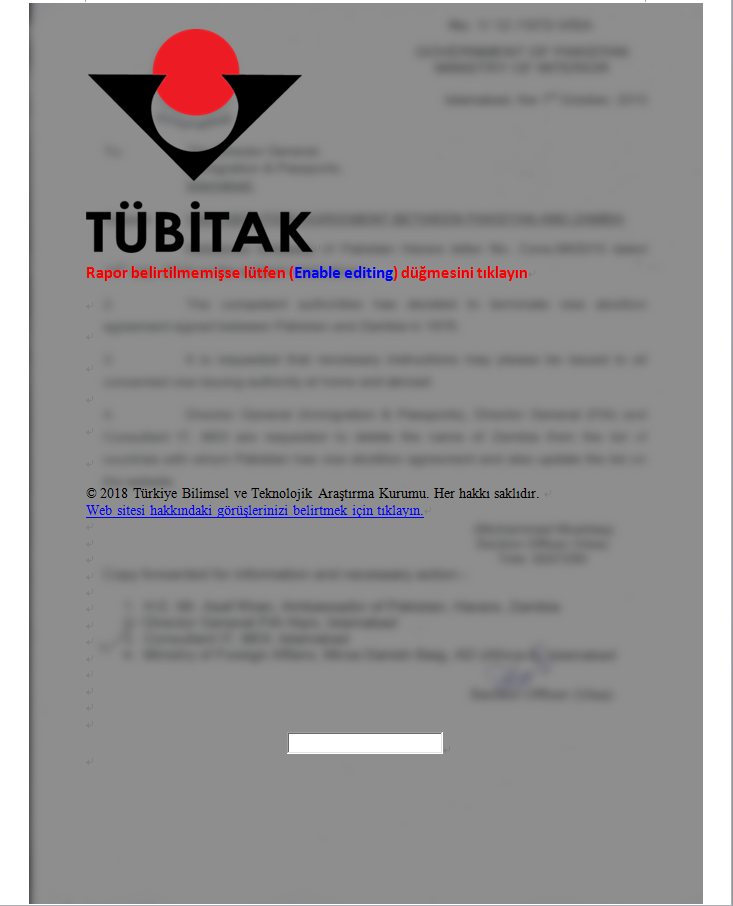
A type of frequent attacks against this institution are launched in the form of phishing emails. The attackers use common payloads such as compressed package attachments and vulnerability documents to deliver AgentTesla and other secret theft Trojans to the users of tubitak.gov.tr mailbox, and collect files, credentials and browser cache data on the victim’s host.

There are also some e-mails with forged quotation request and organization pictures of Scientific and Technological Research Council of Turkey in the mail body, and the attachments of the e-mails carry AgentTesla Trojan horse in the form of compressed package.

The above-mentioned attacks are very typical in the phishing mail activities in recent years. The mail hacker organization will use this method to steal various documents in the victim’s host and sell them in black market. These phishing emails indicate that Scientific and Technological Research Council of Turkey has been exposed in a high risk of data leakage for a long time. Another type of attack is more serious, directly from MuddyWater, an Iranian APT organization. MuddyWater launched a series of phishing attacks against Scientific and Technological Research Council of Turkey around 2019. The process of such attacks is relatively simple, that is to use several types of PowerShell Trojans by delivering bait documents with keyword “TÃœBÄ°TAKâ€.
After finding this clue, NSFOCUS Security Labs launched an investigation into the possible relationship between MurenShark and MuddyWater.
NSFOCUS Security Labs has reproduced the known activities and wild samples of muddwater for Turkey science and Technology Research Institute, and compared them with MurenShark activities in the following dimensions:
Comparison of related activities
| MurenShark | MuddyWater | |
| Direct target | Scientific and Technological Research Council of Turkey or Turkey military | Scientific and Technological Research Council of Turkey |
| Initial payload | Phishing documents | Phishing documents |
| Bait type | Recoverable document | unrecoverable document |
| Attack tools | UniversalDonut, LetMeOut | POWERSTATS or other PowerShell Trojan |
| Network resource | Compromised site | VPS server |
| Final payload | CobaltStrike Beacon Trojan | PowerShell back door |
Through comparison, it can be seen that the differences in characteristics between MurenShark and MuddyWater are greater than the commonalities. The two show similarities in attack target selection and initial stage components, but there is no overlap in subsequent execution processes.
In general, since the attack activities of MuddyWater are relatively intensive, MuddyWater attackers appear to be impatient in component design and resource use. In its activities against Scientific and Technological Research Council of Turkey, the organization copied the known attack methods, and the component design was relatively rough. In the process of disk recovery, NSFOCUS Security Labs observed design defects such as irreducible bait content and reusing the exposed C&C server address. On the contrary, MurenShark developers are more careful in the design of components and processes, focusing on hiding behavior traces and personal information to reduce exposure risks.
MuddyWater is an old-fashioned APT organization whose actions represent Iran’s national interests. The intersection of MurenShark and MuddyWater in terms of attack targets provides a few clues for the subsequent determination of organization affiliation.
Summary
MurenShark is a new APT organization targeting at Turkey. Through investigation and analysis, NSFOCUS Security Labs explored the main activities and technologies of the organization, and determined its independence and APT attributes. The results of the investigation show that the organization has clear targets and rich experience in confrontation. There are still many mysteries to be explored.
The complex international relations in the Middle East lead to the generation of various APT organizations, many of which have a history of attacks against Turkey. NSFOCUS Security Labs will continue to pay attention to the activities and changes of MurenShark.
IoCs
NiceRender ver.1
0a286239b3fe2e44545470e4117f66eb
88bba0077207359cdb9bddb3760f1f32
423cff633679c5dc1bfb27b4499eb171
NiceRender ver.2 partA
3592e56022ce1d87000e36cc0dd37d0e
bb9e1f1e5ef6f3f9f8de6d12d626c435
11a5c681e108cf84a2cc669e8204ac53
0a768a5c9f4714f7ca92545baf9f72c9
a92c6617aa28d4041c44f4b9cc3a5fa3
9a31e7918ae4de42c28d67e711802f58
NiceRender ver.2 partB
07e4844bde106bb6786e9e767d376408
9a0889667c89e592914e74916fd1ec56
468b3eaf031b5aef98b34b5ce39facad
c0f37db18293732872643994e12a4ad2
44da01a0a636a6fa3141c698f3bb2673
UniversalDonut
e6c1685e504fe1d05aa365c79a5e0231
32704a3fb28508e3b15bbbd28716ec76
dc60577efe1d18c05b7c90853bac4c86
349341fe3519a81c0178c5840009cf87
LetMeOut
156e197d7838558f44eed800b3b3ee8a
0f5b520120008ca6969ccad439020f98
d509145bcf4e6af3de1a746609c23564
156e197d7838558f44eed800b3b3ee8a
CobaltStrike Beacon
e4b353f731739487dd48e322bf540405
URIs
http[:]//jc.neu.edu[.]tr/apply
http[:]//jc.neu.edu[.]tr/r_main.js
http[:]//bookstore.neu.edu[.]tr/KGB%20Numaralari%20ve%20Gecerlilik%20Tarihleri.xlsx
http[:]//bookstore.neu.edu[.]tr/ara
d0g3.cachedns[.]io