Adobe Security Bulletins for September 2019 Security Updates Threat Alert

setembro 27, 2019
Overview
On September 10, 2019, local time, Adobe officially released September’s security updates to fix multiple vulnerabilities in its various products, including Adobe Application Manager and Adobe Flash Player. (mais…)
IP Reputation Report-09222019

setembro 26, 2019
Top 10 countries in attack counts: The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at September 22, 2019. Top 10 countries in attack percentage: The Laos is in first place. The Palestine is in the second place. The country China (CN) is […]
Windows Remote Desktop Services Remote Code Execution Vulnerability (CVE-2019-0708) Exploit Disclosure Threat Alert
setembro 25, 2019
-
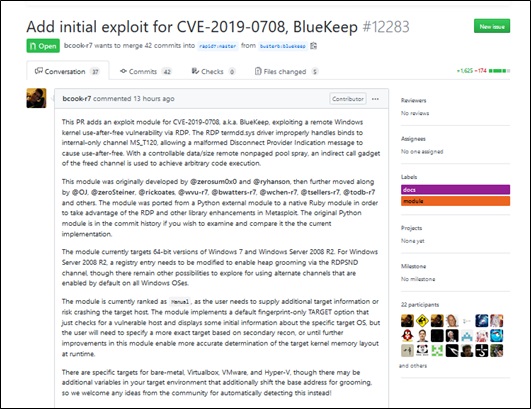
Exploit Disclosure
In the early morning of September 7, Beijing time, a developer disclosed a Metasploit exploit module for the Windows remote desktop services remote code execution vulnerability (CVE-2019-0708) on GitHub. The initial public exploit module (BlueKeep) for the CVE-2019-0708 vulnerability could cause old versions of Windows (Windows 7 SP1 x64 and Windows 2008 R2 x64) to execute code remotely without user interaction. This vulnerability, like WannaCry, will propagate widely, having constituted security threats in the wild.
Confluence Local File Disclosure Vulnerability (CVE-2019-3394) Handling Guide

setembro 24, 2019
-
Vulnerability Description
Recently, Atlassian released a security advisory, announcing remediation of a local file disclosure vulnerability (CVE-2019-3394) in Confluence products. (mais…)
NSFOCUS 2018 Annual Report on Cybersecurity Incident Observations

setembro 23, 2019
1 Introduction
According to the Statistical Report on China’s Internet Development[①] released by China Internet Network Information Center (CNNIC) in February 2019, China’s online population had reached 829 million, with an Internet penetration rate of 59.6%, by the end of 2018. The Internet has shown its presence in every segment of national economy, with a direct influence on national development and people’s work and livelihood. While the Internet technology is gaining momentum for rapid growth, cybersecurity incidents, powered by more and more novel attack methods, are becoming increasingly varied, endangering normal operations of governments and enterprises and affecting people’s daily lives. (mais…)
Multiple Cisco Products Contain Critical Vulnerabilities Threat Alert

setembro 20, 2019
Overview
On August 21, 2019, local time, Cisco officially released multiple security advisories, announcing remediation of critical vulnerabilities in a number of products. These vulnerabilities include authentication bypass and remote code execution vulnerabilities and the most critical one gets a CVSS score of 9.8. (mais…)
Botnet Trend Report-14

setembro 18, 2019
Conclusion and Recommendations
In 2018, botnets continued using DDoS as their primary weapon to attack regions with ubiquitous high speed networking for direct economic gains. However, they underwent significant changes in behavioral patterns, host platforms, C&C server deployment, infection methods, attack methods, and payload types. Security service providers need to adapt their strategies to better mitigate the increasing threats posed by the new generation of botnets. (mais…)
Aspose Remote Code Execution Vulnerabilities (CVE-2019-5032/5033/5041) Threat Alert
setembro 17, 2019
Overview
Recently, Cisco Talos published several technical analysis reports, claiming that Aspose.cells and Aspose.words in Aspose products contain remote code execution vulnerabilities, which can be exploited via a maliciously crafted file to result in remote code execution. (mais…)
Computrace That Is Whitelisted Can Pose Hybrid Threats

setembro 16, 2019
Recently, an article titled “Tips for Security Risks of Anti-theft and Tracking Software from Absolute” has been widely circulated on the internet, sparking public debate on the software LoJack for Laptops developed by Absolute. This software in question is also known as Computrace, with features including the abilities to remotely lock, delete files from, and locate the stolen laptop on a map. In fact, the security issues of Computrace was already exposed to the public as early as in 2009. Following is a review of its security threats. (mais…)