Recently, an article titled “Tips for Security Risks of Anti-theft and Tracking Software from Absolute” has been widely circulated on the internet, sparking public debate on the software LoJack for Laptops developed by Absolute. This software in question is also known as Computrace, with features including the abilities to remotely lock, delete files from, and locate the stolen laptop on a map. In fact, the security issues of Computrace was already exposed to the public as early as in 2009. Following is a review of its security threats.
1 Cause
Computrace’s security threats have exist for a decade and have been mentioned many times at international security conferences. This also shows that Computrace is susceptible to security risks and has been a top concern in the security realm. Reports released in recent years show that this software is suspected of being exploited by the APT28 group as a sharp weapon to carry out APT attacks, posing serious security hazards.
Next, we will make a detailed analysis of security hazards and the attack surface of Computrace.
2 Threat Attack Surface Analysis
2.1 Working Principle of Computrace
According to research findings released by Black Hat in 2014, Computrace exists In a BIOS ROM in a computer. You can determine whether to activate Computrace under BIOS Security Options. Computrace, once activated, follows a four-stage workflow:
Stage one: During the BIOS start-up process, Computrace will look up autocheck.exe in the file system then back up and modify it, or modify the MBR in the hard disk drive in a bid to control the computer upon system start-up.
Stage two: Computrace accesses the file system through Windows NT’s local interface to delete rpcnetp.exe, creates a new service named rpcnetp and modifies the registry before finally resuming autocheck.exe.
Stage three: rpcnetp.exe starts as a service, changes itself as a DLL file, and loads it into memory. After that, it creates the svchost.exe subprocess and suspends it, and injects the DLL file into the subprocess. After resumption, the svchost process will create a new subprocess iexplore.exe and suspend it. Likewise, this process injects the DLL file into the iexplore.exe subprocess. After resumption, the svchost process will connect to the server to obtain new commands and download the encryption module wceprv.dll, upgrade module upgr.exe, main module rpcnet.exe and the identprv.dll module. Finally, Computrace deletes the service and rpcnetp.exe created in the second stage, and then registers and starts a new service for rpcnet.exe.
Stage four: rpcnetp starts as a service, and creates the svchost process and performs other operations to connect to the server in a similar way as the third stage. Then the service will search for settings in the registry, file system and itself, configure the connection to the remote server to provide extendable remote access to the server.
2.2 Security Hazards of Computrace
- BIOS resident
As indicated above, Computrace exists in the computer’s BIOS as the hardware supplier directly writes it into the BIOS. Therefore, Computrace can persist in the operating system. Even if the hard disk is replaced or the operating system is reset after an update is applied, this software still exists.
- Continuous information transmission
Computrace, by default, will connect to the server one time at startup, and will do this every 24 hours when the computer runs, unless its default configuration is modified on the server.
- Unauthorized activation
According to Kaspersky’s statistics in 2014, more than 2 million Computrace have been activated, affecting most computer brand suppliers. For some of the suppliers, Computrace in BIOS security options are in the activated state by default or activated in an unauthorized way. Configuration options in BIOS can only be changed one time, and therefore the configuration, once changed, cannot be changed again.
2.3 Exploitable Attack Surface
In addition to the security hazards mentioned above, Computrace also has an exploitable attack surface. These security hazards, once ingeniously exploited together, could pose huge security threats in some special scenarios.
- Computrace cannot be permanently banned on X brand computers.
At the OffensiveCon19 conference, the research finding of a foreign researcher named akendo showed that Computrace cannot be permanently banned on X brand computers. Computers of this brand have a structure called SecurityConfigs, which stores Computrace’s security configurations, including activation and deactivation settings. In addition, those computers have an SMI (System Management Interrupt) service of ComputraceSmiService. The callback function of the SMI service can modify Computrace security configuration. In this way, Computrace activation status can be changed. Although this function is secured by a password protection mechanism, the key used is of four bytes, which perform authentication by means of cyclic comparison. In this case, the key can be cracked very quickly if being cracked byte by byte. When gaining local execution privileges of a computer of this brand, an attacker could use the above method to render Computrace on this computer always activated. Although Absolute has issued several statements to claim that there is no security issue with activated Computrace, this security problem actually exists in an X brand computer.
- Being white-listed
The working mechanism of Computrace is described in detail in the research findings released by researchers from Core Security Technologies and Kaspersky. Although Computrace has some technologies commonly used by malware, including injecting into memory of another process and establishing confidential communications, Microsoft systems and many anti-virus software suppliers do not detect Absolute’s Computrace module, but only mark it unsafe instead of malicious. Plaintext data transmission
Likewise, at the 2014 Black Hat conference, foreign researchers introduced the traffic protocol format of the 2008 version of Computrace. They indicated that the traffic is transmitted in plaintext without using any encryption algorithm, except that a simple algorithm is employed to check data integrity. Also, they revealed the simple check algorithm used by Computrace. Therefore, the data and checksum can be forged using the public available protocol format, in a bid to tamper with communications. This lays a foundation for man-in-the-middle attacks.
- Configuration that can be tampered with
According to the workflow described above, Computrace will search for configuration information in the registry, file system and itself, and connect the server by reference to domain name information as indicated in the configurations. Among the configurations, the server configuration information is encrypted by performing an XOR algorithm on the key and one-byte server configuration information. Thus an attacker can easily crack and replace the domain name information in the configuration, and change the server’s IP address to that of the controlled server, thus taking control of the victim’s computer to execute arbitrary codes.
To sum up, Computrace can be activated in an unauthorized way in a computer’s BIOS or cannot be permanently banned on computers of a certain brand. Besides, this software is whitelisted by many security vendors and lays a foundation for man-in-the-middle attacks. Therefore, this software’s security issues can could exploited by cyber criminals to turn Computrace into a sharp weapon and use it undetected for a long time.
3 Check
BIOS Check
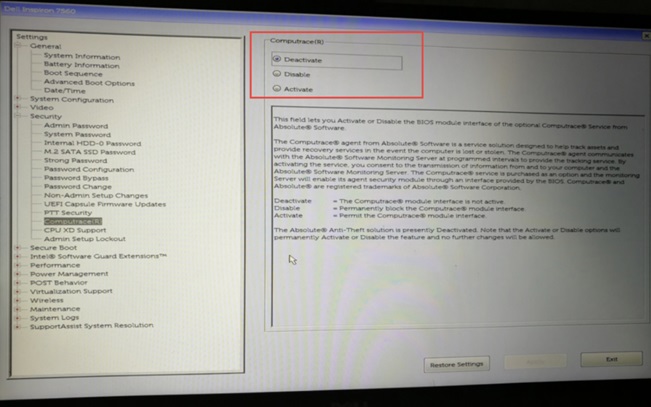
After restarting a Dell computer, press F2 to get into the BIOS, then expand Security options on the left pane and click the suboption Computrace. If the option is Activate, it means Compurtace is activated; Deactivate means deactivated; Disable means disabled. For computers of other brands, perform the same BIOS check.
Figure BIOS option of Dell Inspiron 7560 (deactivated by default )
Process Check
Check whether there are related processes such as rpcnet.exe, rpcnetp.exe, rpcnet.dll, and rpcnetp.dll. If so, it means the software is running.
4 Security Tips
- Solution 1: Prohibit the running of the software.
Step 1: Open the registry editor and locate the following:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager
Delete the right BootExecute key value (autocheck autochk * by default) after backup to prevent the program from automatically restarting subsequent processes.
Step 2: Terminate the relevant process in the task manager and delete rpcnet.exe, rpcnetp.exe, rpcnet.dll, and rpcnetp.dll in the System32 directory. Remember not to restart Windows.
Step 3: Create the above four files with empty contents in the System32 directory. Perform the following steps for each file: Right-click the file and select Properties to open the Properties page. Then click the Security tab and set Permissions for SYSTEM to Deny Full control.
- Solution 2: Prohibit the software from accessing the network.
Modify the hosts file to deny access from certain domain names: Open the hosts file in C:\Windows\System32\Drivers\Etc with Notepad, type the following information, and save it.
- 0. 0. 1 search. namequery. com
- 0. 0. 1 search. namequery. com
- 0. 0. 1 search2. namequery. com
- 0. 0. 1 search64. namequery. com
- 0. 0. 1 search. us. namequery. com
- 0. 0. 1 bh. namequery. com
- 0. 0. 1 namequery. nettrace. co. za
- 0. 0. 1 m229. absolute. com
Furthermore, configure the firewall to deny network access from rpcnet.exe and rpcnetp.exe.
- Solution 3: Block domain names on firewalls or DNS servers.
- Others:
In addition to the above general solutions, such as prohibiting software from running or intercepting network requests, we provide other solutions here:
- Change the operating system to a Linux distribution
- Call Absolute customer support.
5 Summary
To sum up, in this document, we have discussed security issues and hazards of Computrace of the 2008 version by reference to research findings presented at the 2014 Black Hat conference. Currently, no new security vulnerabilities and threats are found in the new version.
Network security threats lurk in many walks of our daily life. Unlike the 0-day vulnerability, an issue of great concern, Absolute’s Computrace, being whitelisted, is like a natural backdoor which contains possible hijacking conditions. This kind of non-0-day hybrid threats, which tend to be overlooked, are highly likely to become one of focuses for threat discovery and capture.
6 Reference
https://www. blackhat. com/docs/us-14/materials/us-14-Kamluk-Computrace-Backdoor-Revisited-WP. pdf
https://securelist. com/absolute-computrace-revisited/58278/
https://www. absolute. com/en/resources/faq/absolute-response-to-arbor-research
http://itsecchina. com/web/xxk/ldxqById. tag?CNNVD=CNNVD-201805-407
http://news. kaspersky. com. cn/news2014/02n/140212. htm
https://www. netscout. com/blog/asert/lojack-becomes-double-agent