-
Vulnerability Description
Recently, Atlassian released a security advisory, announcing remediation of a local file disclosure vulnerability (CVE-2019-3394) in Confluence products.
This vulnerability exists in the Word export function of Confluence Server and Confluence Data Center. An attacker who has Add Page space permission could exploit this vulnerability to read arbitrary files in the <install-directory>/confluence/WEB-INF/ directory on the Confluence server. The vulnerability may lead to disclosure of the following information, depending on files actually stored on the server:
- Source code of .jsp files
- ./classes directory
- LDAP credentials (in atlassian-user.xml)
- Other sensitive information that may exist
References:
https://jira.atlassian.com/browse/CONFSERVER-58734
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-3394
https://confluence.atlassian.com/doc/confluence-security-advisory-2019-08-28-976161720.html
-
Scope of Impact
Affected Version
- 1.0 to 6.6.16 (excluded)
- 7.0 to 6.13.7 (excluded)
- 14.0 to 6.15.8 (excluded)
Unaffected Versions
- 6.16
- 13.7
- 15.8
Note: Atlassian has indicated that Confluence Cloud is not affected by the vulnerability in question.
-
Check for the Vulnerability
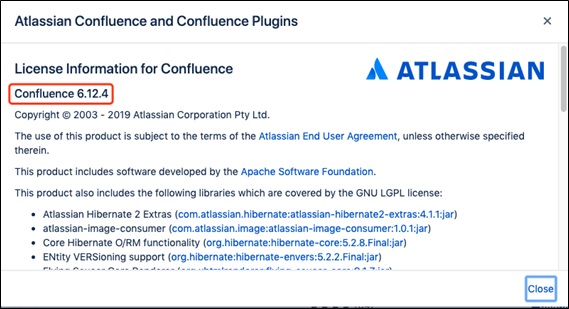
Users can check the current Confluence version to determine whether it is affected. For this purpose, users can click  and select About Confluence to check the current version of Confluence.
-
Recommended Mitigation Measures
-
Official Fix
-
The vender advises users to upgrade Confluence Server and Confluence Data Center to the latest versions to ensure the security and stability of the related services.
Check the upgrade path. Users of Confluence of earlier versions can refer to the following table to find out the best upgrade path.
| Vulnerable Version | Recommended Upgrade Path |
| 2.7 or earlier | Upgrade to 2.7.4 first, then to 3.5.17, and then follow the upgrade path listed below. |
| 2.8 to 3.4 | Upgrade to 3.5.17, and then follow the upgrade path listed below. |
| 3.5 | Upgrade to 5.0.3, and then to the latest Confluence 6. |
| 4.0 to 4.3 | Upgrade to 5.10.x, and then to the latest Confluence 6. |
| 5.0 to 6.x | Directly upgrade to the latest Confluence 6. |
Download appropriate installation packages of Confluence.
Confluence Server and Confluence Data Center:
https://www.atlassian.com/software/confluence/download
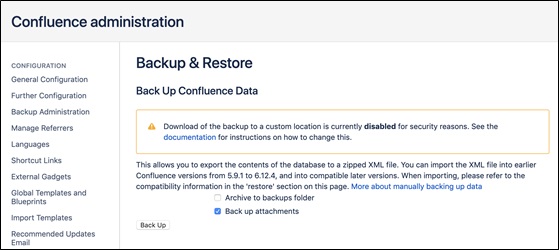
Back up data in case the upgrade fails.
- ‑Choose Configuration > Confluence Administration > Backup & Restore to back up confluence data.
- To ensure a complete backup of Confluence, users need to manually back up the following data:
- Database:
If the database does not support online backup, users need to first stop the Confluence service and then manually back up the database.
- Root directory:
| tar -cvf confluence-home-dir-backup.tar /atlassian/applicationdata/
confluence/ |
- Move routine backup files to another directory of the system:
| cd /disk/atlassian/application-data/confluence/backups/
cp backup.zip ~ |
- Installation directory:
| tar -cvf confluence-install-dir-backup.tar /atlassian/confluence/ |
Run the installation package by selecting 3 Upgrade an existing Confluence installation and performing the next step as prompted. The following uses the installation package of version 6.15.8 as an example.
| ./atlassian-confluence-6.15.8-x64.bin |
Restart Confluence.
| service confluence restart |
For more details and questions about the upgrade of Confluence, please visit https://www.cwiki.us/display/CONF6EN/Upgrading+Confluence.
-
Workarounds
If users cannot upgrade to the latest versions for the time being, the following temporary measures are recommended:
(1) After starting Confluence, change the value of atlassian.confluence.export.word.max.embedded.images from 50 to 0 to restrict export of images to Word documents.
(2) Check whether the workaround is effective: Create a page containing images, export it to a Word document, and then check whether the document contains images (after the preceding configuration, the document should not contain any images).
Note: This mitigation measure will result in images being unable to be exported to Word documents.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.