IP Reputation Report-12082019

dezembro 12, 2019
-
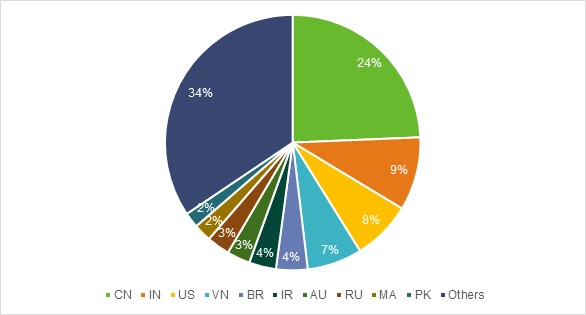
Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at December 08, 2019.
Cybersecurity Insights-8

dezembro 11, 2019
5.2 Web Attacks 5.2.1 Trend of Web Attacks Of all attacks targeting web servers in 2018, 89% of them still employed common methods such as server information disclosure, resource leech, SQL injection, and cross-site scripting. Hackers are using an increasing number of web server or plug-in vulnerabilities. In 2018, vulnerability based web attacks accounted for […]
Apache Flink Arbitrary Jar Package Upload Threat Alert
dezembro 10, 2019
Overview
Recently, researchers have discovered the Apache Flink Jar package to upload the attack data. Attackers can exploit this vulnerability to upload a Jar package containing malicious code without authorization, thereby taking control of the target server. (mais…)
Tracking and Analysis of the LoJack/CompuTrace Incident

dezembro 9, 2019
1. Introduction to LoJack
With a history of 20 years, Absolute Software has been a leading provider for device security, management, and tracking. Its products have set an industry standard for persistent endpoint security and data risk management for computers, laptops, tablets, and smartphones. In 2005, Absolute Software released LoJack for Loaptops, also known as Computrace. This software is used to trace stolen laptops, with features including the abilities to remotely lock, delete files from, and locate the stolen laptop on a map. (mais…)
NSFOCUS Assures Security for Commercial 5G Services

dezembro 6, 2019
NSFOCUS was invited to attend the China Information and Communication Industry Development Summit 2019 held in Beijing on October 30, 2019 and was awarded the “5G Innovation Enterprise” in this summit.
NSFOCUS assures security for commercial 5G services
IP Reputation Report-12012019

dezembro 5, 2019
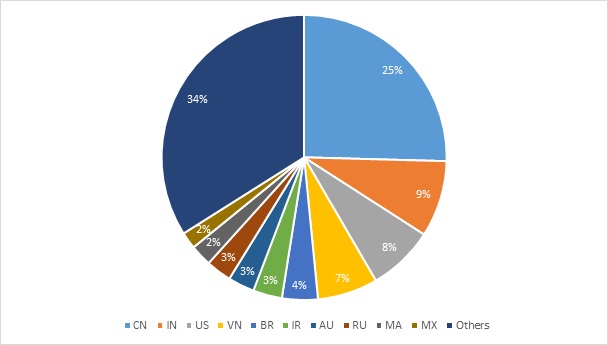
- Top 10 countries in attack counts:
- The above diagram shows the top 10 regions with the most malicious IP addresses from the NSFOCUS IP Reputation databases at December 01, 2019.
Cybersecurity Insights-7

dezembro 4, 2019
Insights into Malicious Traffic
5.1 Vulnerability Exploitation
Here we classify vulnerabilities into
- server vulnerabilities
- desktop application vulnerabilities
- device vulnerabilities
Apache Solr Remote Code Execution Vulnerability (CVE-2019-12409) Threat Alert

dezembro 3, 2019
Vulnerability Description On November 18, local time, Apache Software Foundation (ASF) released an official security bulletin to reveal a remote code execution vulnerability (CVE-2019-12409) in Apache Solr. This vulnerability exists and can bring security risks because the configuration item ENABLE_REMOTE_JMX_OPTS in the configuration file solr.in.sh is enabled by default. If you use the default configuration […]
Advisory: Apache Flink Remote Code Execution Vulnerability

dezembro 2, 2019
Overview
Recently, a security researcher announced a remote code execution vulnerability in Apache Flink Dashboard. The vulnerability does not require an attacker to authenticate, and a malicious Jar package can be uploaded via the dashboard to execute the code remotely. NSFOCUS researchers also made a successful re-enactment through research, confirming that they can attack the latest version of Flink. (mais…)
Advisory: Apache Shiro RememberMe Padding Oracle Vulnerability
novembro 30, 2019
Vulnerability Description
In September 2019, Apache officially released a vulnerability topic “RememberMe Padding Oracle Vulnerability” numbered SHIRO-721. The issue pointed out that because the RememberMe field of the Apache Shiro cookie is encrypted by the AES-128-CBC mode, Shiro is vulnerable to Padding Oracle attacks. An attacker can use the Legal RememberMe cookie as the Padding Oracle attack prefix to construct RememberMe to trigger a Java deserialization attack. The attacker does not need to know the RememberMe encryption key when executing an attack. Apache Shiro is a powerful and easy-to-use Java security framework for performing authentication, authorization, passwords, and session management. Recently, it has been found that the use of this vulnerability has been spread in a small scope, and relevant users should take measures to protect against this vulnerability as soon as possible. (mais…)