Overview
Recently, researchers have discovered the Apache Flink Jar package to upload the attack data. Attackers can exploit this vulnerability to upload a Jar package containing malicious code without authorization, thereby taking control of the target server.
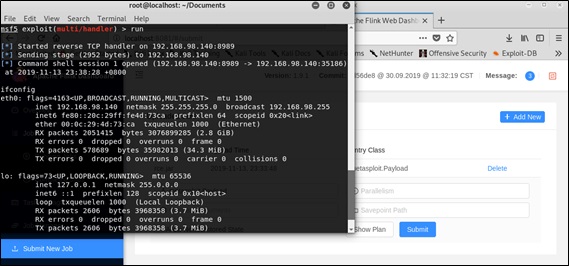
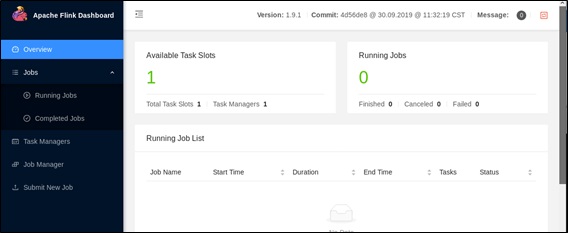
Apache Flink is an open-source stream-processing framework that can be used for processing streaming data in a distributed manner. It is widely used in the field of big data. Uploading Jar packages is a basic capability of Flink, but the Apache Flink Dashboard can be accessed without authentication by default. Therefore, if attackers detect that the target has an Apache Flink Dashboard, they can exploit this vulnerability to obtain server privileges. Successful exploitation is as follows:
Scope of Impact
Affected Versions
- Apache Flink <= 1.9.1
Note: Due to the functional characteristics of Flink, it is speculated that the security risk affects the full version. The NSFOCUS Security Alert Team has tested the latest version 1.9.1.
Detection Method
Version Detection
Users can check whether the current system is affected by checking the version. A user can enter the bin folder of the Flink installation directory and then executes the following command to view the current Flink version.
| ./flink –version |
The screenshot is as follows:
Risks exist if the current version is within the affected range.
Access Probe
Users can try to access the Dashboard using an unauthorized IP address. If the Dashboard is accessible, it indicates that related risks exist. The screenshot of a successful access is as follows:
Security Protection
Workarounds
Currently, the vendor has not provided a solution for fixing this vulnerability. Related users can take the following measures for temporary protection:
- Disable public access to Flink.
- Restrict access to port 8081 (default port of the Flink Dashboard) in intranets.
- Create an authentication policy for access to Flink.
Temporary protection advice
At present, the official fix for this threat has not been released yet, and relevant users can take the following temporary protection suggestions for protection:
- It is forbidden to open Flink to the public network.
- Restrict access to port 8081 (Flink Dashboard default port) on the intranet
- Add an authentication policy for Flink access
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.